A number of substantial-severity security vulnerabilities have been disclosed in ConnectedIO’s ER2000 edge routers and the cloud-based administration platform that could be exploited by destructive actors to execute destructive code and entry sensitive details.
“An attacker could have leveraged these flaws to absolutely compromise the cloud infrastructure, remotely execute code, and leak all purchaser and device info,” Claroty’s Noam Moshe reported in an analysis posted previous week.
Vulnerabilities in 3G/4G routers could expose thousands of inside networks to serious threats, enabling undesirable actors to seize manage, intercept targeted visitors, and even infiltrate Prolonged Internet of Matters (XIoT) points.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The shortcomings impacting the ConnectedIO platform versions v2.1. and prior, mostly the 4G ER2000 edge router and cloud products and services, could be chained, permitting attackers to execute arbitrary code on the cloud-dependent devices without the need of necessitating direct access to them.
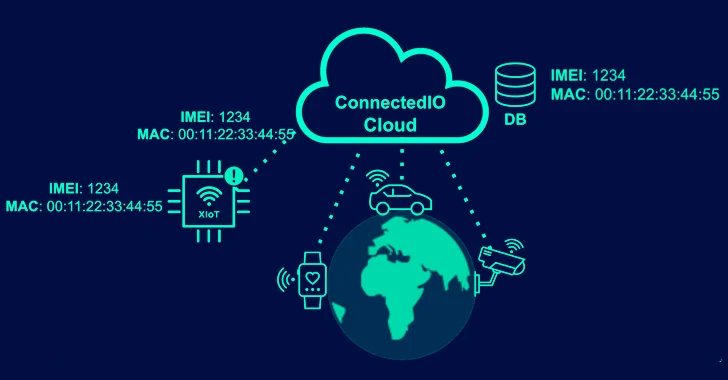
Flaws have also been unearthed in the conversation protocol (i.e., MQTT) used between the products and the cloud, including the use of difficult-coded authentication credentials, that could be employed to sign up a rogue system and accessibility MQTT messages containing device identifiers, Wi-Fi settings, SSIDs, and passwords from routers.
A consequence of the vulnerabilities is that a danger actor could not only impersonate any device of their selection utilizing the leaked IMEI numbers, but also force them to execute arbitrary instructions printed through specially crafted MQTT messages.

This is built attainable as a result of a bash command with the opcode “1116,” which executes a remote command “as-is.”
“This command, which does not need any other variety of authentication other than becoming ready to write it to the appropriate subject, will allow us to execute arbitrary instructions on all products,” Moshe discussed.
“It lacks validation that the sender of the commands is really an licensed issuer. Using this command opcode, we were being able to create a payload that will outcome in code execution every time it is sent to a machine.”
The issues have been assigned the next CVE identifiers –
- CVE-2023-33375 (CVSS rating: 8.6) – A stack-based mostly buffer overflow vulnerability in its conversation protocol, enabling attackers to consider manage more than equipment.
- CVE-2023-33376 (CVSS rating: 8.6) – An argument injection vulnerability in its ip tables command concept in its interaction protocol, enabling attackers to execute arbitrary OS instructions on products.
- CVE-2023-33377 (CVSS rating: 8.6) – An working process command injection vulnerability in the established firewall command in element of its communication protocol, enabling attackers to execute arbitrary OS commands on units.
- CVE-2023-33378 (CVSS rating: 8.6) – An argument injection vulnerability in its AT command information in its interaction protocol, enabling attackers to execute arbitrary OS instructions on products.
“These vulnerabilities, if exploited, could pose major risk for hundreds of organizations around the entire world, permitting attackers to disrupt the companies’ business enterprise and generation, along with offering them obtain to the companies’ internal networks,” Moshe claimed.

The disclosure arrives as the organization also unveiled a handful of flaws in network-attached storage (NAS) equipment from Synology and Western Electronic that could be weaponized to impersonate and command them, as nicely as steal saved information and redirect customers to an attacker-controlled unit.
It also follows the discovery of a few unpatched vulnerabilities impacting Baker Hughes’ Bently Nevada 3500 rack product that could be used to bypass the authentication method and attain full access to the system and .
“In the most extreme state of affairs, these flaws could allow an attacker to completely compromise the device and alter its interior configuration, perhaps main to either incorrect measurements from monitored equipment, or denial-of-services attacks,” Nozomi Networks claimed.
Discovered this posting interesting? Abide by us on Twitter and LinkedIn to read additional special material we post.
Some areas of this write-up are sourced from:
thehackernews.com

 Security Patch for Two New Flaws in Curl Library Arriving on October 11
Security Patch for Two New Flaws in Curl Library Arriving on October 11