Malicious actors are employing a respectable Rust-dependent injector known as Freeze.rs to deploy a commodity malware identified as XWorm in sufferer environments.
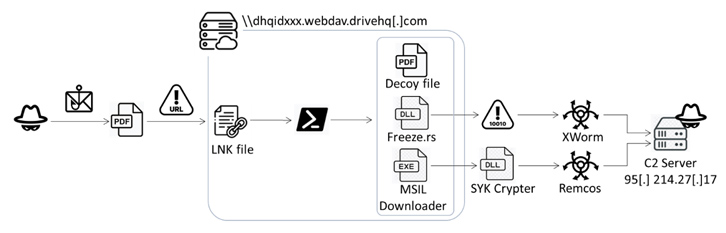
The novel attack chain, detected by Fortinet FortiGuard Labs on July 13, 2023, is initiated via a phishing email containing a booby-trapped PDF file. It has also been made use of to introduce Remcos RAT by implies of a crypter identified as SYK Crypter, which was 1st documented by Morphisec in May 2022.
“This file redirects to an HTML file and utilizes the ‘search-ms’ protocol to obtain an LNK file on a distant server,” security researcher Cara Lin reported. “Upon clicking the LNK file, a PowerShell script executes Freeze.rs and SYK Crypter for further offensive steps.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Freeze.rs, launched on May perhaps 4, 2023, is a open-resource red teaming device from Optiv that functions as a payload development software used for circumventing security solutions and executing shellcode in a stealthy method.

“Freeze.rs makes use of a number of procedures to not only eliminate Userland EDR hooks, but to also execute shellcode in this kind of a way that it circumvents other endpoint monitoring controls,” according to a description shared on GitHub.
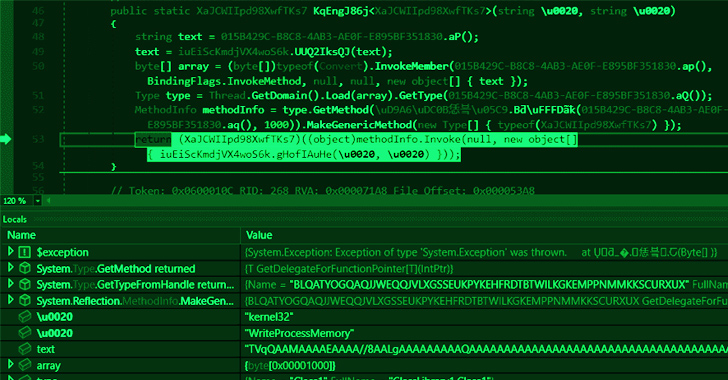
SYK Crypter, on the other hand, is a device utilized to dispersed a vast range of malware family members this sort of as AsyncRAT, NanoCore RAT, njRAT, QuasarRAT, RedLine Stealer, and Warzone RAT (aka Ave Maria). It’s retrieved from the Discord articles supply network (CDN) by indicates of a .NET loader attached to emails that masquerades as benign invest in orders.
“This attack chain delivers a crypter that is persistent, capabilities numerous layers of obfuscation, and takes advantage of polymorphism to preserve its capability to steer clear of detection by security methods,” Morphisec researcher Hido Cohen discussed.
It is really well worth noting that the abuse of the “lookup-ms” URI protocol handler was not too long ago highlighted by Trellix, which unearthed an infection sequences bearing HTML or PDF attachments to operate queries on an attacker-managed server and listing malicious files in the Windows File Explorer as if they are regional look for results.

The findings from Fortinet are no different in that the data files are camouflaged as PDF data files but are basically LNK information that execute a PowerShell script to launch the Rust-centered injector, even though exhibiting a decoy PDF document.
In the final stage, the injected shellcode is decrypted to execute the XWorm distant accessibility trojan and harvest delicate data, such as equipment information and facts, screenshots, and keystrokes, and remotely regulate the compromised machine.
The fact that a three-month-previous system is by now becoming weaponized in attacks symbolizes the speedy adoption of offensive instruments by malicious actors to meet up with their aims.
Which is not all. The PowerShell script, other than loading the injector, is configured to operate yet another executable, which features as a dropper by getting in touch with a remote server to fetch the SYK Crypter containing the encrypted Remcos RAT malware.
“The combination of XWorm and Remcos generates a formidable trojan with an array of destructive functionalities,” Lin mentioned. “The C2 server’s site visitors report […] reveals Europe and North America as the major targets of this malicious campaign.”
Found this post interesting? Comply with us on Twitter and LinkedIn to examine a lot more special information we submit.
Some components of this short article are sourced from:
thehackernews.com

 New Statc Stealer Malware Emerges: Your Sensitive Data at Risk
New Statc Stealer Malware Emerges: Your Sensitive Data at Risk