The China-joined menace actor identified as Mustang Panda has specific different Asian countries working with a variant of the PlugX (aka Korplug) backdoor dubbed DOPLUGS.
“The piece of custom-made PlugX malware is dissimilar to the normal kind of the PlugX malware that consists of a concluded backdoor command module, and that the former is only employed for downloading the latter,” Pattern Micro scientists Sunny Lu and Pierre Lee claimed in a new technical compose-up.
Targets of DOPLUGS have been principally found in Taiwan, and Vietnam, and to a lesser extent in Hong Kong, India, Japan, Malaysia, Mongolia, and even China.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
PlugX is a staple tool of Mustang Panda, which is also tracked as BASIN, Bronze President, Camaro Dragon, Earth Preta, HoneyMyte, RedDelta, Red Lich, Stately Taurus, TA416, and TEMP.Hex. It is really identified to be lively considering the fact that at least 2012, despite the fact that it 1st arrived to light in 2017.

The risk actor’s tradecraft involves carrying out very well-solid spear-phishing strategies that are built to deploy custom made malware. It also has a keep track of report of deploying its personal custom made PlugX variants such as RedDelta, Thor, Hodur, and DOPLUGS (dispersed by way of a marketing campaign named SmugX) considering that 2018.
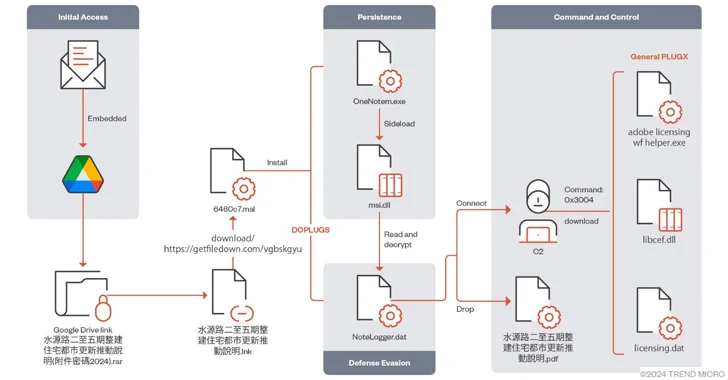
Compromise chains leverage a established of distinct practices, using phishing messages as a conduit to deliver a 1st-stage payload that, though displaying a decoy doc to the receiver, covertly unpacks a reputable, signed executable that is susceptible to DLL side-loading in get to facet-load a dynamic-url library (DLL), which, in turn, decrypts and executes PlugX.
The PlugX malware subsequently retrieves Poison Ivy distant obtain trojan (RAT) or Cobalt Strike Beacon to build a connection with a Mustang Panda-controlled server.
In December 2023, Lab52 uncovered a Mustang Panda campaign focusing on Taiwanese political, diplomatic, and governmental entities with DOPLUGS, but with a noteworthy change.
“The destructive DLL is published in the Nim programming language,” Lab52 mentioned. “This new variant utilizes its individual implementation of the RC4 algorithm to decrypt PlugX, as opposed to prior variations that use the Windows Cryptsp.dll library.”
DOPLUGS, initially documented by Secureworks in September 2022, is a downloader with 4 backdoor commands, 1 of which is orchestrated to obtain the standard form of the PlugX malware.

Craze Micro claimed it also discovered DOPLUGS samples built-in with a module identified as KillSomeOne, a plugin that’s responsible for malware distribution, information and facts collection, and document theft through USB drives.
This variant will come equipped with an further launcher ingredient that executes the genuine executable to conduct DLL-sideloading, in addition to supporting performance to run instructions and download the next-phase malware from an actor-controlled server.
It’s worth noting that a custom-made PlugX variant, such as the KillSomeOne module built for spreading via USB, was uncovered as early as January 2020 by Avira as section of attacks directed against Hong Kong and Vietnam.
“This shows that Earth Preta has been refining its applications for some time now, frequently introducing new functionalities and characteristics,” the scientists said. “The group stays very lively, especially in Europe and Asia.”
Found this article exciting? Observe us on Twitter and LinkedIn to browse a lot more exceptional written content we article.
Some elements of this posting are sourced from:
thehackernews.com

 6 Ways to Simplify SaaS Identity Governance
6 Ways to Simplify SaaS Identity Governance