A new malvertising marketing campaign has been observed distributing an current edition of a macOS stealer malware referred to as Atomic Stealer (or AMOS), indicating that it truly is remaining actively taken care of by its author.
An off-the-shelf Golang malware readily available for $1,000 for every thirty day period, Atomic Stealer first arrived to light-weight in April 2023. Shortly soon after that, new variants with an expanded set of information-accumulating functions had been detected in the wild, focusing on avid gamers and cryptocurrency buyers.
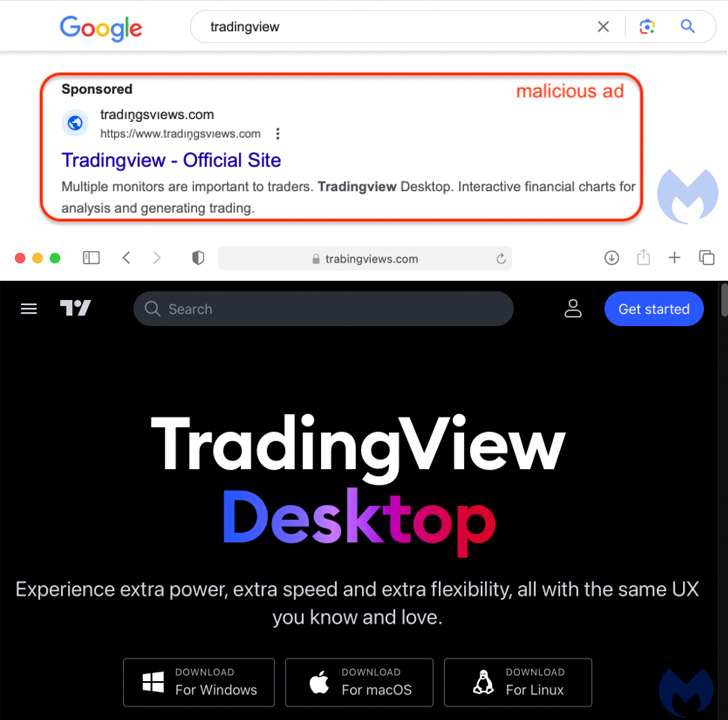
Malvertising by means of Google Ads has been observed as the primary distribution vector in which buyers searching for well-known software, authentic or cracked, on lookup engines are shown bogus adverts that immediate to internet websites hosting rogue installers.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The most up-to-date campaign includes the use of a fraudulent website for TradingView, prominently showcasing three buttons to down load the program for Windows, macOS, and Linux functioning methods.

“Both the Windows and Linux buttons point to an MSIX installer hosted on Discord that drops NetSupport RAT,” Jérôme Segura, director of menace intelligence at Malwarebytes, reported.
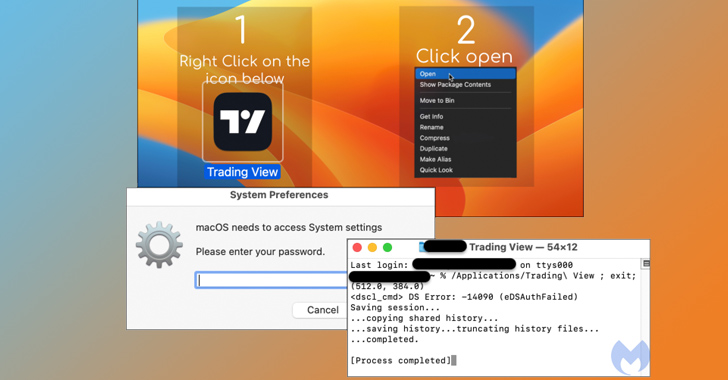
The macOS payload (“TradingView.dmg”) is a new edition of Atomic Stealer produced at the stop of June, which is bundled in an advert-hoc signed application that, when executed, prompts end users to enter their password on a bogus prompt and harvest documents as well as information saved in iCloud Keychain and web browsers.
“Atomic stealer also targets both Chrome and Firefox browsers and has an comprehensive hardcoded list of crypto-relevant browser extensions to attack,” SentinelOne earlier pointed out in May perhaps 2023. Choose variants have also qualified Coinomi wallets.
The best objective of the attacker is to bypass Gatekeeper protections in macOS and exfiltrate the stolen info to a server under their manage.
The progress will come as macOS is progressively becoming a feasible concentrate on of malware attacks, with a amount of macOS-precise data stealers appearing for sale in crimeware message boards in recent months to consider benefit of the large availability of Apple programs in corporations.
Upcoming WEBINARWay As well Vulnerable: Uncovering the Condition of the Identity Attack Surface area
Realized MFA? PAM? Assistance account protection? Find out how properly-equipped your group definitely is versus identity threats
Supercharge Your Abilities
“Whilst Mac malware genuinely does exist, it tends to be less detected than its Windows counterpart,” Segura stated. “The developer or seller for AMOS really designed it a selling point that their toolkit is capable of evading detection.”
Atomic Stealer is not the only malware propagated by way of malvertising and research motor optimization (Seo) poisoning campaigns, as proof has emerged of DarkGate (aka MehCrypter) latching on to the similar shipping and delivery system.
New versions of DarkGate have considering that been used in attacks mounted by menace actors using strategies comparable to that of Scattered Spider, Aon’s Stroz Friedberg Incident Response Products and services said past month.
Discovered this report intriguing? Follow us on Twitter and LinkedIn to read through more special material we publish.
Some elements of this short article are sourced from:
thehackernews.com

 The State of the Virtual CISO Report: MSP/MSSP Security Strategies for 2024
The State of the Virtual CISO Report: MSP/MSSP Security Strategies for 2024