An ongoing examination of the KmsdBot botnet has lifted the chance that it’s a DDoS-for-use support presented to other risk actors.
This is dependent on the various industries and geographies that were attacked, web infrastructure corporation Akamai explained. Between the notable targets incorporated FiveM and RedM, which are video game modifications for Grand Theft Car V and Pink Lifeless Redemption 2, as very well as luxurious brands and security corporations.
KmsdBot is a Go-dependent malware that leverages SSH to infect units and carry out activities like cryptocurrency mining and start instructions employing TCP and UDP to mount dispersed denial-of-assistance (DDoS) attacks.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

However, a lack of an mistake-examining mechanism in the botnet resource code caused the malware operators to inadvertently crash their individual botnet previous month.
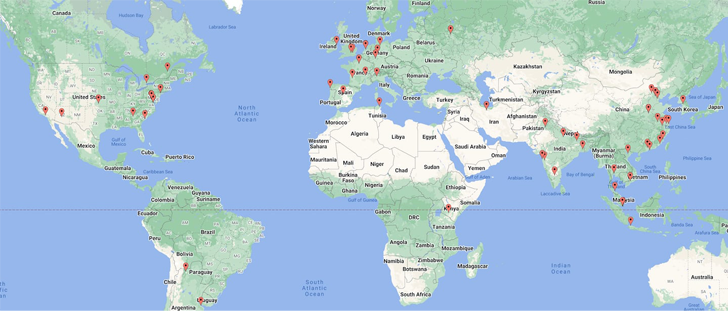
“Based on noticed IPs and domains, the greater part of the victims are found in Asia, North America, and Europe,” Akamai researchers Larry W. Cashdollar and Allen West stated. “The existence of these instructions tracks with former observations of qualified gaming servers and delivers a glimpse into the prospects of this botnet for use.”
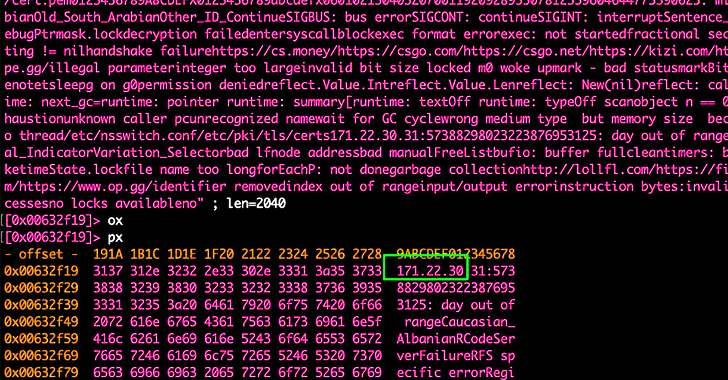
Akamai, which examined the attack traffic, recognized 18 different commands that KmsdBot accepts from a remote server, one of which, dubbed “bigdata,” caters to sending junk packets containing substantial quantities of facts to a focus on in an endeavor to exhaust its bandwidth.
Also incorporated are commands such as “fivem” and “redm” that are built to target online video recreation mod servers, alongside a “scan” instruction that “appears to target particular paths inside of the focus on surroundings.”
Charting the infection makes an attempt of the botnet signals small exercise in the Russian territory and neighboring locations, possibly providing a clue as to its origins.
A additional breakdown of the attack commands observed about a 30-working day time period of time exhibits “bigdata” leading with a frequency of more than 70 instances. Phone calls to “fivem” have happened 45 occasions, though “redm” has noticed less than 10 calls.
“This tells us that even though gaming servers are a precise target provided, it could not be the only field that is being strike with these attacks,” the researchers mentioned. “Help for numerous types of servers raises the in general usability of this botnet and appears to be powerful in driving in consumers.”
The findings arrive a week after Microsoft in depth a cross-system botnet identified as MCCrash that comes with capabilities to carry out DDoS attacks from private Minecraft servers.
Discovered this post exciting? Stick to us on Twitter and LinkedIn to study more special content material we submit.
Some areas of this write-up are sourced from:
thehackernews.com

 Apple issues patch for macOS security bypass vulnerability
Apple issues patch for macOS security bypass vulnerability