A new phishing attack probably targeting civil modern society teams in South Korea has led to the discovery of a novel distant entry trojan identified as SuperBear.
The intrusion singled out an unnamed activist, who was contacted in late August 2023 and been given a malicious LNK file from an address impersonating a member of the organization, non-gain entity Interlabs stated in a new report.
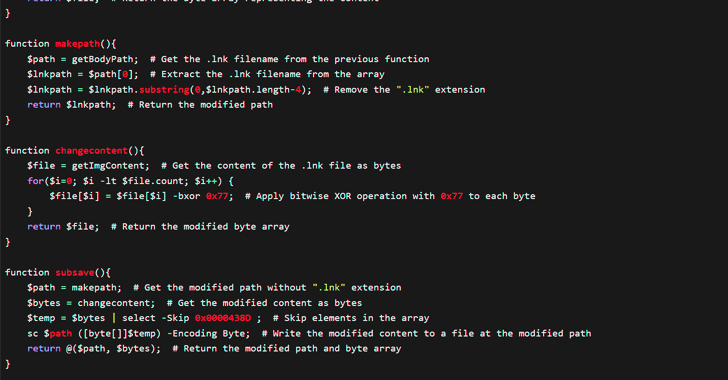
The LNK file, on execution, launches a PowerShell command to execute a Visible Primary script that, in transform, fetches the subsequent-phase payloads from a authentic but compromised WordPress website.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
This contains the Autoit3.exe binary (“solmir.pdb”) and an AutoIt script (“solmir_1.pdb”) which is launched utilizing the previous.
The AutoIt script, for its portion, performs course of action injection working with a approach hollowing technique, in which malicious code is inserted into a procedure that’s in a suspended condition.

In this situation, an occasion of Explorer.exe is spawned to inject a by no means-before-witnessed RAT referred to as SuperBear that establishes communications with a distant server to exfiltrate info, download and operate additional shell commands and dynamic-hyperlink libraries (DDLs).
“The default action for the C2 server seems to instruct purchasers to exfiltrate and process procedure info,” Interlab researcher Ovi Liber mentioned, noting that the malware is so named for the reason that “the destructive DLL will check out to create a random filename for it, and if it cannot it will be named ‘SuperBear.'”
The attack has been loosely pinned on a North Korean country-condition actor named Kimsuky (aka APT43 or Emerald Sleet, Nickel Kimball, and Velvet Chollima), citing similarities with the initial attack vector and the PowerShell instructions utilized.
Earlier this February, Interlab also unveiled that North Korean country-condition actors specific a journalist in South Korea with Android malware dubbed RambleOn as component of a social engineering marketing campaign.
Located this article exciting? Follow us on Twitter and LinkedIn to read through additional special content we put up.
Some elements of this write-up are sourced from:
thehackernews.com

 It’s a Zero-day? It’s Malware? No! It’s Username and Password
It’s a Zero-day? It’s Malware? No! It’s Username and Password