Microsoft is warning of a new phishing marketing campaign undertaken by an preliminary entry broker that requires utilizing Groups messages as lures to infiltrate corporate networks.
The tech giant’s Threat Intelligence team is monitoring the cluster beneath the title Storm-0324, which is also acknowledged by the monikers TA543 and Sagrid.
“Beginning in July 2023, Storm-0324 was observed distributing payloads applying an open-source resource to mail phishing lures by way of Microsoft Teams chats,” the firm reported, adding the growth marks a shift from using email-based mostly original infection vectors for original accessibility.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Storm-0324 operates in the cybercriminal economy as a payload distributor, offering a company that lets for the propagation of numerous payloads using evasive infection chains. This incorporates a mix of downloaders, banking trojans, ransomware, and modular toolkits this sort of as Nymaim, Gozi, TrickBot, IcedID, Gootkit, Dridex, Sage, GandCrab, and JSSLoader.
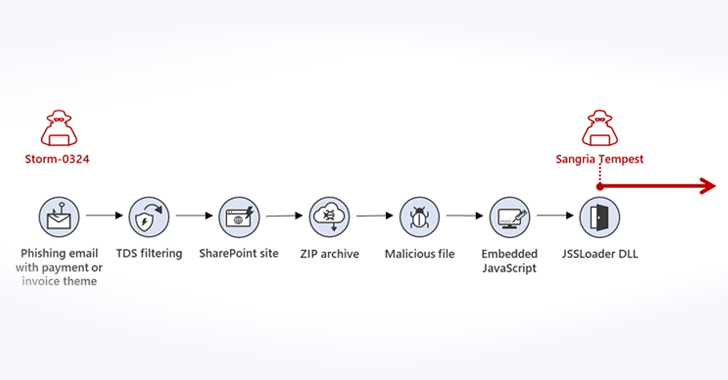
Attack sequences mounted by the actor in the earlier have used bill- and payment-themed decoy email messages to trick buyers into downloading SharePoint-hosted ZIP archive data files distributing JSSLoader, a malware loader capable of profiling infected devices and loading further payloads.

“The actor’s email chains are hugely evasive, making use of traffic distribution units (TDS) like BlackTDS and Keitaro, which provide identification and filtering abilities to tailor user visitors,” Microsoft said.
“This filtering ability allows attackers to evade detection by specific IP ranges that could be security options, like malware sandboxes, while also productively redirecting victims to their malicious down load site.”
The entry afforded by the malware paves the way for the ransomware-as-a-services (RaaS) actor Sangria Tempest (aka Carbon Spider, ELBRUS, and FIN7) to carry out write-up-exploitation steps and deploy file-encrypting malware.
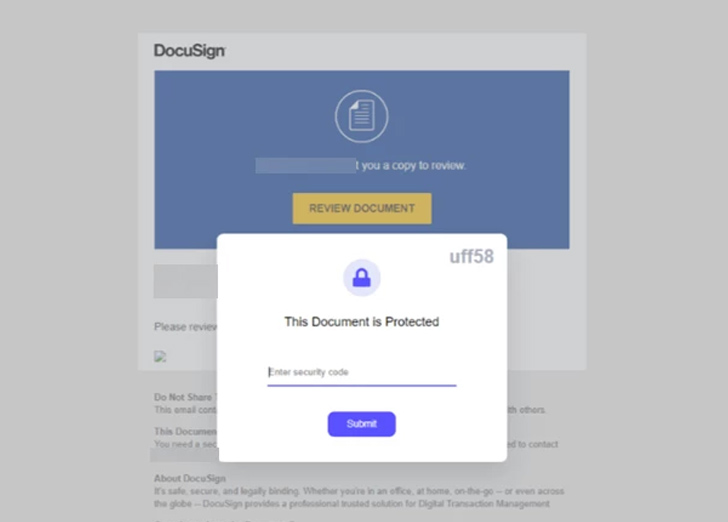
The modus operandi has since obtained a facelift as of July 2023 wherein the phishing lures are sent in excess of Groups with destructive hyperlinks main to a malicious ZIP file hosted on SharePoint.
This is completed by leveraging an open-source software known as TeamsPhisher, which allows Teams tenant end users to connect information to messages sent to exterior tenants by exploiting an issue that was first highlighted by JUMPSEC in June 2023.
It is really value noting that a identical method was adopted by the Russian nation-state actor APT29 (aka Midnight Blizzard) in attacks targeting about 40 corporations globally in May perhaps 2023.
The firm reported it has produced many security enhancements to block the menace and that it “suspended discovered accounts and tenants connected with inauthentic or fraudulent habits.”
“For the reason that Storm-0324 fingers off obtain to other menace actors, pinpointing and remediating Storm-0324 action can avoid more harmful abide by-on attacks like ransomware,” Microsoft even further pointed out.
The disclosure arrives as Kaspersky detailed the tactics, procedures and methods of the infamous ransomware group regarded as Cuba (aka COLDDRAW and Tropical Scorpius), along with figuring out a new moniker named V Is Vendetta that is suspected to have been employed by a sub-group or affiliate.
The team, like RaaS strategies, employs the double extortion small business product to attack many organizations all-around the earth and make illicit revenue.
Upcoming WEBINARWay Much too Vulnerable: Uncovering the Condition of the Id Attack Area
Reached MFA? PAM? Service account protection? Come across out how properly-geared up your business truly is versus identity threats
Supercharge Your Competencies
Ingress routes entail the exploitation of ProxyLogon, ProxyShell, ZeroLogon, and security flaws in Veeam Backup & Replication computer software to deploy a tailor made backdoor dubbed BUGHATCH, which is then utilised to provide Cobalt Strike and up-to-date variations of BURNTCIGAR in get to terminate security program working on the host.
“The Cuba cybercrime gang employs an comprehensive arsenal of the two publicly readily available and customized-built resources, which it keeps up to date, and many methods and approaches together with rather unsafe ones, this sort of as BYOVD,” Kaspersky said.
Ransomware attacks have witnessed a main spike in 2023, with the U.K. National Cyber Security Centre (NCSC) and Countrywide Criminal offense Company (NCA) noting that they are “reliant on a sophisticated provide chain.”
“Focussing on particular ransomware strains can be confusing at best, and unhelpful at worst,” the businesses claimed in a report posted before this 7 days. “Most ransomware incidents are not due to sophisticated attack tactics the preliminary accesses to victims are received opportunistically, with achievements generally the consequence of inadequate cyber hygiene.”
Located this report exciting? Observe us on Twitter and LinkedIn to examine additional special material we write-up.
Some elements of this short article are sourced from:
thehackernews.com

 Microsoft Releases Patch for Two New Actively Exploited Zero-Days Flaws
Microsoft Releases Patch for Two New Actively Exploited Zero-Days Flaws