The threat actor recognized as COLDRIVER has continued to engage in credential theft activities towards entities that are of strategic pursuits to Russia while simultaneously increasing its detection evasion capabilities.
The Microsoft Threat Intelligence staff is monitoring less than the cluster as Star Blizzard (previously SEABORGIUM). It is really also referred to as Blue Callisto, BlueCharlie (or TAG-53), Calisto (alternately spelled Callisto), and TA446.
The adversary “proceeds to prolifically focus on people and organizations concerned in international affairs, protection, and logistics help to Ukraine, as effectively as academia, information security organizations, and other entities aligning with Russian point out interests,” Redmond mentioned.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Star Blizzard, linked to Russia’s Federal Security Company (FSB), has a keep track of history of location up lookalike domains that impersonate the login pages of specific organizations. It’s acknowledged to be active considering the fact that at minimum 2017.
Impending WEBINAR Cracking the Code: Find out How Cyber Attackers Exploit Human Psychology
At any time puzzled why social engineering is so efficient? Dive deep into the psychology of cyber attackers in our impending webinar.
Be part of Now
In August 2023, Recorded Foreseeable future uncovered 94 new domains that are element of the danger actor’s attack infrastructure, most of which characteristic key phrases similar to data technology and cryptocurrency.
Microsoft stated it observed the adversary leveraging server-aspect scripts to protect against automatic scanning of the actor-managed infrastructure beginning April 2023, relocating away from hCaptcha to figure out targets of curiosity and redirecting the browsing session to the Evilginx server.
The server-facet JavaScript code is built to check if the browser has any plugins put in, if the website page is becoming accessed by an automation device like Selenium or PhantomJS, and transmit the effects to the server in the type of a HTTP Article request.
“Next the Submit ask for, the redirector server assesses the info collected from the browser and decides whether or not to let ongoing browser redirection,” Microsoft explained.
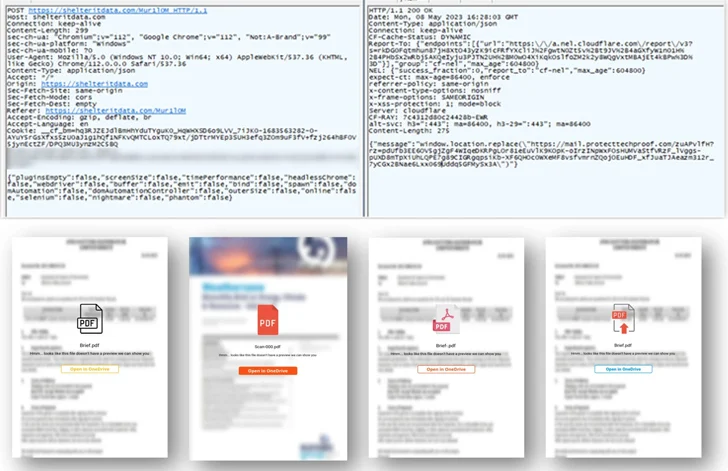
“When a excellent verdict is achieved, the browser gets a response from the redirection server, redirecting to the upcoming phase of the chain, which is both an hCaptcha for the consumer to resolve, or direct to the Evilginx server.”
Also newly made use of by Star Blizzard are email marketing companies like HubSpot and MailerLite to craft campaigns that serve as the commencing place of the redirection chain that culminates at the Evilginx server hosting the credential harvesting page.
In addition, the risk actor has been observed making use of a area title company (DNS) service provider to solve actor-registered domain infrastructure, sending password-secured PDF lures embedding the one-way links to evade email security procedures as properly as host the documents on Proton Drive.
Which is not all. In a signal that the threat actor is actively holding tabs on general public reporting into its techniques and strategies, it has now upgraded its domain era algorithm (DGA) to consist of a far more randomized checklist of text when naming them.

Inspite of these variations, “Star Blizzard routines keep on being targeted on email credential theft, predominantly concentrating on cloud-centered email providers that host organizational and/or personal email accounts,” Microsoft reported.
“Star Blizzard remains regular in their use of pairs of devoted VPSs to host actor-managed infrastructure (redirector + Evilginx servers) employed for spear-phishing functions, wherever each and every server generally hosts a individual actor registered domain.”
U.K. Sanctions Two Users of Star Blizzard
The improvement comes as the U.K. identified as out Star Blizzard for “sustained unsuccessful makes an attempt to interfere in U.K. political processes” by concentrating on higher-profile folks and entities by cyber functions.
In addition to linking Star Blizzard to Centre 18, a subordinate aspect within FSB, the U.K. government sanctioned two associates of the hacking crew – Ruslan Aleksandrovich Peretyatko and Andrey Stanislavovich Korinets (aka Alexey Doguzhiev) – for their involvement in the spear-phishing campaigns.
The activity “resulted in unauthorized entry and exfiltration of sensitive info, which was supposed to undermine UK corporations and much more broadly, the UK governing administration,” it claimed.
Observed this posting intriguing? Comply with us on Twitter and LinkedIn to study far more exceptional content we publish.
Some sections of this short article are sourced from:
thehackernews.com


 New Bluetooth Flaw Let Hackers Take Over Android, Linux, macOS, and iOS Devices
New Bluetooth Flaw Let Hackers Take Over Android, Linux, macOS, and iOS Devices