Numerous security vulnerabilities have been disclosed in cloud management platforms connected with a few industrial mobile router distributors that could expose operational technology (OT) networks to external attacks.
The conclusions were being introduced by Israeli industrial cybersecurity business OTORIO at the Black Hat Asia 2023 convention final week.
The 11 vulnerabilities permit “remote code execution and total regulate more than hundreds of hundreds of units and OT networks – in some scenarios, even all those not actively configured to use the cloud.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Exclusively, the shortcomings reside in the cloud-dependent management methods available by Sierra Wi-fi, Teltonika Networks, and InHand Networks to remotely regulate and work units.

Thriving exploitation of the vulnerabilities could pose intense pitfalls to industrial environments, permitting adversaries to sidestep security layers as very well as exfiltrate delicate facts and attain code execution remotely on the internal networks.
Even even worse, the issues could be weaponized to receive unauthorized entry to products in the network and complete destructive operations such as shutdown with elevated permissions.
This, in switch, is designed attainable owing to three unique attack vectors that could be exploited to compromise and takeover cloud-managed IIoT products by means of their cloud-dependent management platforms:
- Weak asset registration mechanisms (Sierra Wireless): An attacker could scan for unregistered units that are connected to the cloud, get their serial quantities by getting advantage of the AirVantage online Warranty Checker tool, register them to an account beneath their regulate, and execute arbitrary commands.
- Flaws in security configurations (InHand Networks): An unauthorized user could leverage CVE-2023-22601, CVE-2023-22600, and CVE-2023-22598, a command injection flaw, to obtain distant code execution with root privileges, issue reboot commands, and thrust firmware updates.
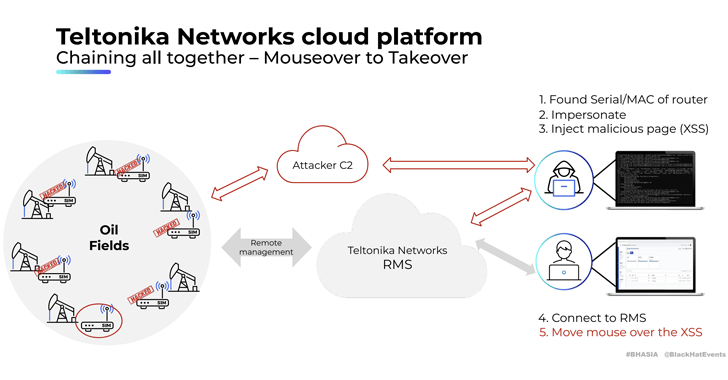
- Exterior API and interfaces (Teltonika Networks): A menace actor could abuse several issues identified in the remote administration method (RMS) to “expose delicate device facts and unit qualifications, enable distant code execution, expose related equipment managed on the network, and let impersonation of genuine equipment.”
The six flaws impacting Teltonika Networks – CVE-2023-32346, CVE-2023-32347, CVE-2023-32348, CVE-2023-2586, CVE-2023-2587, and CVE-2023-2588 – ended up uncovered next a “extensive exploration” carried out in collaboration with Claroty.
Approaching WEBINARLearn to Cease Ransomware with Genuine-Time Defense
Join our webinar and find out how to stop ransomware attacks in their tracks with true-time MFA and services account safety.
Preserve My Seat!
“An attacker successfully exploiting these industrial routers and IoT gadgets can bring about a selection of impacts on compromised devices and networks, like monitoring network traffic and thieving sensitive data, hijacking internet connections and accessing inner providers,” the corporations claimed.
OTORIO said cloud-managed units pose a “substantial” supply-chain risk and that a single seller compromise can act as a backdoor for accessing a number of OT networks in a person sweep.
The growth arrives a tiny additional than 3 months just after the cybersecurity enterprise disclosed 38 security flaws in the wi-fi industrial Internet of Issues (IIoT) gadgets that could supply attackers a immediate path to inner OT networks and place critical infrastructure at risk.
“As the deployment of IIoT equipment gets to be a lot more well known, it is important to be aware that their cloud administration platforms may well be qualified by threat actors,” security researcher Roni Gavrilov stated. “A solitary IIoT vendor platform being exploited could act as a ‘pivot point’ for attackers, accessing countless numbers of environments at once.”
Discovered this post fascinating? Comply with us on Twitter and LinkedIn to go through much more distinctive information we publish.
Some pieces of this article are sourced from:
thehackernews.com

 New Ransomware Gang RA Group Hits U.S. and South Korean Organizations
New Ransomware Gang RA Group Hits U.S. and South Korean Organizations