Security scientists have outlined a new method that renders a remote timing-based facet-channel assault more helpful regardless of the network congestion between the adversary and the concentrate on server.
Remote timing assaults that get the job done above a network connection are predominantly affected by variations in network transmission time (or jitter), which, in change, depends on the load of the network connection at any offered stage in time.
But because measuring the time taken to execute cryptographic algorithms is crucial to carrying out a timing attack and as a result leak details, the jitter on the network route from the attacker to the server can make it impractical to efficiently exploit timing facet-channels that depend on a smaller distinction in execution time.
The new technique, named Timeless Timing Attacks (TTAs) by scientists from DistriNet Investigate Team and New York University Abu Dhabi, rather leverages multiplexing of network protocols and concurrent execution by programs, thus making the attacks immune to network circumstances.
“These concurrency-primarily based timing attacks infer a relative timing distinction by analyzing the purchase in which responses are returned, and consequently do not count on any absolute timing information,” the scientists reported.
Utilizing HTTP/2’s Request Multiplexing to Lessen Jitter
Not like the standard timing-dependent attacks, whereby the execution instances are measured independently and sequentially, the latest procedure makes an attempt to extract info from the buy and the relative timing big difference in between two concurrently executed requests devoid of relying on any timing information.
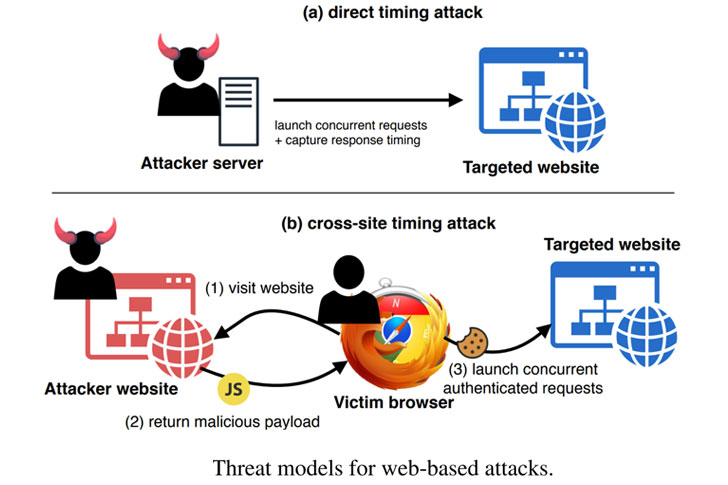
To do so, a terrible actor initiates a pair of HTTP/2 requests to the target server either straight or using a cross-website — these kinds of as a malicious advertisement or tricking the victim into checking out an attacker-managed web page — to launch requests to the server by means of JavaScript code.
The server returns a end result that incorporates the big difference in response time involving the next ask for and the first. The TTA, then, operates by using into account whether this variance is optimistic or detrimental, wherever good implies that the processing time of the initially ask for usually takes fewer time than processing the next ask for.
“On web servers hosted about HTTP/2, we discover that a timing change as tiny as 100ns can be properly inferred from the reaction get of about 40,000 request-pairs,” the researchers noted.
“The smallest timing variation that we could notice in a classic timing assault more than the Internet was 10μs, 100 instances greater than our concurrency-based attack.”
A limitation of this solution is that attacks aimed at servers using HTTP/1.1 can’t exploit the protocol to coalesce several requests in a one network packet, thereby demanding that a concurrent timing attack be done using several connections rather of sending all requests in excess of the exact connection.
This stems from HTTP/1.1’s use of head-of-line (HOL) blocking, which results in all requests about the same relationship to be handled sequentially, while HTTP/2 addresses this issue by way of ask for multiplexing.
Presently, 37.46% of all desktop websites are served more than HTTP/2, a number that raises even more to 54.04% for web-sites that aid HTTPS. Even though this tends to make a large amount of internet sites vulnerable to TTAs, the researchers take note that several of them count on written content supply networks (CDN), these types of as Cloudflare, which nonetheless takes advantage of HTTP/1.1 for connections involving the CDN and the origin site.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Tor Onion Support and Wi-Fi EAP-PWD Vulnerable
But in a twist, the scientists located that concurrency-centered timing assaults can also be deployed from Tor onion products and services, such as all those that only help HTTP/1.1, allowing an attacker to generate two Tor connections to a distinct onion provider, and then concurrently send out a ask for on every of the connections to evaluate a timing change of 1μs.
That’s not all. The EAP-PWD authentication method, which employs a shared password among the server and supplicant when connecting to Wi-Fi networks, is rendered susceptible to dictionary assaults by exploiting a timing leak in the Dragonfly handshake protocol to expose the facts about the password itself.
Though timing attacks can be countered by making certain continuous-time execution, it’s much easier mentioned than carried out, in particular for applications that rely on 3rd-social gathering factors. Alternatively, the researchers propose introducing a random delay to incoming requests and make sure that distinctive requests are not merged in a solitary packet.
This is not the first time distant timing attacks have been employed to leak sensitive data. Researchers have formerly shown it can be possible to exploit cache aspect-channels to sniff out SSH passwords from Intel CPU cache (NetCAT) and even reach Spectre-like speculative execution more than a network link (NetSpectre).
“Since the NetSpectre attacks focus on applications above the network layer, an attacker could, in principle, leverage our concurrency-centered timing attacks to strengthen the timing precision,” the researchers mentioned.
The results will be offered at the USENIX Security Symposium later this 12 months. The researchers have also published a Python-based mostly resource to test HTTP/2 servers for TTA vulnerabilities.
Discovered this short article fascinating? Adhere to THN on Fb, Twitter and LinkedIn to browse far more exclusive written content we publish.


 Twitter Confirms Spear-Phishing Attack Brought about Account Takeover
Twitter Confirms Spear-Phishing Attack Brought about Account Takeover