An not known danger actor is leveraging malicious npm offers to goal builders with an purpose to steal supply code and configuration information from victim equipment, a signal of how threats lurk continuously in open up-resource repositories.
“The danger actor behind this campaign has been joined to destructive activity courting back to 2021,” software program source chain security agency Checkmarx stated in a report shared with The Hacker Information. “Because then, they have continually printed malicious packages.”
The most recent report is a continuation of the identical campaign that Phylum disclosed at the begin of the month in which a quantity of npm modules ended up engineered to exfiltrate beneficial facts to a remote server.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The deals, by layout, are configured to execute promptly publish-set up by signifies of a postinstall hook defined in the bundle.json file. It triggers the start of preinstall.js, which spawns index.js to seize the technique metadata as well as harvest source code and strategies from particular directories.
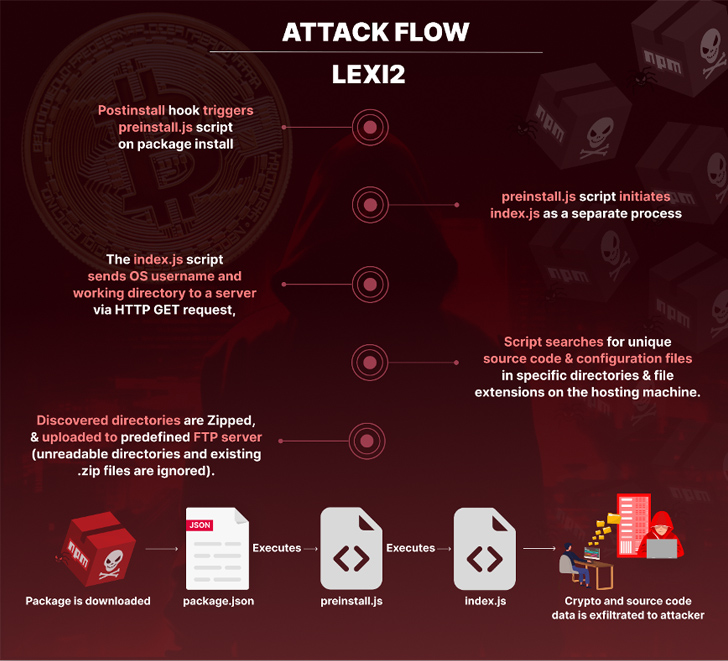
The attack culminates with the script developing a ZIP archive of the data and transmitting it to a predefined FTP server.
A typical trait that connects all the deals is the use of “lexi2” as the author in the deal.json file, enabling Checkmarx to trace the origins of the activity as far back as 2021.

Though the specific plans of the campaign are unclear, the use of deal names these as binarium-consumer, binarium-crm, and rocketrefer recommend that the concentrating on is geared to the cryptocurrency sector.
“The cryptocurrency sector continues to be a hot focus on, and it is really essential to understand that we’re not just grappling with malicious packages, but also persistent adversaries whose steady and meticulously planned attacks date again months or even yrs,” security researcher Yehuda Gelb claimed.
Observed this post fascinating? Abide by us on Twitter and LinkedIn to study additional exceptional material we article.
Some parts of this report are sourced from:
thehackernews.com


 Alert: Juniper Firewalls, Openfire, and Apache RocketMQ Under Attack from New Exploits
Alert: Juniper Firewalls, Openfire, and Apache RocketMQ Under Attack from New Exploits