The danger actors at the rear of the Hive ransomware-as-a-assistance (RaaS) plan have released attacks from about 1,300 corporations throughout the world, netting the gang $100 million in illicit payments as of November 2022.
“Hive ransomware has focused a extensive variety of businesses and critical infrastructure sectors, such as authorities facilities, communications, critical producing, facts technology, and — specially — Health care and Community Health (HPH),” U.S. cybersecurity and intelligence authorities stated in an inform.
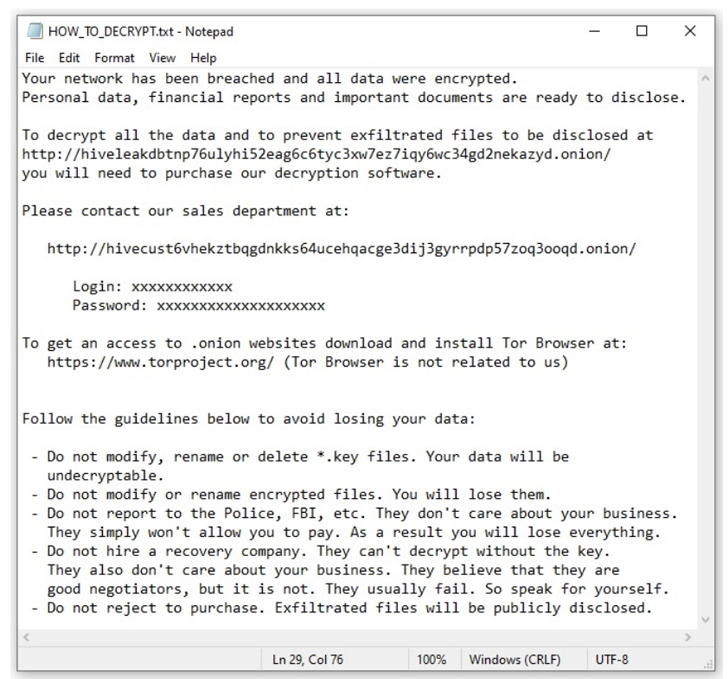
Energetic since June 2021, Hive’s RaaS operation includes a blend of developers, who build and control the malware, and affiliates, who are dependable for conducting the attacks on focus on networks by often purchasing first entry from initial accessibility brokers (IABs).

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
In most circumstances, getting a foothold requires the exploitation of ProxyShell flaws in Microsoft Trade Server, adopted by having methods to terminate procedures associated with antivirus engines and info backups as properly as delete Windows event logs.
The threat actor, which lately upgraded its malware to Rust as a detection evasion evaluate, is also recognized to clear away virus definitions prior to encryption.
“Hive actors have been known to reinfect—with possibly Hive ransomware or yet another ransomware variant—the networks of victim corporations who have restored their network with no building a ransom payment,” the U.S. Cybersecurity and Infrastructure Security Company (CISA) mentioned.
According to details shared by cybersecurity organization Malwarebytes, Hive compromised about seven victims in August 2022, 14 in September, and two other entities in Oct, marking a drop in activity from July, when the group targeted 26 victims.
Discovered this article fascinating? Comply with THN on Fb, Twitter and LinkedIn to read more distinctive content we put up.
Some parts of this write-up are sourced from:
thehackernews.com


 W4SP Stealer Constantly Targeting Python Developers in Ongoing Supply Chain Attack
W4SP Stealer Constantly Targeting Python Developers in Ongoing Supply Chain Attack