Cybersecurity scientists took the wraps off however a further instance of Android malware concealed below the guise of legitimate programs to stealthily subscribe unsuspecting users for premium services without the need of their know-how.
In a report printed by Verify Place investigate today, the malware — infamously termed Joker (or Bread) — has discovered another trick to bypass Google’s Engage in Shop protections: obfuscate the destructive DEX executable inside of the application as Base64 encoded strings, which are then decoded and loaded on the compromised gadget.
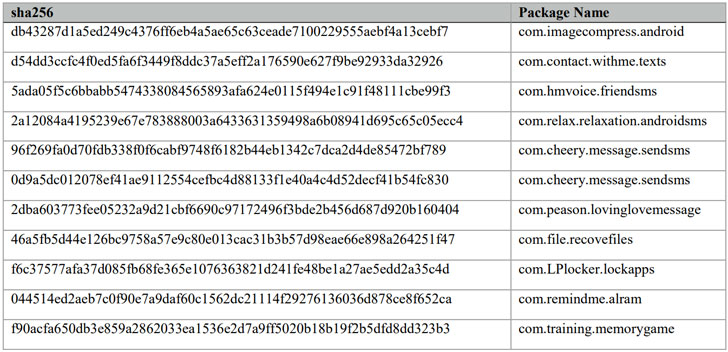
Subsequent dependable disclosure by Check Position researchers, the 11 apps (checklist and hashes right here) in problem have been taken out by Google from the Perform Retail outlet on April 30, 2020.
“The Joker malware is difficult to detect, inspite of Google’s financial investment in incorporating Participate in Retailer protections,” said Check Point’s Aviran Hazum, who identified the new modus operandi of Joker malware. “Although Google taken off the malicious apps from the Play Retailer, we can totally hope Joker to adapt once more.”
Joker: A Massive-Scale Billing Fraud Family
First uncovered in 2017, Joker is one of the most widespread types of Android malware, infamous for perpetrating billing fraud and its adware abilities, which includes thieving SMS messages, make contact with lists, and device information and facts.
Campaigns involving Joker received additional foothold previous yr, with a number of malware-contaminated Android applications uncovered by CSIS Stability Team, Development Micro, Dr.Website, and Kaspersky, repeatedly getting exclusive strategies to exploit gaps in Enjoy Keep safety checks.
To mask their genuine nature, the malware authors guiding the large-scale procedure have resorted to a selection of approaches — encryption to hide strings from examination engines, pretend critiques to entice end users into downloading the apps, and a approach named versioning, which refers to uploading a thoroughly clean variation of the application to the Play Retail outlet to build trust amongst end users and then sneakily adding malicious code at a afterwards phase by means of app updates.
“As the Perform Retail outlet has introduced new procedures and Google Engage in Protect has scaled defenses, Bread applications were compelled to continually iterate to research for gaps,” Android’s Safety & Privacy Team stated previously this yr. “They have at some issue utilized just about each cloaking and obfuscation method below the solar in an attempt to go undetected.”
As of January 2020, Google has eliminated extra than 1,700 apps submitted to the Participate in Retail outlet above the previous a few a long time that experienced been contaminated with the malware.
Applying Android Manifest to Cover Malicious DEX File


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The new variant noticed by Look at Level has the similar aim but goes about it by leveraging the app’s manifest file, which it works by using to load a Foundation64 encoded DEX file.
A 2nd “in-in between” variation recognized by Look at Point employs a similar procedure of hiding the .dex file as Foundation64 strings but adds them as an inner course in the major application and masses it by way of reflection APIs.
“To reach the ability of subscribing the consumers to quality solutions with out their awareness or consent, the Joker utilized two main elements — the Notification Listener as a aspect of the original software, and a dynamic dex file loaded from the C&C server to perform the registration,” Hazum noted in his evaluation.
Furthermore, the variant arrives geared up with a new feature that lets the danger actor to remotely situation a “wrong” position code from a C&C server under their management to suspend the malicious action.
If anything at all, the most current Joker plan signifies fewer of a important menace than it does a reminder of how Android malware is constantly evolving and has to be protected consistently.
For customers who’ve installed any of the contaminated applications, it is really worth examining your cell and transaction historical past to see if there are any suspicious payments that you really don’t recognize. Also, make guaranteed to very carefully scrutinize your permissions for just about every app set up on your Android device.
Identified this posting fascinating? Adhere to THN on Fb, Twitter and LinkedIn to browse a lot more exceptional material we post.


 The Incident Response Challenge 2020 — Results and Solutions Announced
The Incident Response Challenge 2020 — Results and Solutions Announced