Microsoft on Monday posted steerage for a recently discovered zero-day security flaw in its Office productivity suite that could be exploited to reach code execution on influenced devices.
The weakness, now assigned the identifier CVE-2022-30190, is rated 7.8 out of 10 for severity on the CVSS vulnerability scoring procedure. Microsoft Business versions Business office 2013, Place of work 2016, Place of work 2019, and Business office 2021, as very well as Experienced As well as editions, are impacted.
“To assist protect consumers, we have printed CVE-2022-30190 and more guidance right here,” a Microsoft spokesperson instructed The Hacker News in an emailed assertion.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The Follina vulnerability, which arrived to light-weight late final week, associated a actual-environment exploit that leveraged the shortcoming in a weaponized Word document to execute arbitrary PowerShell code by producing use of the “ms-msdt:” URI scheme. The sample was uploaded to VirusTotal from Belarus.
But 1st symptoms of exploitation of the flaw date again to April 12, 2022, when a second sample was uploaded to the malware databases. This artifact is thought to have targeted a person in Russia with a malicious Term doc (“приглашение на интервью.doc”) that masqueraded as an job interview invitation with Sputnik Radio.
“A distant code execution vulnerability exists when MSDT is known as making use of the URL protocol from a calling software this kind of as Word,” Microsoft said in an advisory for CVE-2022-30190.
“An attacker who successfully exploits this vulnerability can run arbitrary code with the privileges of the contacting application. The attacker can then install courses, look at, adjust, or delete facts, or make new accounts in the context allowed by the user’s rights.”
The tech giant credited crazyman, a member of the Shadow Chaser Group, for reporting the flaw on April 12, coinciding with the discovery of the in-the-wild exploit concentrating on Russian customers, indicating the corporation experienced been previously conscious of the vulnerability.
In fact, according to screenshots shared by the researcher on Twitter, Microsoft closed the report on April 21, 2022 stating “the issue has been mounted,” whilst also dismissing the flaw as “not a security issue” given that it demands a passkey presented by a assistance technician when setting up the diagnostic device.

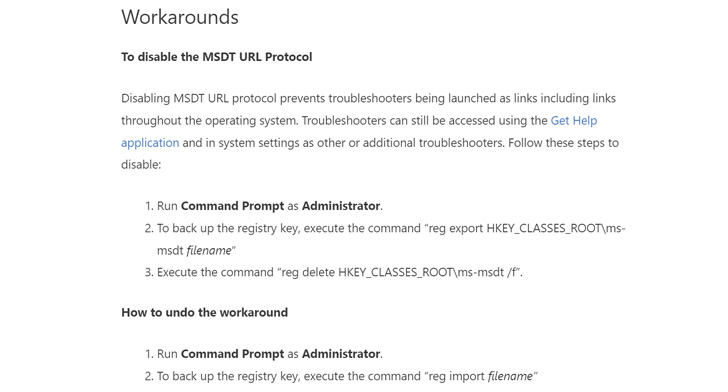
Moreover releasing detection guidelines for Microsoft Defender for Endpoint, the Redmond-primarily based firm has provided workarounds in its assistance to disable the MSDT URL protocol by way of a Windows Registry modification.
“If the calling application is a Microsoft Office environment software, by default, Microsoft Business opens paperwork from the internet in Guarded See or Software Guard for Office environment, the two of which protect against the latest attack,” Microsoft explained.
This is not the initially time Microsoft Office environment protocol strategies like “ms-msdt:” have arrive less than the scanner for their potential misuse. Earlier this January, Germany security organization SySS disclosed how it can be probable to open files straight by using specially crafted URLs these kinds of as “ms-excel:ofv|u|https://192.168.1.10/poc[.]xls.”
Uncovered this posting fascinating? Abide by THN on Fb, Twitter and LinkedIn to read a lot more distinctive information we article.
Some pieces of this report are sourced from:
thehackernews.com

 Anonymous Claims Attacks Against Belarus for Involvement in Russian Invasion of Ukraine
Anonymous Claims Attacks Against Belarus for Involvement in Russian Invasion of Ukraine