A crew of academic researchers—who beforehand manufactured the headlines previously this yr for uncovering intense security issues in the 4G LTE and 5G networks—today presented a new assault termed ‘ReVoLTE,’ that could enable distant attackers crack the encryption used by VoLTE voice calls and spy on qualified phone phone calls.
The assault does not exploit any flaw in the Voice more than LTE (VoLTE) protocol in its place, it leverages weak implementation of the LTE cell network by most telecommunication companies in practice, enabling an attacker to eavesdrop on the encrypted phone calls designed by specific victims.
VoLTE or Voice above Lengthy Expression Evolution protocol is a normal higher-pace wi-fi conversation for cellular phones and info terminals, such as Internet of items (IoT) products and wearables, deploying 4G LTE radio access technology.
The crux of the trouble is that most mobile operators frequently use the similar keystream for two subsequent calls inside of a person radio connection to encrypt the voice facts involving the phone and the similar base station, i.e., mobile phone tower.
Therefore, the new ReVoLTE attack exploits the reuse of the exact same keystream by vulnerable foundation stations, enabling attackers to decrypt the contents of VoLTE powered voice calls in the pursuing scenario.
Even so, reuse of a predictable keystream is not new and was to start with pointed out by Raza & Lu, but the ReVoLTE assault turns it into a realistic attack.
How Does the ReVoLTE Assault Perform?
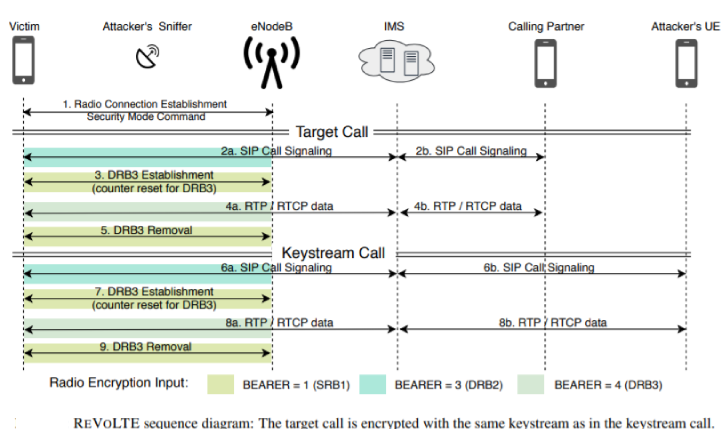
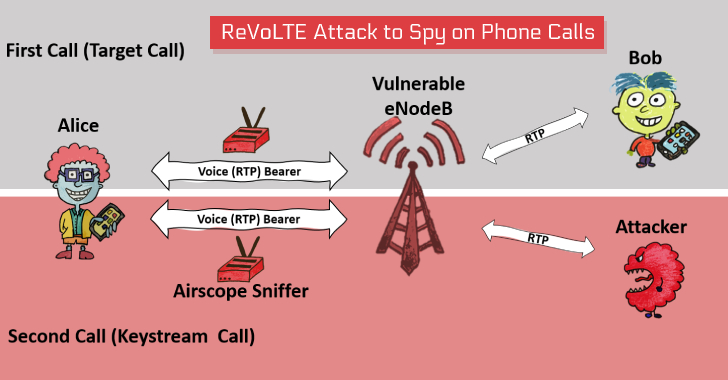
To initiate this assault, the attacker should be connected to the similar foundation station as the target and put a downlink sniffer to monitor and history a ‘targeted call’ built by the victim to a person else that wants to be decrypted later, as portion of the to start with stage of ReVoLTE assault.
The moment the victim hangs up the ‘targeted contact,’ the attacker is needed to get in touch with the victim, typically within just 10 seconds right away, which would drive the susceptible network into initiating a new call concerning sufferer and attacker on the very same radio relationship as employed by prior specific phone.
“The keystream reuse takes place when the goal and keystream simply call use the exact same user-aircraft encryption crucial. As this key is up-to-date for each new radio connection, the attacker must guarantee that the initially packet of the keystream simply call comes within just the lively stage following the target phone,” the researchers reported.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The moment linked, as section of the next stage, the attacker wants to have interaction the victim into a discussion and history it in plaintext, which would support the attacker afterwards reverse compute the keystream used by the subsequent simply call.
In accordance to researchers, XOR-ing the keystreams with the corresponding encrypted frame of the targeted call captured in the first section decrypts its articles, making it possible for attackers to pay attention to what dialogue its victim had in the former phone phone.
“As this outcomes in the same keystream, all RTP knowledge is encrypted in the identical way as the voice knowledge of the focus on simply call. As before long as a enough quantity of keystream facts was generated, the adversary cancels the get in touch with,” the paper reads.
Having said that, the length of the next contact need to be increased than or equal to the initial contact in order to decrypt each individual body in any other case, it can only decrypt a section of the conversation.
“It is important to notice that the attacker has to interact the victim in a lengthier dialogue. The for a longer period he/she talked to the target, the much more articles of the former communication he/she can decrypt,” the paper reads.
“Every single body is associated with a rely and encrypted with an personal keystream that we extract in the course of the keystream computation. As the identical rely generates the very same keystream, the count synchronizes the keystreams with encrypted frames of the concentrate on contact. XOR-ing the keystreams with the corresponding encrypted body decrypts the target get in touch with.”
“As we aim to decrypt the total contact, the keystream get in touch with should be as prolonged as the target contact to present a enough amount of packets, as otherwise we can only decrypt a component of the dialogue.”
Detecting ReVoLTE Attack and Demonstration
To show the practical feasibility of the ReVoLTE attack, the group of academics from Ruhr University Bochum executed an close-to-finish edition of the assault within just a business, susceptible network and professional phones.
The workforce utilised the downlink analyzer Airscope by Software package Radio Method to sniff the encrypted site visitors and 3 Android-primarily based phones to acquire the recognised-plaintext at the attacker’s phone. It then when compared the two recorded discussions, decided the encryption key, and finally decrypted a part of the preceding phone.
You can see the demo video clip of the ReVoLTE assault, which, according to the researchers, could price tag much less than $7000 to attackers for environment up the attack and, ultimately, decrypting downlink targeted visitors.
The team tested a range of randomly picked radio cells throughout Germany to decide the scope of the issue and observed that it influences 12 out of 15 foundation stations in Germany, but scientists explained the security hole also impacts other international locations.
Researchers notified the affected German foundation station operators about the ReVoLTE attack by the GSMA Coordinated Vulnerability Disclosure Programme system in early December 2019, and the operators managed to deploy the patches by the time of publication.
Considering the fact that the issue also affects a huge quantity of companies worldwide, researchers launched an open up source Android app, termed ‘Mobile Sentinel,’ that you can use to detect irrespective of whether their 4G network and base stations are vulnerable to the ReVoLTE attack or not.
Researchers—David Rupprecht, Katharina Kohls and Thorsten Holz of RUB University Bochum and Christina Pöpper of NYU Abu Dhabi—have also introduced a dedicated internet site and study paper PDF, titled “Simply call Me Possibly: Eavesdropping Encrypted LTE Phone calls With REVOLTE,” detailing the ReVoLTE assault, exactly where you can find extra aspects.
Uncovered this short article exciting? Stick to THN on Fb, Twitter and LinkedIn to study additional special content we write-up.

 Phishing Tactic Targets Verizon Users’ Qualifications
Phishing Tactic Targets Verizon Users’ Qualifications