The Iran-connected MuddyWater danger actor has been observed focusing on numerous nations around the world in the Center East as well as Central and West Asia as component of a new spear-phishing exercise.
“The campaign has been observed targeting Armenia, Azerbaijan, Egypt, Iraq, Israel, Jordan, Oman, Qatar, Tajikistan, and the United Arab Emirates,” Deep Intuition researcher Simon Kenin mentioned in a complex write-up.
MuddyWater, also called Boggy Serpens, Cobalt Ulster, Earth Vetala, Mercury, Seedworm, Static Kitten, and TEMP.Zagros, is stated to be a subordinate component inside Iran’s Ministry of Intelligence and Security (MOIS).

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Active due to the fact at least 2017, attacks mounted by the espionage group have commonly specific telecommunications, authorities, defense, and oil sectors.

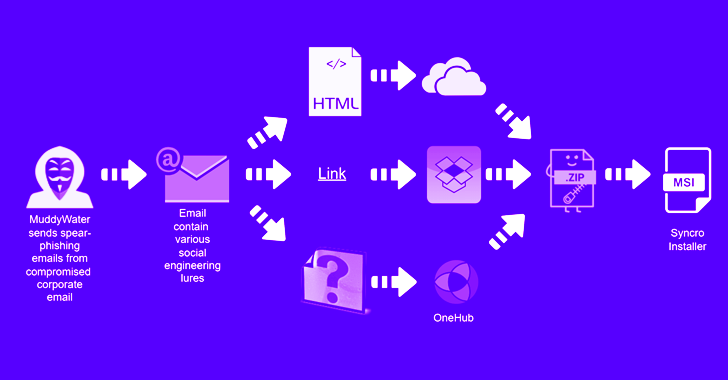
The recent intrusion established follows MuddyWater’s lengthy-operating modus operandi of applying phishing lures that have direct Dropbox backlinks or doc attachments with an embedded URL pointing to a ZIP archive file.
It truly is really worth mentioning in this article that the messages are sent from presently compromised corporate email accounts, which are getting made available for sale on the darknet by webmail outlets like Xleet, Odin, Xmina, and Lufix everywhere amongst $8 to $25 per account.
When the archive files have formerly harbored installers for genuine instruments like ScreenConnect and RemoteUtilities, the actor was noticed switching to Atera Agent in July 2022 in a bid to fly under the radar.
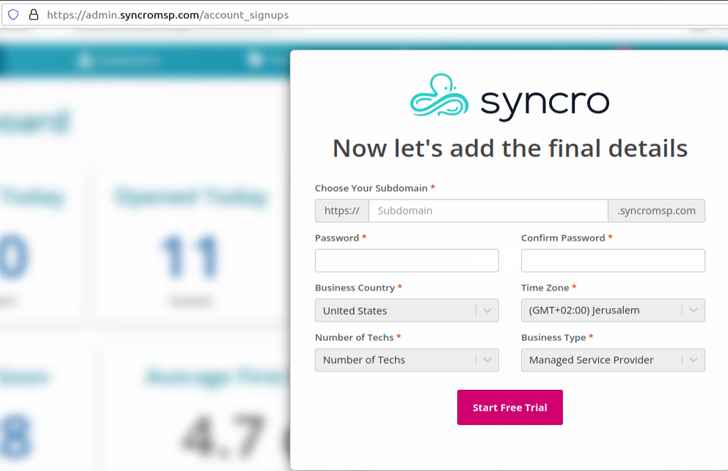
But in a additional signal that the marketing campaign is staying actively managed and updated, the attack methods have been tweaked still again to supply a distinctive remote administration instrument named Syncro.
The integrated MSP program gives a way to absolutely handle a device, allowing the adversary to conduct reconnaissance, deploy added backdoors, and even promote obtain to other actors.
“A danger actor that has entry to a corporate equipment by means of this kind of abilities has approximately limitless selections,” Kenin pointed out.
The findings appear as Deep Intuition also uncovered new malware components used by a Lebanon-centered team tracked as Polonium in its attacks aimed completely at Israeli entities.
“Polonium is coordinating its operations with many tracked actor groups affiliated with Iran’s Ministry of Intelligence and Security (MOIS), centered on victim overlap and the subsequent prevalent techniques and tooling,” Microsoft pointed out in June 2022.
Located this article intriguing? Stick to us on Twitter and LinkedIn to read much more distinctive information we post.
Some pieces of this post are sourced from:
thehackernews.com

 US Sues TikTok Over Child Safety and Data Security Claims
US Sues TikTok Over Child Safety and Data Security Claims