A new malware campaign has been observed utilizing delicate information stolen from a bank as a lure in phishing emails to drop a distant entry trojan called BitRAT.
The unknown adversary is thought to have hijacked the IT infrastructure of a Colombian cooperative bank, working with the information and facts to craft convincing decoy messages to entice victims into opening suspicious Excel attachments.
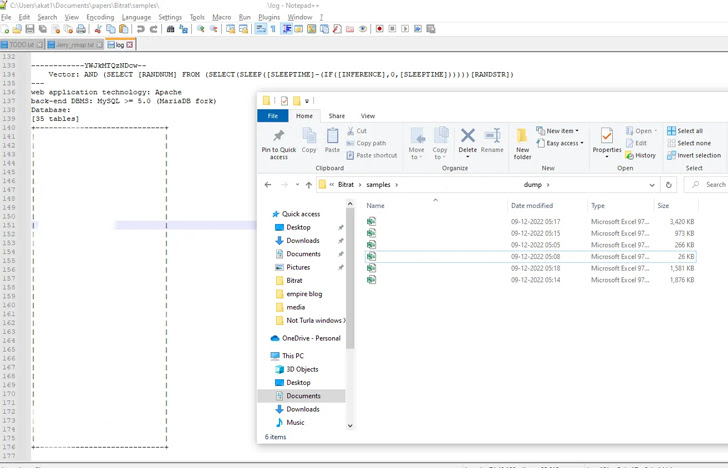
The discovery comes from cybersecurity organization Qualys, which identified evidence of a databases dump comprising 418,777 information which is explained to have been received by exploiting SQL injection faults.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The leaked details involve Cédula numbers (a countrywide identification document issued to Colombian citizens), email addresses, phone quantities, consumer names, payment data, wage details, and addresses, among others.
There are no indications that the info has been earlier shared on any forums in the darknet or apparent web, suggesting that the risk actors by themselves obtained obtain to customer knowledge to mount the phishing attacks.
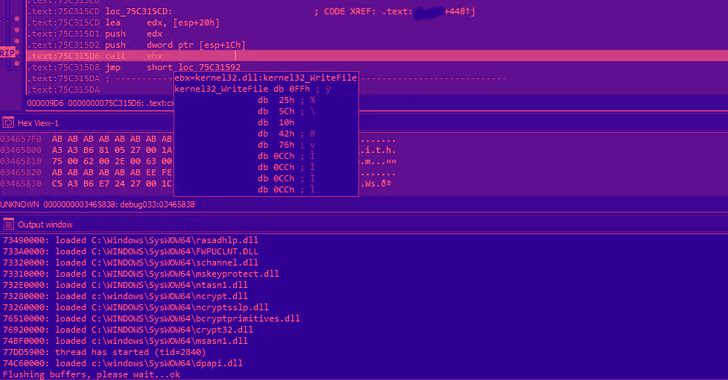
The Excel file, which contains the exfiltrated bank information, also embeds in it a macro that’s applied to obtain a 2nd-stage DLL payload, which is configured to retrieve and execute BitRAT on the compromised host.
“It makes use of the WinHTTP library to down load BitRAT embedded payloads from GitHub to the %temp% listing,” Qualys researcher Akshat Pradhan explained.
Established in mid-November 2022, the GitHub repository is utilized to host obfuscated BitRAT loader samples that are in the end decoded and launched to entire the infection chains.
BitRAT, an off-the-shelf malware offered on sale on underground boards for a mere $20, will come with a large vary of functionalities to steal info, harvest credentials, mine cryptocurrency, and obtain further binaries.
“Professional off the shelf RATs have been evolving their methodology to distribute and infect their victims,” Pradhan explained. “They have also elevated the usage of legit infrastructures to host their payloads and defenders need to account for it.”
Identified this article exciting? Adhere to us on Twitter and LinkedIn to read far more distinctive material we put up.
Some components of this report are sourced from:
thehackernews.com

 Offensive Security bans use of ChatGPT in cyber security certification exams
Offensive Security bans use of ChatGPT in cyber security certification exams