Microsoft on Wednesday took the lid off a “novel and distinctive Russian menace actor,” which it mentioned is linked to the Common Employees Primary Intelligence Directorate (GRU) and has a “comparatively lower achievements fee.”
The tech giant’s Threat Intelligence staff, which was beforehand tracking the group under its emerging moniker DEV-0586, has graduated it to a named actor dubbed Cadet Blizzard.
“Cadet Blizzard seeks to carry out disruption, destruction, and information and facts assortment, working with regardless of what indicates are obtainable and at times acting in a haphazard vogue,” the enterprise said.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“When the group carries higher risk thanks to their destructive action, they look to function with a reduced diploma of operational security than that of longstanding and superior Russian groups these kinds of as Seashell Blizzard and Forest Blizzard.”

Cadet Blizzard 1st arrived to light-weight in January 2022 in relationship with destructive cyber exercise targeting Ukraine employing a novel wiper malware known as WhisperGate (aka PAYWIPE) in the weeks major to Russia’s armed forces invasion of the region.
The point out-sponsored actor, for every Microsoft, has a track file of orchestrating damaging attacks, espionage, and info operations aimed at entities situated in Ukraine, Europe, Central Asia, and, periodically, Latin The united states.
Suspected to have been operational in some capacity because at the very least 2020, intrusions mounted by Cadet Blizzard have predominantly concentrated on governing administration companies, legislation enforcement, non-earnings and non-governmental corporations, IT provider suppliers, and emergency services.
“Cadet Blizzard is energetic 7 times a 7 days and has conducted its operations through its primary targets’ off-business hours when its action is significantly less probable to be detected,” Microsoft’s Tom Burt mentioned. “In addition to Ukraine, it also focuses on NATO member states concerned in delivering armed service help to Ukraine.”
It can be really worth noting that Cadet Blizzard also overlaps with teams monitored by the broader cybersecurity neighborhood beneath the names Ember Bear (CrowdStrike), FROZENVISTA (Google TAG), Nodaria (Symantec), TA471 (Proofpoint), UAC-0056 (CERT-UA), and UNC2589 (Google Mandiant).
Apart from WhisperGate, the hacking crew is identified to leverage a raft of weapons for its arsenal, including SaintBot, OutSteel, GraphSteel, GrimPlant, and a lot more not too long ago, Graphiron. Microsoft has attributed SaintBot and OutSteel to a connected activity cluster labeled Storm-0587.
Approaching WEBINAR🔐 Mastering API Security: Knowing Your Accurate Attack Area
Explore the untapped vulnerabilities in your API ecosystem and get proactive techniques toward ironclad security. Sign up for our insightful webinar!
Be a part of the Session.wn-button,.wn-label,.wn-label:immediately afterscreen:inline-block.verify_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px solid #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-best-still left-radius:25px-moz-border-radius-topleft:25px-webkit-border-base-proper-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-dimension:13pxmargin:20px 0font-body weight:600letter-spacing:.6pxcolor:#596cec.wn-label:right afterwidth:50pxheight:6pxcontent:”border-major:2px reliable #d9deffmargin: 8px.wn-titlefont-dimension:21pxpadding:10px 0font-pounds:900text-align:leftline-top:33px.wn-descriptiontext-align:leftfont-measurement:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-dimensions:15pxcolor:#fff!importantborder:0line-height:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-weight:500letter-spacing:.2px
“Cadet Blizzard is also connected to the defacements of numerous Ukrainian organization web sites, as effectively as many operations, which include the hack-and-leak discussion board regarded as ‘Free Civilian,'” Microsoft additional.
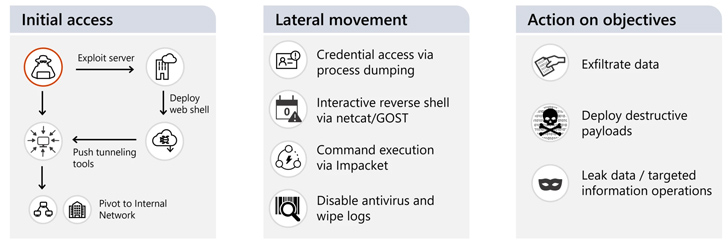
Other notable tradecraft involves the use of dwelling-off-the-land (LotL) strategies publish gaining first obtain to reach lateral movement, acquire qualifications and other info, and deploy tools to aid defense evasion and persistence.
The cyber assaults, for their element, are achieved by the exploitation of known flaws in uncovered web servers (e.g., Atlassian Confluence and Microsoft Trade Server) and information administration methods.
“As the war continues, Cadet Blizzard activity poses an rising risk to the broader European group, specially any successful attacks versus governments and IT assistance companies, which may well give the actor each tactical and strategic-degree perception into Western operations and plan encompassing the conflict,” Microsoft pointed out.
Discovered this write-up exciting? Observe us on Twitter and LinkedIn to examine a lot more unique written content we write-up.
Some sections of this post are sourced from:
thehackernews.com


 LockBit Makes $91m From US Victims in Two Years
LockBit Makes $91m From US Victims in Two Years