A new analysis of the Android banking trojan identified as Hook has uncovered that it can be primarily based on its predecessor called ERMAC.
“The ERMAC resource code was applied as a foundation for Hook,” NCC Team security researchers Joshua Kamp and Alberto Segura reported in a technical analysis printed last 7 days.
“All commands (30 in complete) that the malware operator can send out to a unit contaminated with ERMAC malware, also exist in Hook. The code implementation for these instructions is approximately equivalent.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
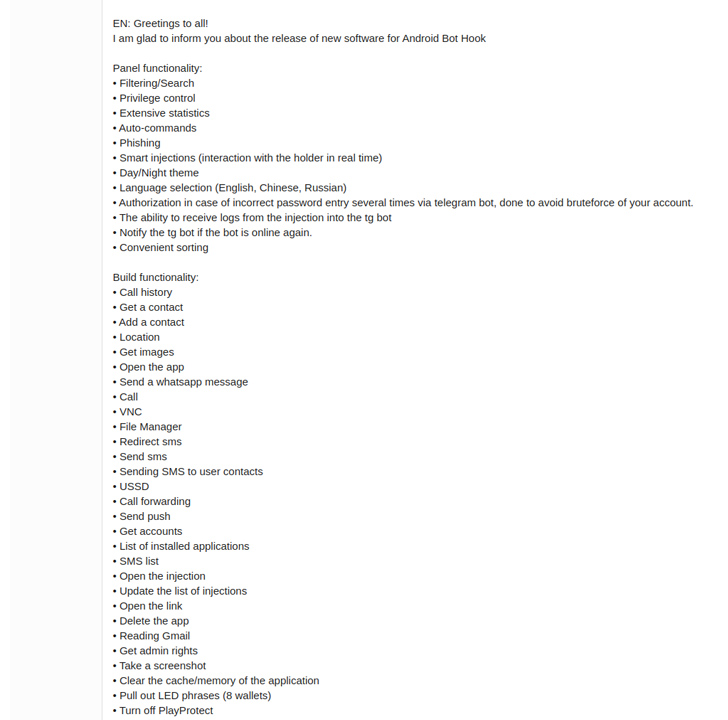
Hook was initially documented by ThreatFabric in January 2023, describing it as a “ERMAC fork” that is supplied for sale for $7,000 for each thirty day period. Equally the strains are the get the job done of a malware author known as DukeEugene.
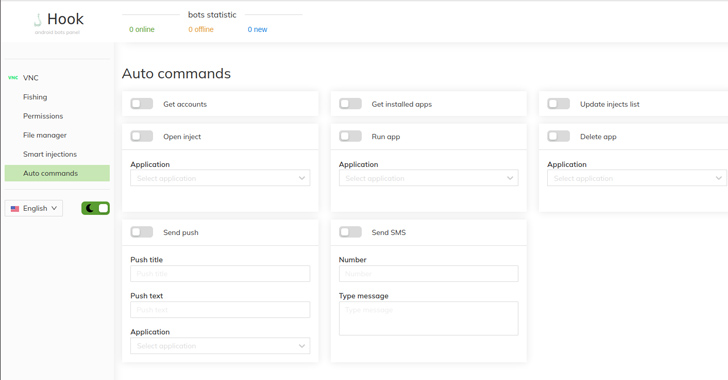
That reported, Hook expands on ERMAC’s functionalities with far more capabilities, supporting as quite a few as 38 extra commands when in comparison to the latter.
ERMAC’s core functions are developed to send out SMS messages, exhibit a phishing window on top rated of a genuine application, extract a listing of installed programs, assemble SMS messages, and siphon restoration seed phrases for a number of cryptocurrency wallets.

Hook, on the other hand, goes a move more by streaming the victim’s monitor and interacting with the user interface to achieve full management around an infected unit, capturing photographs of the target working with the front dealing with digicam, harvesting cookies related to Google login classes, and plundering recovery seeds from much more crypto wallets.
It can more send out an SMS concept to various phone numbers, effectively propagating the malware to other buyers.
Irrespective of these differences, each Hook and ERMAC can log keystrokes and abuse Android’s accessibility providers to perform overlay attacks in buy to display screen articles on best of other applications and steal qualifications from in excess of 700 applications. The record of apps to concentrate on is retrieved on the fly by way of a request to a remote server.
The malware family members are also engineered to monitor for clipboard functions and swap the content with an attacker-controlled wallet must the sufferer duplicate a authentic wallet deal with.
A the greater part of Hook and ERMAC’s command-and-management (C2) servers are found in Russia, followed by the Netherlands, the U.K., the U.S., Germany, France, Korea, and Japan.
As of April 19, 2023, it seems that the Hook project has been shuttered, according to a post shared by DukeEugene, who claimed to be leaving for a “distinctive military procedure” and that help for the computer software would be delivered by another actor named RedDragon till the customers’ membership operates out.
Subsequently, on May 11, 2023, the supply code for Hook is reported to have been bought by RedDragon for $70,000 on an underground forum. The brief lifespan of Hook apart, the progress has lifted the possibility that other danger actors could decide on up the operate and launch new variants in the potential.
The disclosure will come as a China-nexus threat actor has been connected to an Android spy ware campaign targeting people in South Korea considering that the beginning of July 2023.
“The malware is distributed by means of misleading phishing internet websites that pose as adult internet sites but truly provide the malicious APK file,” Cyble said. “When the malware has contaminated the victim’s equipment, it can steal a huge range of delicate information and facts, which includes contacts, SMS messages, call logs, pictures, audio information, display screen recordings, and screenshots.”
Impending WEBINARIdentity is the New Endpoint: Mastering SaaS Security in the Modern-day Age
Dive deep into the long run of SaaS security with Maor Bin, CEO of Adaptive Protect. Find why identity is the new endpoint. Secure your place now.
Supercharge Your Capabilities
On best of that, the malware (APK offer identify “com.example.middlerankapp”) can take benefit of accessibility expert services to monitor the apps utilized by the victims and prevent uninstallation.
It also consists of a element that enables the malware to redirect incoming phone calls to a designated mobile amount managed by the attacker, intercept SMS messages, and include an unfinished keylogging features, indicating it can be possible in lively growth.
The connections to China stem from references to Hong Kong in the WHOIS history details for the C2 server as well as the existence of a number of Chinese language strings, like “中国共产党万岁,” in the malware source code, which translates to “Prolonged reside the Communist Party of China.”
In a associated progress, Israeli newspaper Haaretz revealed that a domestic spyware firm Insanet has produced a merchandise termed Sherlock that can infect equipment through on the internet ads to snoop on targets and collect sensitive information from Android, iOS, and Windows systems.
The program is said to have been sold to a region that’s not a democracy, it described, introducing a amount of Israeli cyber businesses have tried to build offensive technology that exploits advertisements for profiling victims (a term identified as AdInt or advert intelligence) and distributing spyware.
Discovered this short article intriguing? Stick to us on Twitter and LinkedIn to browse much more special information we publish.
Some pieces of this article are sourced from:
thehackernews.com

 Retool Falls Victim to SMS-Based Phishing Attack Affecting 27 Cloud Clients
Retool Falls Victim to SMS-Based Phishing Attack Affecting 27 Cloud Clients