Cybersecurity researchers now uncovered new aspects of watering gap assaults against the Kurdish community in Syria and Turkey for surveillance and intelligence exfiltration functions.
The superior persistent risk powering the procedure, termed StrongPity, has retooled with new methods to manage compromised machines, cybersecurity firm Bitdefender claimed in a report shared with The Hacker News.
“Making use of watering gap techniques to selectively infect victims and deploying a a few-tier C&C infrastructure to thwart forensic investigations, the APT team leveraged Trojanized popular instruments, these kinds of as archivers, file recovery programs, remote connections apps, utilities, and even security software package, to include a broad vary of alternatives that targeted victims could be looking for,” the researchers stated.
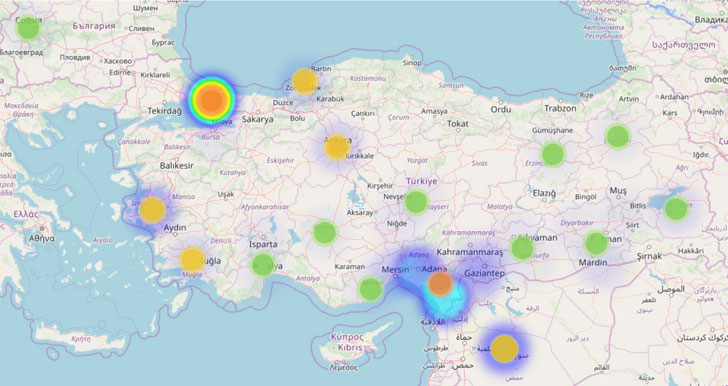
With the timestamps of the analyzed malware samples made use of in the marketing campaign coinciding with the Turkish offensive into north-eastern Syria (codenamed Procedure Peace Spring) very last Oct, Bitdefender reported the assaults could have been politically motivated.
Working with Tainted Installers to Drop Malware
StrongPity (or Promethium) was 1st publicly described on in Oct 2016 after assaults towards people in Belgium and Italy that employed watering holes to deliver destructive versions of WinRAR and TrueCrypt file encryption software package.
Because then, the APT has been joined to a 2018 procedure that abused Türk Telekom’s network to redirect hundreds of buyers in Turkey and Syria to destructive StrongPity versions of reliable application.
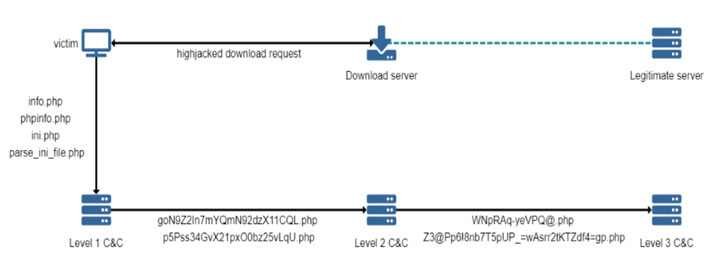
Consequently when the qualified end users try to download a respectable software on the formal web-site, a watering hole attack or an HTTP redirect is carried out to compromise the units.
Final July, AT&T Alien Labs uncovered proof of a new adware marketing campaign that exploited trojanized versions of WinBox router management software program and WinRAR file archiver to put in StrongPity and converse with the adversary infrastructure.
The new assault process discovered by Bitdefender stays the identical: focus on victims in Turkey and Syria working with predefined IP listing by leveraging tampered installers — including McAfee Safety Scan In addition, Recuva, TeamViewer, WhatsApp, and Piriform’s CCleaner — hosted on localized software aggregates and sharers.
“Apparently, all documents investigated pertaining to the tainted programs appear to have been compiled from Monday to Friday, during standard 9 to 6 UTC+2 doing the job hours,” the scientists mentioned. “This strengthens the thought that StrongPity could be a sponsored and organized developer staff paid out to deliver particular ‘projects.'”
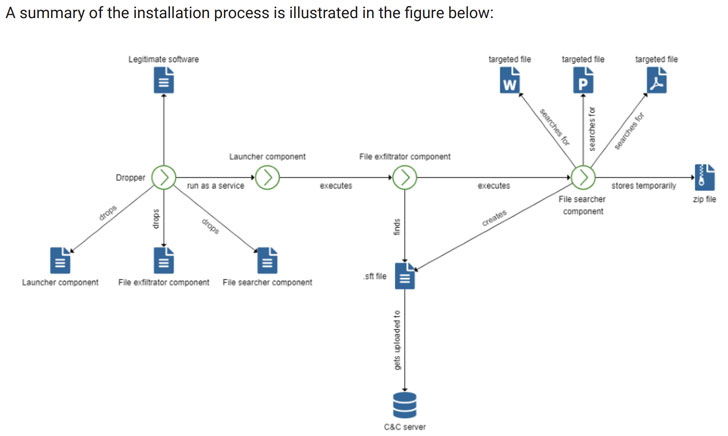
When the malware dropper is downloaded and executed, the backdoor is set up, which establishes conversation with a command and regulate server for doc exfiltration and for retrieving commands to be executed.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
It also deploys a “File Searcher” part on the victim’s machine that loops via every single travel and seems for data files with distinct extensions (e.g., Microsoft Business documents) to be exfiltrated in the kind of a ZIP archive.
This ZIP file is then break up into several hidden “.sft” encrypted documents, sent to the C&C server, and eventually deleted from the disk to go over any tracks of the exfiltration.
Increasing Further than Syria and Turkey
Though Syria and Turkey could be their recurring targets, the menace actor behind StrongPity seems to be growing their victimology to infect users in Colombia, India, Canada, and Vietnam employing tainted versions of Firefox, VPNpro, DriverPack, and 5kPlayer.
Contacting it StrongPity3, Cisco Talos researchers yesterday described an evolving malware toolkit that employs a module known as “winprint32.exe” to start the doc look for and transmit the gathered information. What is actually a lot more, the faux Firefox installer also checks if both ESET or BitDefender antivirus software package is set up prior to dropping the malware.
“These characteristics can be interpreted as indicators that this menace actor could in fact be section of an company company for seek the services of procedure,” the scientists stated. “We consider this has hallmarks a professionally packaged alternative owing to the similarity of each piece of malware becoming particularly very similar but utilised across diverse targets with small alterations.”
Uncovered this post appealing? Comply with THN on Facebook, Twitter and LinkedIn to read through much more exclusive information we post.

 Tuesday’s Magento 1 EOL Leaves Clock Ticking on 100K On line Merchants
Tuesday’s Magento 1 EOL Leaves Clock Ticking on 100K On line Merchants