Microsoft is warning of continuing attempts by nation-point out adversaries and commodity attackers to acquire edge of security vulnerabilities uncovered in the Log4j open-resource logging framework to deploy malware on susceptible units.
“Exploitation tries and tests have remained significant all through the very last weeks of December,” Microsoft Menace Intelligence Middle (MSTIC) reported in revised advice revealed previously this week. “We have noticed quite a few present attackers introducing exploits of these vulnerabilities in their existing malware kits and practices, from coin miners to palms-on-keyboard attacks.”
Publicly disclosed by the Apache Application Basis on December 10, 2021, the remote code execution (RCE) vulnerability in Apache Log4j 2, aka Log4Shell, has emerged as a new attack vector for popular exploitation by a selection of threat actors.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

In the subsequent months, 4 a lot more weaknesses in the utility have arrive to light — CVE-2021-45046, CVE-2021-45105, CVE-2021-4104, and CVE-2021-44832 — offering opportunistic lousy actors with persistent handle more than the compromised equipment and mount an evolving array of attacks ranging from cryptocurrency miners to ransomware.
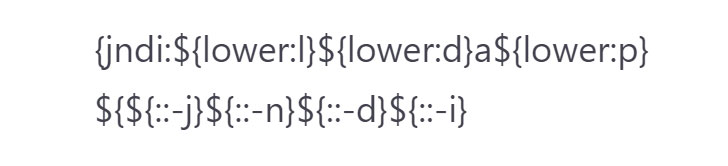
Even as the mass scanning tries are demonstrating no signals of letting up, efforts are underway to evade string-matching detections by obfuscating the malicious HTTP requests orchestrated to crank out a web request log applying Log4j that leverages JNDI to execute a request to the attacker-controlled web page.
In addition, Microsoft stated it noticed “quick uptake of the vulnerability into existing botnets like Mirai, existing campaigns previously concentrating on vulnerable Elasticsearch techniques to deploy cryptocurrency miners, and exercise deploying the Tsunami backdoor to Linux techniques.”
On best of that, the Log4Shell vulnerability has also been place to use to drop added distant entry toolkits and reverse shells these as Meterpreter, Bladabindi (aka NjRAT), and HabitsRAT.
“At this juncture, consumers ought to suppose broad availability of exploit code and scanning capabilities to be a genuine and current threat to their environments,” MSTIC noted. “Due to the lots of software package and expert services that are impacted and specified the pace of updates, this is envisioned to have a long tail for remediation, demanding ongoing, sustainable vigilance.”
The improvement also comes as the U.S. Federal Trade Commission (FTC) issued a warning that it “intends to use its total lawful authority to go after providers that fail to choose affordable actions to shield customer information from publicity as a consequence of Log4j, or comparable known vulnerabilities in the long term.”
Uncovered this report exciting? Abide by THN on Fb, Twitter and LinkedIn to study a lot more special content material we write-up.
Some areas of this report are sourced from:
thehackernews.com



 Microsoft Sees Rampant Log4j Exploit Attempts, Testing
Microsoft Sees Rampant Log4j Exploit Attempts, Testing