Cybersecurity researchers have disclosed a new refined Android malware termed FjordPhantom that has been noticed focusing on consumers in Southeast Asian nations like Indonesia, Thailand, and Vietnam because early September 2023.
“Spreading mainly by messaging services, it combines app-centered malware with social engineering to defraud banking prospects,” Oslo-centered mobile application security firm Promon mentioned in an investigation released Thursday.
Propagated mostly by way of email, SMS, and messaging apps, attack chains trick recipients into downloading a purported banking app that will come fitted with authentic attributes but also incorporates rogue factors.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Victims are then subjected to a social engineering method akin to telephone-oriented attack shipping and delivery (TOAD), which consists of contacting a bogus phone centre to obtain move-by-stage instructions for jogging the application.
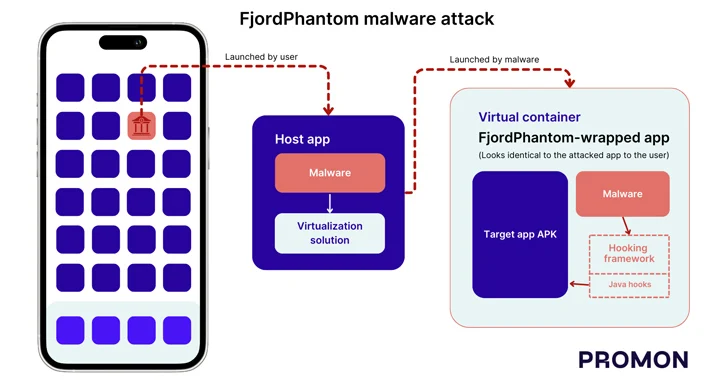
A crucial characteristic of the malware that sets it aside from other banking trojans of its form is the use of virtualization to operate destructive code in a container and fly under the radar.
The sneaky technique, Promon reported, breaks Android’s sandbox protections as it will allow diverse apps to be run on the same sandbox, enabling the malware to entry delicate info with out requiring root obtain.
“Virtualization solutions like the just one utilized by the malware can also be used to inject code into an application because the virtualization alternative initially masses its own code (and anything else identified in its app) into a new approach and then masses the code of the hosted software,” security researcher Benjamin Adolphi claimed.
In the circumstance of FjordPhantom, the host application downloaded incorporates a malicious module and the virtualization factor that is then made use of to put in and launch the embedded application of the qualified financial institution in a virtual container.

In other phrases, the bogus app is engineered to load the bank’s genuine application in a virtual container when also utilizing a hooking framework in just the natural environment to change the conduct of critical APIs to grab sensitive data from the application’s display screen programmatically and shut dialog packing containers utilised to alert destructive exercise on users’ units.
“FjordPhantom alone is published in a modular way to attack different banking applications,” Adolphi mentioned. “Based on which banking application is embedded into the malware, it will complete various attacks on these apps.”
Discovered this posting appealing? Adhere to us on Twitter and LinkedIn to read much more special content we post.
Some sections of this article are sourced from:
thehackernews.com

 Qakbot Takedown Aftermath: Mitigations and Protecting Against Future Threats
Qakbot Takedown Aftermath: Mitigations and Protecting Against Future Threats