A Linux botnet malware known as XorDdos has witnessed a 254% surge in activity about the very last 6 months, in accordance to most recent study from Microsoft.
The trojan, so named for carrying out denial-of-company attacks on Linux devices and its use of XOR-dependent encryption for communications with its command-and-control (C2) server, is regarded to have been energetic considering the fact that at least 2014.
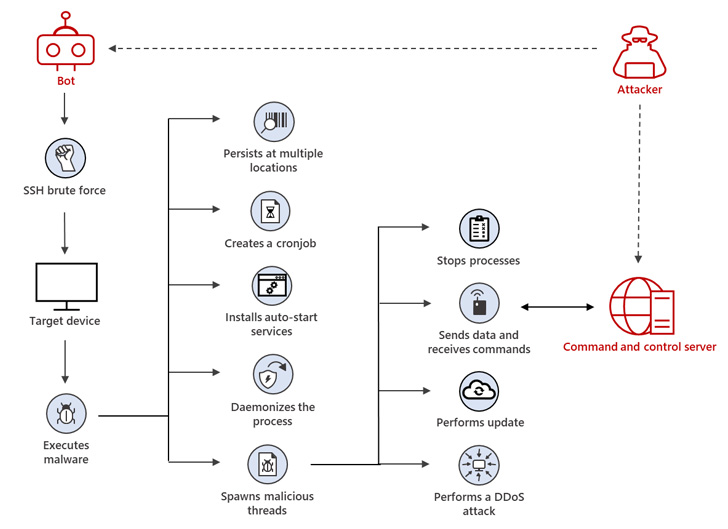
“XorDdos’ modular character offers attackers with a versatile trojan capable of infecting a wide range of Linux program architectures,” Ratnesh Pandey, Yevgeny Kulakov, and Jonathan Bar Or of the Microsoft 365 Defender Exploration Team said in an exhaustive deep-dive of the malware.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Its SSH brute power attacks are a comparatively uncomplicated nevertheless powerful system for gaining root entry above a quantity of potential targets.”
Distant command about susceptible IoT and other internet-connected equipment is received by implies of protected shell (SSH) brute-power attacks, enabling the malware to form a botnet able of carrying dispersed denial-of-support (DDoS) attacks.
Besides getting compiled for ARM, x86, and x64 architectures, the malware is built to assist various Linux distributions, not to mention arrive with features to siphon delicate information, install a rootkit, and act as a vector for follow-on routines.
In latest years, XorDdos has focused unprotected Docker servers with uncovered ports (2375), making use of victimized methods to overwhelm a focus on network or provider with faux visitors in order to render it inaccessible.

XorDdos has since emerged as the prime Linux-qualified threat in 2021, in accordance to a report from CrowdStrike printed previously this January.
“XorDdos employs evasion and persistence mechanisms that allow for its functions to keep on being robust and stealthy,” the researchers mentioned.
“Its evasion abilities include things like obfuscating the malware’s actions, evading rule-based detection mechanisms and hash-based mostly malicious file lookup, as well as utilizing anti-forensic techniques to crack method tree-primarily based evaluation.”
Discovered this posting attention-grabbing? Comply with THN on Facebook, Twitter and LinkedIn to read through additional exceptional content we submit.
Some components of this posting are sourced from:
thehackernews.com


 Modern “Smart” Farm Machinery Vulnerable to Cyber-Attackers
Modern “Smart” Farm Machinery Vulnerable to Cyber-Attackers