Cybersecurity scientists have learned multiple strategies focusing on Docker Hub by planting hundreds of thousands of destructive “imageless” containers in excess of the earlier 5 years, after once again underscoring how open up-source registries could pave the way for supply chain attacks.
“Over four million of the repositories in Docker Hub are imageless and have no content except for the repository documentation,” JFrog security researcher Andrey Polkovnichenko reported in a report shared with The Hacker News.
What’s more, the documentation has no link in any respect to the container. As an alternative, it really is a web web page that’s designed to entice end users into checking out phishing or malware-hosting web sites.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

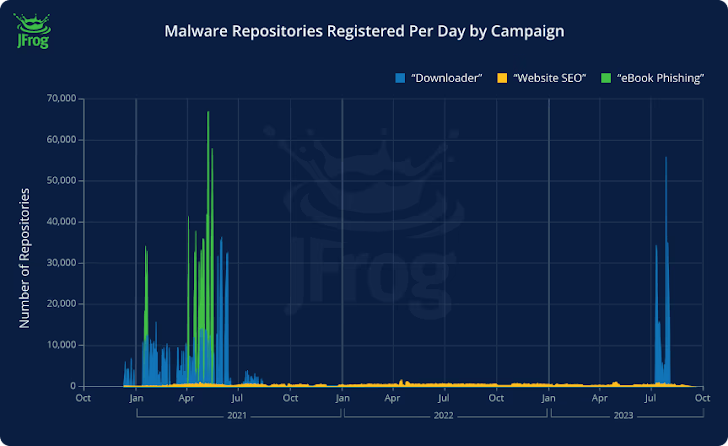
Of the 4.79 million imageless Docker Hub repositories uncovered, 3.2 million of them are reported to have been used as landing internet pages to redirect unsuspecting consumers to fraudulent web sites as portion of three broad strategies –
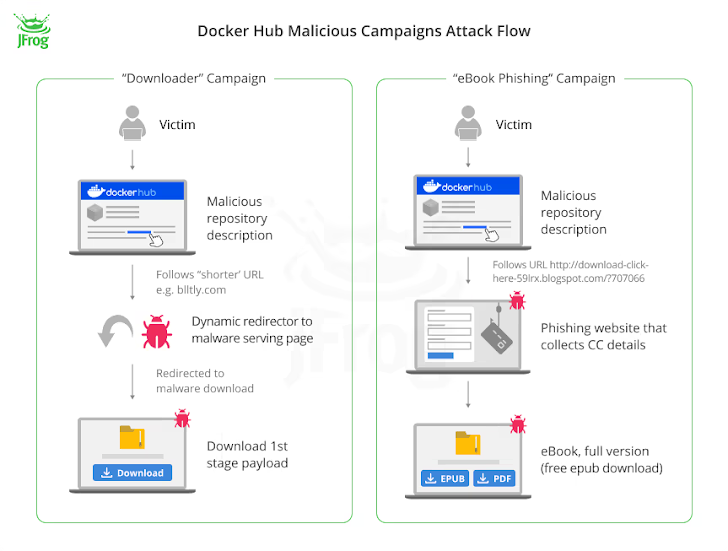
- Downloader (repositories designed in the initial 50 percent of 2021 and September 2023), which advertises back links to purported pirated information or cheats for video games but possibly specifically hyperlinks to destructive resources or a reputable just one that, in flip, consists of JavaScript code that redirects to the destructive payload just after 500 milliseconds.
- E-e-book phishing (repositories made in mid-2021), which redirects end users hunting for e-publications to a website (“rd.lesac.ru”) that, in transform, urges them to enter their economical information to down load the e-guide.
- Web site (countless numbers of repositories produced each day from April 2021 to Oct 2023), which has a link to an on the web diary-hosting service termed Penzu in some circumstances.
The payload sent as portion of the downloader marketing campaign is made to get in touch with a command-and-regulate (C2) server and transmit procedure metadata, adhering to which the server responds with a backlink to cracked software program.
On the other hand, the exact intention of the web-site cluster is currently unclear, with the marketing campaign also propagated on websites that have a lax material moderation policy.

“The most relating to facet of these 3 strategies is that there is not a whole lot that consumers can do to secure on their own at the outset, other than exercising warning,” Shachar Menashe, senior director of security study at JFrog, reported in a statement shared with The Hacker Information.
“We’re essentially hunting at a malware playground that in some scenarios has been a few a long time in the generating. These danger actors are remarkably motivated and are hiding guiding the trustworthiness of the Docker Hub title to entice victims.”
With menace actors getting painstaking efforts to poison well regarded utilities, as evidenced in the circumstance of the XZ Utils compromise, it’s very important that builders exercising caution when it will come to downloading deals from open up-source ecosystems/
“As Murphy’s Legislation suggests, if a thing can be exploited by malware developers, it inevitably will be, so we count on that these campaigns can be identified in more repositories than just Docker Hub,” Menashe stated.
Found this article fascinating? Stick to us on Twitter and LinkedIn to go through much more exclusive articles we write-up.
Some components of this short article are sourced from:
thehackernews.com


 U.S. Government Releases New AI Security Guidelines for Critical Infrastructure
U.S. Government Releases New AI Security Guidelines for Critical Infrastructure