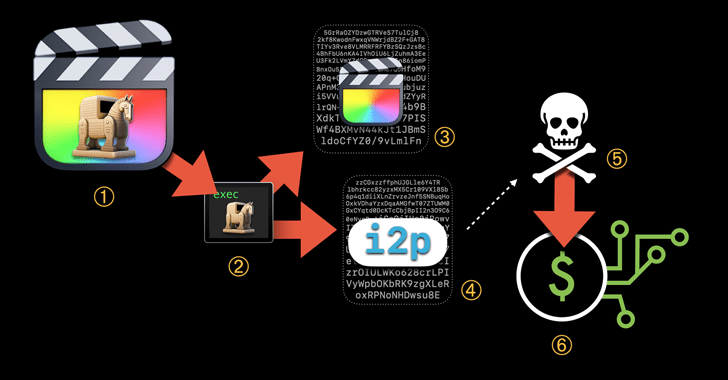
Trojanized versions of genuine applications are becoming made use of to deploy evasive cryptocurrency mining malware on macOS programs.
Jamf Risk Labs, which manufactured the discovery, said the XMRig coin miner was executed as Ultimate Minimize Pro, a video enhancing software program from Apple, which contained an unauthorized modification.
“This malware will make use of the Invisible Internet Task (i2p) […] to down load destructive parts and send out mined forex to the attacker’s wallet,” Jamf scientists Matt Benyo, Ferdous Saljooki, and Jaron Bradley stated in a report shared with The Hacker News.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
An previously iteration of the marketing campaign was documented specifically a year ago by Pattern Micro, which pointed out the malware’s use of i2p to conceal network site visitors and speculated that it could have been shipped as a DMG file for Adobe Photoshop CC 2019.
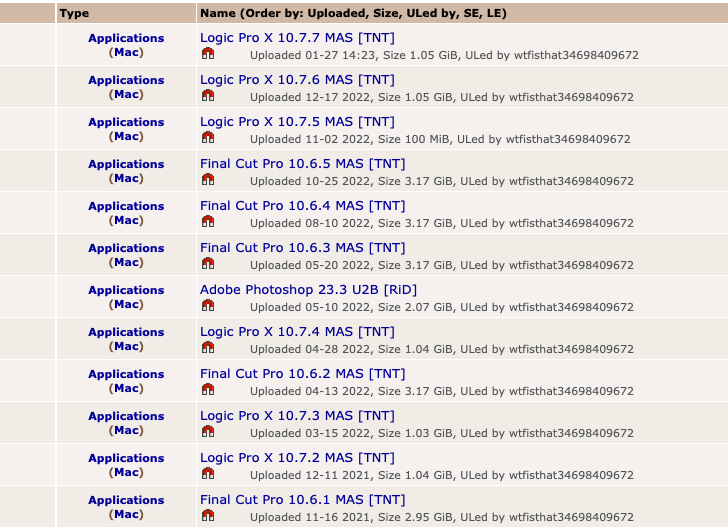
The Apple product management corporation reported the supply of the cryptojacking applications can be traced to Pirate Bay, with the earliest uploads relationship all the way again to 2019.
The consequence is the discovery of 3 generations of the malware, noticed initial in August 2019, April 2021, and Oct 2021, that charts the evolution of the campaign’s sophistication and stealth.
One illustration of the evasion method is a shell script that screens the checklist of working processes to check for the existence of Exercise Monitor, and if so, terminate the mining processes.
The malicious mining procedure banking companies on the person launching the pirated software, on which the code embedded in the executable connects to an actor-controlled server around i2p to down load the XMRig ingredient.
The malware’s capability to fly underneath the radar, coupled with the fact that end users jogging cracked computer software are willingly executing anything unlawful, has designed the distribution vector a extremely productive one particular for several decades.
Apple, nonetheless, has taken actions to beat this sort of abuse by subjecting notarized apps to more stringent Gatekeeper checks in macOS Ventura, therefore blocking tampered apps from becoming released.
“On the other hand, macOS Ventura did not avoid the miner from executing,” Jamf researchers famous. “By the time the user gets the mistake information, that malware has presently been mounted.”
“It did reduce the modified edition of Final Slice Pro from launching, which could increase suspicion for the user as very well as significantly lessen the chance of subsequent launches by the consumer.”
Identified this short article fascinating? Comply with us on Twitter and LinkedIn to read through more exclusive content we submit.
Some sections of this short article are sourced from:
thehackernews.com

 Dozens of Malicious ‘HTTP’ Libraries Found on PyPI
Dozens of Malicious ‘HTTP’ Libraries Found on PyPI