Danger actors are leveraging digital doc publishing (DDP) web sites hosted on platforms like FlipSnack, Issuu, Marq, Publuu, RelayTo, and Simplebooklet for carrying out phishing, credential harvesting, and session token theft, at the time yet again underscoring how risk actors are repurposing legit expert services for malicious finishes.
“Hosting phishing lures on DDP web sites improves the likelihood of a thriving phishing attack, due to the fact these web-sites frequently have a favorable track record, are unlikely to seem on web filter blocklists, and may well instill a bogus feeling of security in consumers who acknowledge them as common or reputable,” Cisco Talos researcher Craig Jackson stated very last week.
While adversaries have applied popular cloud-based mostly companies this kind of as Google Push, OneDrive, Dropbox, SharePoint, DocuSign, and Oneflow to host phishing documents in the earlier, the hottest progress marks an escalation created to evade email security controls.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

DDP solutions allow for customers to add and share PDF information in a browser-centered interactive flipbook structure, adding page flip animations and other skeuomorphic effects to any catalog, brochure, or journal.
Danger actors have been found to abuse the free tier or a no-price trial period of time presented by these expert services to develop numerous accounts and publish destructive documents.
Other than exploiting their favorable domain status, the attackers acquire gain of the actuality that DDP web pages aid transient file hosting, thus making it possible for revealed content material to instantly turn into unavailable just after a predefined expiration day and time.
What is actually more, productiveness capabilities baked into DDP internet sites like Publuu could act as a deterrent, protecting against the extraction and detection of destructive backlinks in phishing messages.
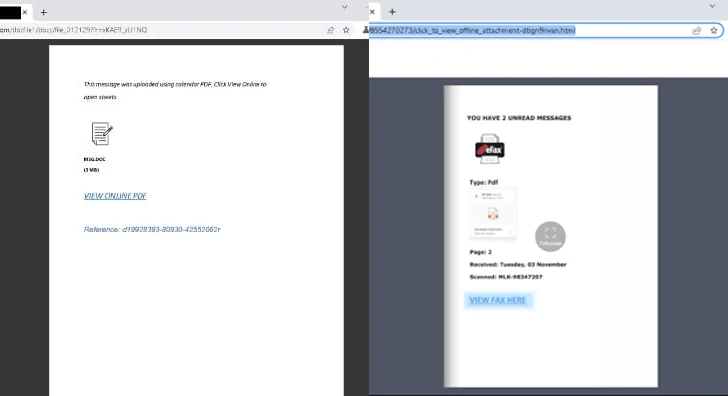
In the incidents analyzed by Cisco Talos, DDP sites are built-in into the attack chain in the secondary or intermediate stage, usually by embedding a url to a doc hosted on a authentic DDP web page in a phishing email.
The DDP-hosted doc serves as a gateway to an exterior, adversary-controlled internet site both directly by clicking on a backlink incorporated in the decoy file, or as a result of a series of redirects that also have to have resolving CAPTCHAs to thwart automatic evaluation initiatives.

The closing landing web page is a bogus web page mimicking the Microsoft 365 login web page, therefore allowing the attackers to steal qualifications or session tokens.
“DDP web-sites could signify a blind spot for defenders, simply because they are unfamiliar to skilled users and unlikely to be flagged by email and web information filtering controls,” Jackson mentioned.
“DDP internet sites generate pros for danger actors seeking to thwart modern day phishing protections. The exact capabilities and gains that draw in respectable customers to these web sites can be abused by menace actors to boost the efficacy of a phishing attack.”
Uncovered this posting attention-grabbing? Stick to us on Twitter and LinkedIn to go through far more special content material we write-up.
Some sections of this post are sourced from:
thehackernews.com


 Suspected Russian Data-Wiping ‘AcidPour’ Malware Targeting Linux x86 Devices
Suspected Russian Data-Wiping ‘AcidPour’ Malware Targeting Linux x86 Devices