Cybersecurity researchers have uncovered a new cloud concentrating on, peer-to-peer (P2P) worm called P2PInfect that targets susceptible Redis cases for abide by-on exploitation.
“P2PInfect exploits Redis servers running on equally Linux and Windows Operating Techniques producing it extra scalable and potent than other worms,” Palo Alto Networks Unit 42 researchers William Gamazo and Nathaniel Quist stated. “This worm is also written in Rust, a really scalable and cloud-helpful programming language.”
It is believed that as lots of as 934 distinctive Redis units may well be vulnerable to the threat. The initial regarded occasion of P2PInfect was detected on July 11, 2023.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
A notable characteristic of the worm is its potential to infects vulnerable Redis instances by exploiting a critical Lua sandbox escape vulnerability, CVE-2022-0543 (CVSS score: 10.), which has been beforehand exploited to provide numerous malware family members this kind of as Muhstik, Redigo, and HeadCrab about the previous calendar year.
The first obtain afforded by a prosperous exploitation is then leveraged to produce a dropper payload that establishes peer-to-peer (P2P) conversation to a greater P2P network and fetch supplemental malicious binaries, which include scanning computer software for propagating the malware to other uncovered Redis and SSH hosts.
“The infected occasion then joins the P2P network to give obtain to the other payloads to foreseeable future compromised Redis circumstances,” the researchers mentioned.
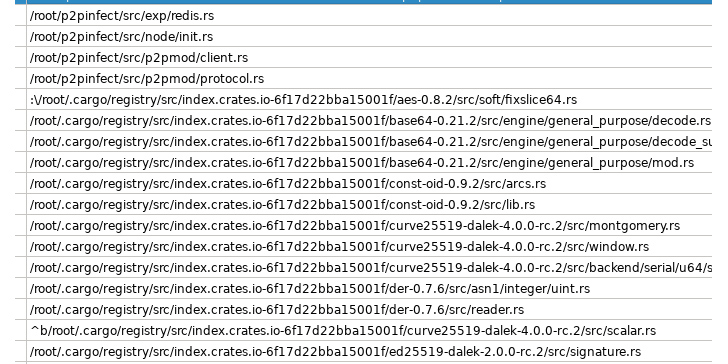
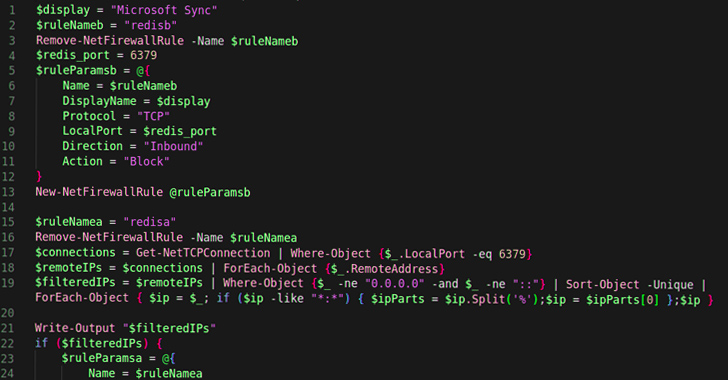
The malware also makes use of a PowerShell script to build and maintain conversation involving the compromised host and the P2P network, presenting threat actors persistent access. What is additional, the Windows taste of P2PInfect incorporates a Watch ingredient to self-update and start the new variation.
It is not immediately recognized what the finish purpose of the marketing campaign is, with Unit 42 noting that there is no definitive proof of cryptojacking irrespective of the presence of the term “miner” in the toolkit’s source code.
Upcoming WEBINARShield Towards Insider Threats: Master SaaS Security Posture Administration
Fearful about insider threats? We have got you covered! Be part of this webinar to discover practical strategies and the secrets and techniques of proactive security with SaaS Security Posture Management.
Be part of These days
The action has not been attributed to any recognized menace actor groups notorious for placing cloud environments like Adept Libra (aka TeamTNT), Aged Libra (aka Rocke), Automatic Libra (aka PURPLEURCHIN), Money Libra (aka Kinsing), Returned Libra (aka 8220 Gang), or Thief Libra (aka WatchDog).
The advancement will come as misconfigured and susceptible cloud assets are staying found out within minutes by terrible actors frequently scanning the internet to mount sophisticated attacks.
“The P2PInfect worm appears to be perfectly built with various contemporary progress decisions,” the scientists mentioned. “The layout and making of a P2P network to conduct the vehicle-propagation of malware is not a thing frequently found inside of the cloud concentrating on or cryptojacking menace landscape.”
Identified this write-up appealing? Stick to us on Twitter and LinkedIn to browse more exceptional material we write-up.
Some components of this article are sourced from:
thehackernews.com

 Microsoft Expands Cloud Logging to Counter Rising Nation-State Cyber Threats
Microsoft Expands Cloud Logging to Counter Rising Nation-State Cyber Threats