A Golang implementation of Cobalt Strike identified as Geacon is possible to garner the attention of danger actors searching to concentrate on Apple macOS systems.
The conclusions appear from SentinelOne, which observed an uptick in the selection of Geacon payloads showing up on VirusTotal in latest months.
“Whilst some of these are very likely red-staff functions, many others bear the characteristics of genuine malicious attacks,” security researchers Phil Stokes and Dinesh Devadoss mentioned in a report.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Cobalt Strike is a well-recognised purple teaming and adversary simulation instrument formulated by Fortra. Owing to its myriad article-exploitation capabilities, illegally cracked versions of the application have been abused by menace actors about the many years.
Whilst write-up-exploitation exercise affiliated with Cobalt Strike has largely singled out Windows, this kind of attacks in opposition to macOS are anything of a rarity.

In Might 2022, software supply chain company Sonatype disclosed information of a rogue Python package named “pymafka” that was built to drop a Cobalt Strike Beacon onto compromised Windows, macOS, and Linux hosts.
That may possibly, however, modify with the emergence of Geacon artifacts in the wild. Geacon is a Go variant of Cobalt Strike that has been available on GitHub considering that February 2020.
Even more evaluation of two new VirusTotal samples that have been uploaded in April 2023 has traced their origins to two Geacon variants (geacon_as well as and geacon_pro) that had been formulated in late October by two nameless Chinese builders z3ratu1 and H4de5.
The geacon_pro undertaking is no for a longer period obtainable on GitHub, but an Internet Archive snapshot captured on March 6, 2023, reveals its skill to bypass antivirus engines these kinds of as Microsoft Defender, Kaspersky, and Qihoo 360 360 Main Crystal.
H4de5, the developer behind geacon_pro, claims the resource is largely built to aid CobaltStrike variations 4.1 and later on, when geacon_as well as supports CobaltStrike edition 4.. The present edition of the computer software is 4.8.
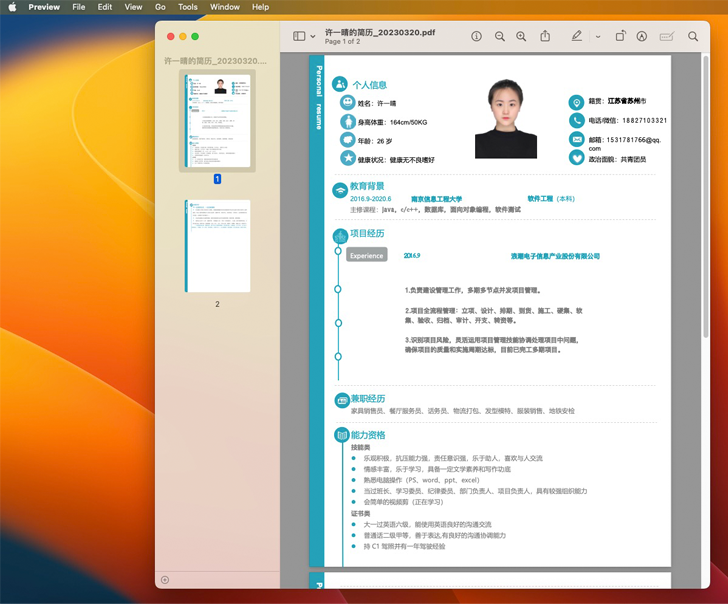
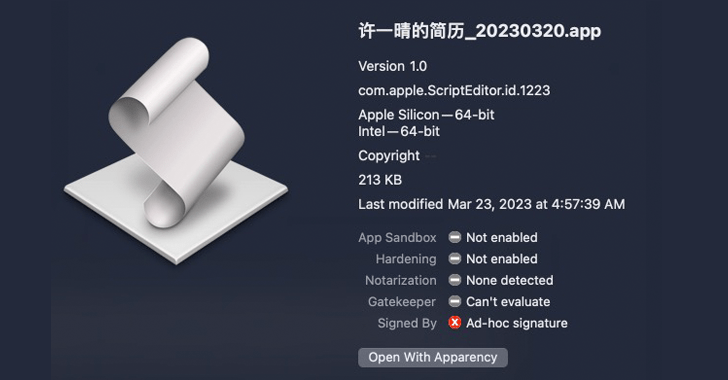
Xu Yiqing’s Resume_20230320.app, one particular of the artifacts found by SentinelOne, employs a operate-only AppleScript to achieve out to a distant server and obtain a Geacon payload. It is really suitable with both of those Apple silicon and Intel architectures.
“The unsigned Geacon payload is retrieved from an IP deal with in China,” the researchers reported. “In advance of it commences its beaconing action, the user is introduced with a two-webpage decoy doc embedded in the Geacon binary. A PDF is opened displaying a resume for an unique named ‘Xu Yiqing.'”
The Geacon binary, compiled from the geacon_furthermore supply code, packs a multitude of functions that enables it to download following-phase payloads and exfiltrate details, and aid network communications.
Upcoming WEBINARLearn to Cease Ransomware with Real-Time Safety
Be part of our webinar and study how to end ransomware attacks in their tracks with authentic-time MFA and provider account defense.
Preserve My Seat!
The 2nd sample, per the cybersecurity company, is embedded inside of a trojanized application that masquerades as the SecureLink distant support application (SecureLink.app) and primarily targets Intel gadgets.
The barebones, unsigned application requests for users’ permission to entry contacts, shots, reminders, as properly as the device’s digital camera and microphone. Its primary ingredient is a Geacon payload constructed from the geacon_pro venture that connects to a acknowledged command-and-manage (C2) server in Japan.
The improvement arrives as the macOS ecosystem is becoming focused by a extensive wide variety of threat actors, which include point out-sponsored teams, to deploy backdoors and information stealers.
“The uptick in Geacon samples around the previous number of months implies that security teams need to be paying out interest to this software and making certain that they have protections in location.”
Located this short article appealing? Follow us on Twitter and LinkedIn to browse more exclusive information we publish.
Some areas of this short article are sourced from:
thehackernews.com

 Qilin’s Dark Web Ransomware Targets Critical Sectors
Qilin’s Dark Web Ransomware Targets Critical Sectors