A new Android malware strain named CherryBlos has been noticed earning use of optical character recognition (OCR) procedures to gather sensitive information stored in pictures.
CherryBlos, for every Trend Micro, is dispersed by way of bogus posts on social media platforms and will come with capabilities to steal cryptocurrency wallet-linked credentials and act as a clipper to substitute wallet addresses when a sufferer copies a string matching a predefined format is copied to the clipboard.
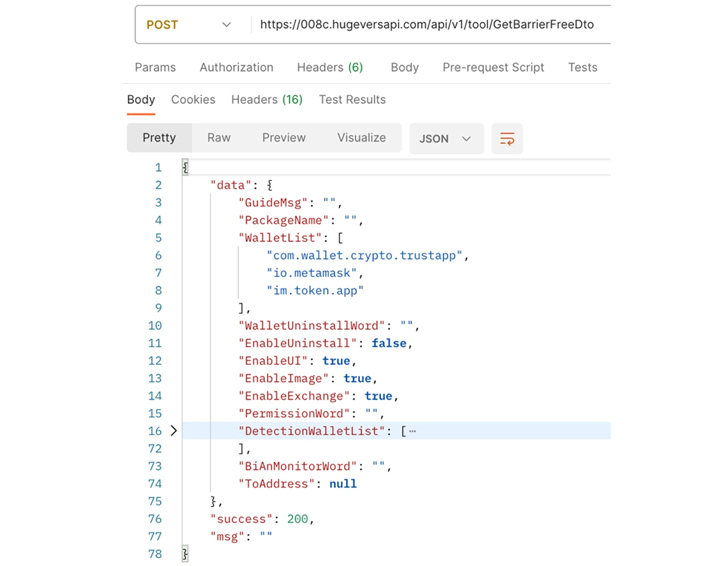
When installed, the applications request users’ permissions to grant it accessibility permissions, which lets it to immediately grant by itself further permissions as required. As a defense evasion evaluate, buyers trying to kill or uninstall the app by getting into the Options application are redirected back to the house screen.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Aside from exhibiting fake overlays on major of respectable crypto wallet apps to steal qualifications and make fraudulent fund transfers to an attacker-controlled tackle, CherryBlos utilizes OCR to figure out potential mnemonic phrases from photos and images saved on the unit, the outcomes of which are periodically uploaded to a distant server.
The achievement of the marketing campaign banking companies on the probability that end users are inclined to just take screenshots of the wallet recovery phrases on their products.
Pattern Micro reported it also located an app produced by the CherryBlos menace actors on the Google Play Keep but without the malware embedded into it. The application, named Synthnet, has given that been taken down by Google.
The risk actors also appear to share overlaps with a further action set involving 31 scam funds-earning apps, dubbed FakeTrade, hosted on the formal application marketplace based mostly on the use of shared network infrastructure and app certificates.
Most of the applications had been uploaded to the Play Retailer in 2021 and have been found to goal Android consumers in Malaysia, Vietnam, Indonesia, Philippines, Uganda, and Mexico.
“These apps declare to be e-commerce platforms that assure enhanced earnings for people by means of referrals and leading-ups,” Pattern Micro claimed. “Even so, buyers will be unable withdraw their cash when they attempt to do so.”
The disclosure arrives as McAfee comprehensive a SMS phishing marketing campaign against Japanese Android buyers that masquerades as a electricity and drinking water infrastructure organization to infect the products with malware termed SpyNote. The campaign took area in early June 2023.
“Right after launching the malware, the application opens a faux options display screen and prompts the user to permit the Accessibility aspect,” McAfee researcher Yukihiro Okutomi claimed final 7 days.
“By enabling the Accessibility assistance, the malware disables battery optimization so that it can run in the background and instantly grants unfamiliar supply set up authorization to install a further malware with out the user’s information.”
It really is no surprise that malware authors continually search for new methods to entice victims and steal sensitive data in the ever-evolving cyber danger landscape.
Google, very last 12 months, began getting techniques to suppress the misuse of accessibility APIs by rogue Android apps to covertly assemble data from compromised products by blocking sideloaded applications from employing accessibility capabilities entirely.
Upcoming WEBINARShield Against Insider Threats: Grasp SaaS Security Posture Management
Nervous about insider threats? We’ve acquired you protected! Be part of this webinar to discover sensible techniques and the secrets and techniques of proactive security with SaaS Security Posture Administration.
Be a part of Now
But stealers and clippers just symbolize 1 of the a lot of forms of malware – this sort of as spyware and stalkerware – that are applied to monitor targets and obtain facts of fascination, posing severe threats to personal privacy and security.
New investigate revealed this week uncovered that a surveillance app known as SpyHide is stealthily accumulating personal phone info from just about 60,000 Android products all over the globe given that at least 2016.
“Some of the users (operators) have many gadgets connected to their account, with some having as considerably as 30 equipment they’ve been looking at more than a course of a number of many years, spying on every person in their lives,” a security researcher, who goes by the name maia arson crimew, mentioned.
It is therefore vital for buyers to stay vigilant when downloading apps from unverified sources, verify developer information, and scrutinize app critiques to mitigate prospective pitfalls.
The truth that there is almost nothing halting danger actors from producing bogus developer accounts on the Play Retail store to distribute malware hasn’t long gone unnoticed by Google.
Earlier this thirty day period, the search big introduced that it will have to have all new developer accounts registering as an corporation to supply a valid D-U-N-S quantity assigned by Dun & Bradstreet prior to submitting applications in an energy to develop consumer have confidence in. The alter goes into outcome on August 31, 2023.
Discovered this post attention-grabbing? Abide by us on Twitter and LinkedIn to browse a lot more distinctive information we article.
Some sections of this post are sourced from:
thehackernews.com


 RFP Template for Browser Security
RFP Template for Browser Security