Malaysian law enforcement authorities have announced the takedown of a phishing-as-a-assistance (PhaaS) operation termed BulletProofLink.
The Royal Malaysian Police stated the hard work, which was carried out with aid from the Australian Federal Police (AFP) and the U.S. Federal Bureau of Investigation (FBI) on November 6, 2023, was primarily based on information that the danger actors guiding the platform had been primarily based out of the region.
To that conclude, 8 folks aged involving 29 and 56, together with the syndicate’s mastermind, have been arrested throughout diverse places in Sabah, Selangor, Perak, and Kuala Lumpur, New Straits Moments claimed.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Together with the arrests, authorities confiscated servers, desktops, jewelry, cars, and cryptocurrency wallets containing somewhere around $213,000.

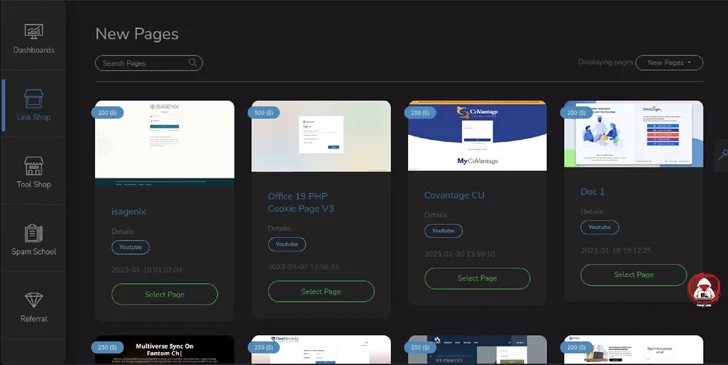
BulletProofLink, also referred to as BulletProftLink, is known for giving all set-to-use phishing templates on a subscription basis to other actors for conducting credential harvesting strategies. These templates mimic the login web pages of perfectly-recognized expert services like American Convey, Bank of The united states, DHL, Microsoft, and Naver.
In accordance to an investigation from Microsoft in September 2021, BulletProofLink actors also engaged in what is named double theft wherein the stolen qualifications are despatched to both their customers and the main developers, ensuing in extra monetization avenues.
“BulletProftLink is linked with the risk actor AnthraxBP who also went by the on the internet nicknames TheGreenMY and AnthraxLinkers,” cybersecurity agency Intel 471 explained very last 7 days.
“The actor maintained an lively web-site advertising and marketing phishing companies. The actor has an substantial underground footprint and operated on a variety of obvious web underground discussion boards and Telegram channels working with multiple handles.”
Considered to be lively due to the fact at the very least 2015, BulletProftLink’s on the web storefront is approximated to have no considerably less than 8,138 active consumers and 327 phishing web pages templates as of April 2023.
Another noteworthy function is its integration of the Evilginx2 to facilitate adversary-in-the-middle (AiTM) attacks that make it attainable for danger actors to steal session cookies and bypass multi-factor authentication protections.
“PhaaS schemes like BulletProftLink deliver the gas for more attacks,” Intel 471 reported. “Stolen login credentials are one particular of the key ways that malicious hackers achieve obtain to businesses.”

In a indication that danger actors are continually updating strategies in response to disruptions and getting a lot more innovative approaches, AiTM attacks have also been noticed using intermediary inbound links to files hosted on file-sharing options like DRACOON that include the URLs to adversary-managed infrastructure.
“This new strategy can bypass email security mitigations considering the fact that the first url appears to be from a legitimate supply and no data files are delivered to the victim’s endpoint as the hosted document made up of the link can be interacted with by using the file-sharing server inside the browser,” Craze Micro stated.
The progress will come as a 33-yr-old Serbian and Croatian nationwide, Milomir Desnica, pleaded responsible in the U.S. to working a drug trafficking system termed Monopoly Sector on the dark web and for conspiring to distribute in excess of 30 kilograms of methamphetamine to U.S. buyers.
The illicit market, which was set up by Desnica in 2019, was taken offline in December 2021 as part of a coordinated workout in partnership with Germany and Finland. Desnica was arrested in Austria in November 2022 and extradited to the U.S. to facial area drug trafficking prices in June 2023.
Identified this post exciting? Follow us on Twitter and LinkedIn to read through a lot more exclusive written content we put up.
Some components of this write-up are sourced from:
thehackernews.com


 New BiBi-Windows Wiper Targets Windows Systems in Pro-Hamas Attacks
New BiBi-Windows Wiper Targets Windows Systems in Pro-Hamas Attacks