A now-patched security flaw in the Microsoft Edge web browser could have been abused to set up arbitrary extensions on users’ devices and have out destructive steps.
“This flaw could have allowed an attacker to exploit a private API, originally intended for marketing and advertising reasons, to covertly set up extra browser extensions with wide permissions without the need of the user’s information,” Guardio Labs security researcher Oleg Zaytsev stated in a new report shared with The Hacker Information.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Tracked as CVE-2024-21388 (CVSS score: 6.5), it was addressed by Microsoft in Edge steady edition 121..2277.83 produced on January 25, 2024, next liable disclosure in November 2023. The Windows maker credited the two Zaytsev and Jun Kokatsu for reporting the issue.
“An attacker who productively exploited this vulnerability could get the privileges wanted to set up an extension,” Microsoft claimed in an advisory for the flaw, introducing it “could direct to a browser sandbox escape.”

Describing it as a privilege escalation flaw, the tech huge also emphasized that a thriving exploitation of the bug demands an attacker to “get added actions prior to exploitation to get ready the focus on atmosphere.”
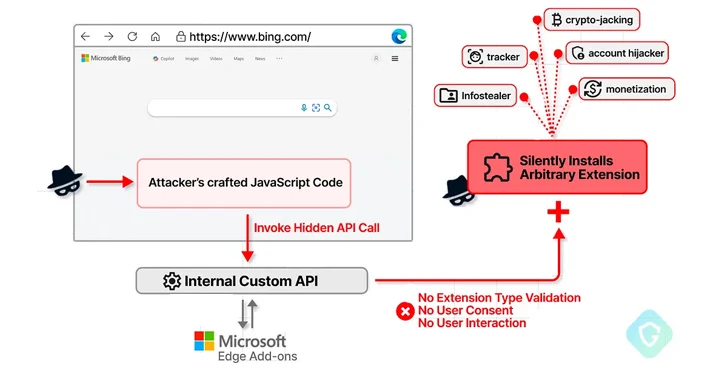
In accordance to Guardio’s conclusions, CVE-2024-21388 permits a negative actor with the potential to operate JavaScript on bing[.]com or microsoft[.]com web pages to put in any extensions from the Edge Include-ons retail outlet sans demanding user’s consent or conversation.
This is made doable by the simple fact that the browser will come with privileged obtain to certain personal APIs that make it doable to put in an add-on as long as it is really from the vendor’s possess extension marketplace.
1 this kind of API in the Chromium-dependent Edge browser is edgeMarketingPagePrivate, which is available from a established of allowlisted internet websites that belong to Microsoft, including bing[.]com, microsoft[.]com, microsoftedgewelcome.microsoft[.]com, and microsoftedgetips.microsoft[.]com, between other individuals.
The API also packs in a strategy referred to as installTheme() that, as the identify indicates, is developed to put in a topic from the Edge Include-ons store by passing a exceptional concept identifier (“themeId”) and its manifest file as enter.


The bug determined by Guardio is effectively a circumstance of inadequate validation, thus enabling an attacker to present any extension identifier from the storefront (as opposed to the themeId) and get it stealthily set up.
“As an additional bonus, as this extension installation is not completed rather in the manner it was initially developed for, there will be no have to have for any interaction or consent from the user,” Zaytsev described.

In a hypothetical attack scenario leveraging CVE-2024-21388, a risk actor could publish a seemingly harmless extension to the increase-ons shop and use it to inject a piece of destructive JavaScript code into bing[.]com – or any of the web pages that are permitted to entry the API – and install an arbitrary extension of their choice by invoking the API utilizing the extension identifier.
Set in different ways, executing the specifically crafted extension on the Edge browser and heading to bing[.]com will quickly put in the focused extension without the need of the victim’s authorization.
Guardio instructed The Hacker Information that though there is no evidence of this bug becoming exploited in the wild, it highlights the want for balancing person ease and security, and how browser customizations can inadvertently defeat security mechanisms and introduce numerous new attack vectors.
“It is really fairly quick for attackers to trick customers into putting in an extension that appears harmless, not acknowledging it serves as the original phase in a far more complex attack,” Zaytsev claimed. “This vulnerability could be exploited to aid the installation of supplemental extensions, likely for financial get.”
Found this report exciting? Observe us on Twitter and LinkedIn to read through extra distinctive content we article.
Some elements of this write-up are sourced from:
thehackernews.com

 SASE Solutions Fall Short Without Enterprise Browser Extensions, New Report Reveals
SASE Solutions Fall Short Without Enterprise Browser Extensions, New Report Reveals