Many bugs impacting thousands and thousands of motor vehicles from 16 various manufacturers could be abused to unlock, commence, and observe vehicles, additionally affect the privacy of motor vehicle homeowners.
The security vulnerabilities were being located in the automotive APIs powering Acura, BMW, Ferrari, Ford, Genesis, Honda, Hyundai, Infiniti, Jaguar, Kia, Land Rover, Mercedes-Benz, Nissan, Porsche, Rolls Royce, Toyota as properly as in software program from Reviver, SiriusXM, and Spireon.
The flaws operate a huge gamut, ranging from those people that give entry to inside firm techniques and consumer information to weaknesses that would allow an attacker to remotely mail commands to accomplish code execution.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The research builds on before findings from late final yr, when Yuga Labs researcher Sam Curry et al specific security flaws in a connected vehicle assistance provided by SiriusXM that could possibly put autos at risk of remote attacks.
The most severe of the issues, which issue Spireon’s telematics resolution, could have been exploited to achieve comprehensive administrative access, enabling an adversary to issue arbitrary commands to about 15.5 million autos as nicely as update gadget firmware.
“This would’ve authorized us to track and shut off starters for police, ambulances, and law enforcement autos for a amount of diverse large towns and dispatch instructions to people vehicles,” the researchers reported.
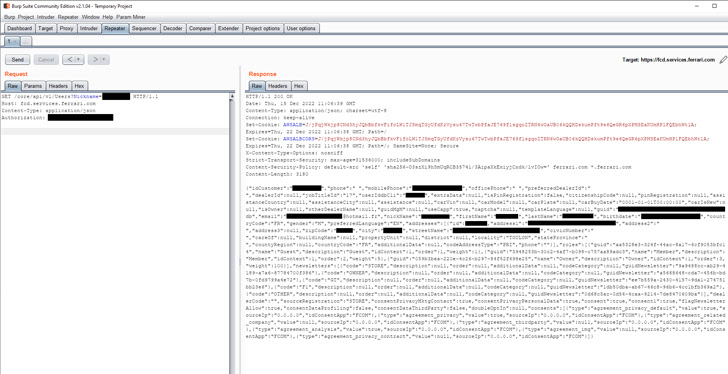
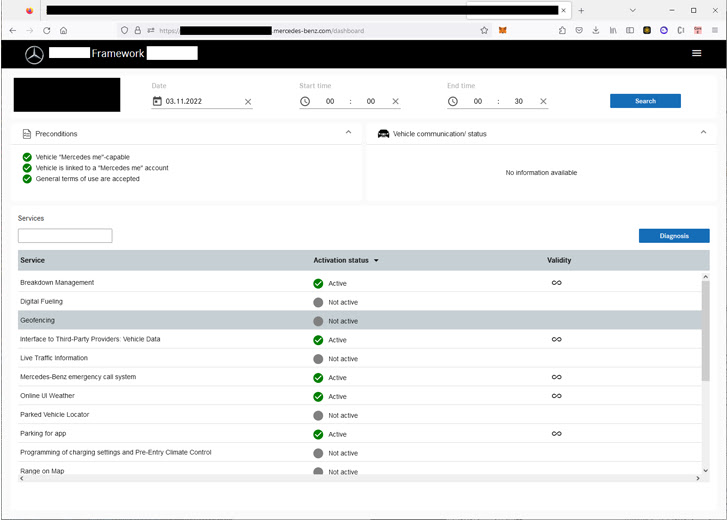
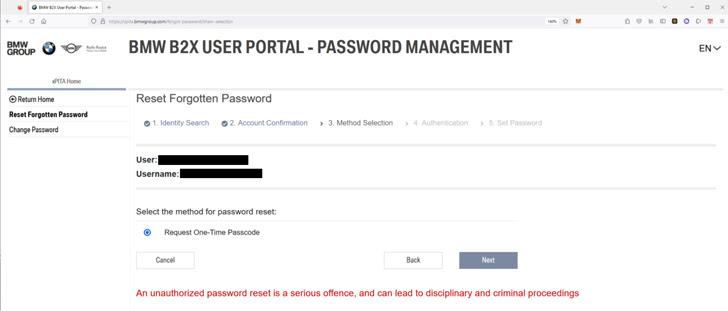
Vulnerabilities discovered in Mercedes-Benz could grant obtain to inner programs by way of an improperly configured solitary signal-on (SSO) authentication plan, when other individuals could permit person account takeover and disclosure of delicate information.
Other flaws make it achievable to access or modify purchaser records, interior supplier portals, track motor vehicle GPS locations in serious time, deal with the license plate facts for all Reviver consumers, and even update car status as “stolen.”
While all the security vulnerabilities have because been set by the respective suppliers subsequent responsible disclosure, the results spotlight the have to have for defense-in-depth system to consist of threats and mitigate risk.
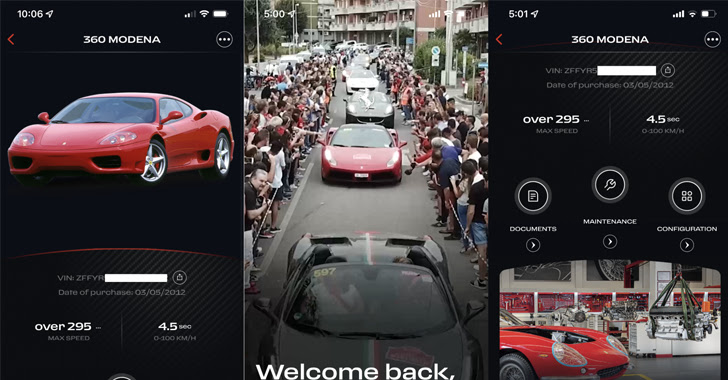
“If an attacker have been equipped to locate vulnerabilities in the API endpoints that car telematics units applied, they could honk the horn, flash the lights, remotely observe, lock/unlock, and start out/quit autos, completely remotely,” the scientists mentioned.
Found this post fascinating? Adhere to us on Twitter and LinkedIn to examine extra distinctive material we submit.
Some elements of this report are sourced from:
thehackernews.com

 Threat Actors Spread RAT Via Pokemon NFT Card Site
Threat Actors Spread RAT Via Pokemon NFT Card Site