A Rust variant of a ransomware pressure regarded as Agenda has been observed in the wild, building it the hottest malware to adopt the cross-system programming language immediately after BlackCat, Hive, Luna, and RansomExx.
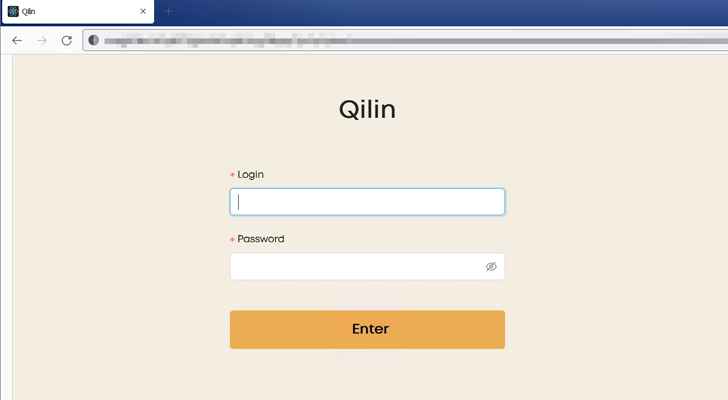
Agenda, attributed to an operator named Qilin, is a ransomware-as-a-provider (RaaS) group that has been connected to a spate of attacks mostly concentrating on producing and IT industries throughout unique countries.
A past edition of the ransomware, created in Go and tailored for just about every victim, singled out healthcare and instruction sectors in international locations like Indonesia, Saudi Arabia, South Africa, and Thailand.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

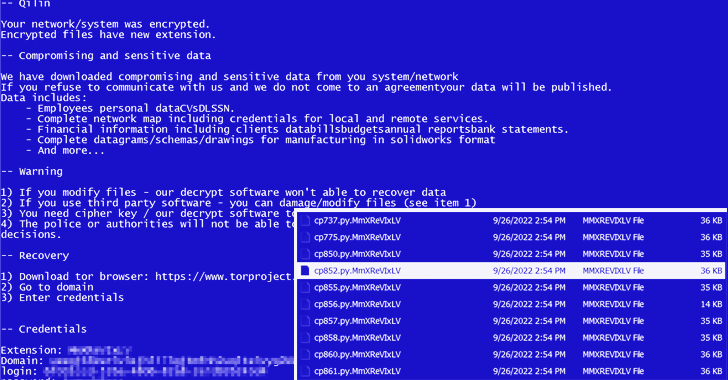
Agenda, like Royal ransomware, expands on the idea of partial encryption (aka intermittent encryption) by configuring parameters that are used to establish the percentage of file written content to be encrypted.
“This tactic is becoming much more preferred among the ransomware actors as it lets them encrypt faster and prevent detections that closely count on study/compose file functions,” a team of researchers from Trend Micro said in a report last week.
An evaluation of the ransomware binary reveals that encrypted information are given the extension “MmXReVIxLV,” in advance of proceeding to fall the ransom notice in just about every listing.
In addition, the Rust edition of Agenda is capable of terminating the Windows AppInfo process and disabling Person Account Handle (UAC), the latter of which assists mitigate the impact of malware by demanding administrative accessibility to start a system or task.
“At current, its menace actors appear to be migrating their ransomware code to Rust as new samples continue to deficiency some options seen in the original binaries created in the Golang variant of the ransomware,” the researchers pointed out.
“Rust language is getting much more well-known between danger actors as it is far more tough to examine and has a lower detection charge by antivirus engines.”
Identified this posting fascinating? Follow us on Twitter and LinkedIn to examine a lot more special content we publish.
Some areas of this post are sourced from:
thehackernews.com

 API Vulnerabilities Discovered in LEGO Marketplace
API Vulnerabilities Discovered in LEGO Marketplace