Companies running in the Latin American (LATAM) location are the focus on of a new Windows-centered banking trojan called TOITOIN given that May 2023.
“This complex marketing campaign employs a trojan that follows a multi-staged an infection chain, making use of specifically crafted modules all over each and every stage,” Zscaler researchers Niraj Shivtarkar and Preet Kamal explained in a report posted very last 7 days.
“These modules are tailor made built to have out malicious activities, this sort of as injecting destructive code into distant processes, circumventing User Account Regulate by means of COM Elevation Moniker, and evading detection by Sandboxes through clever approaches like process reboots and father or mother approach checks.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The 6-stage endeavor has all the hallmarks of a perfectly-crafted attack sequence, commencing with a phishing email containing an embedded website link that points to a ZIP archive hosted on an Amazon EC2 instance to evade area-primarily based detections.
The email messages leverage an bill-themed entice to trick unwitting recipients into opening them, therefore activating the an infection. Inside the ZIP archive is a downloader executable that is engineered to established up persistence by usually means of an LNK file in the Windows Startup folder and talk with a distant server to retrieve 6 upcoming-phase payloads in the variety of MP3 documents.
The downloader is also dependable for producing a Batch script that restarts the system after a 10-next timeout. This is performed so as to “evade sandbox detection considering that the destructive steps happen only just after the reboot,” the researchers claimed.
Provided amongst the fetched payloads is “icepdfeditor.exe,” a valid signed binary by ZOHO Corporation Personal Restricted, which, when executed, sideloads a rogue DLL (“ffmpeg.dll”) codenamed the Krita Loader.
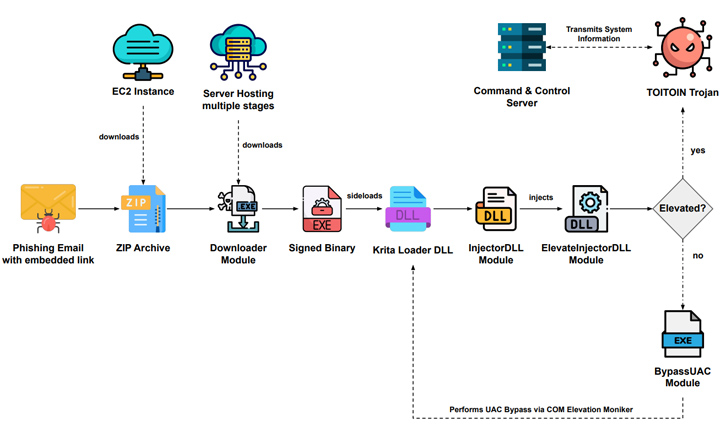
The loader, for its aspect, is designed to decode a JPG file downloaded together with the other payloads and launch yet another executable regarded as the InjectorDLL module that reverses a 2nd JPG file to variety what’s named the ElevateInjectorDLL module.
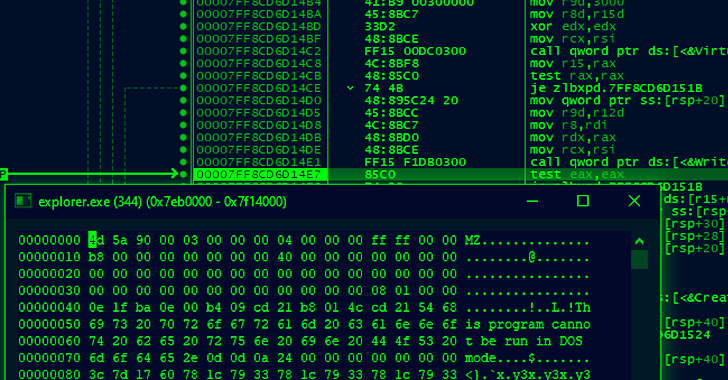
The InjectorDLL component subsequently moves to inject ElevateInjectorDLL into the “explorer.exe” procedure, next which a User Account Regulate (UAC) bypass is carried out, if needed, to elevate the method privileges and the TOITOIN Trojan is decrypted and injected into the “svchost.exe” course of action.
Impending WEBINAR🔐 Privileged Accessibility Management: Discover How to Conquer Important Challenges
Learn distinct ways to conquer Privileged Account Administration (PAM) difficulties and stage up your privileged obtain security strategy.
Reserve Your Place
“This system enables the malware to manipulate method information and execute instructions with elevated privileges, facilitating further more destructive actions,” the scientists defined.
TOITOIN comes with abilities to acquire process data as properly as harvest info from set up web browsers these kinds of as Google Chrome, Microsoft Edge and Internet Explorer, Mozilla Firefox, and Opera. Moreover, it checks for the presence of Topaz On the web Fraud Detection (OFD), an anti-fraud module integrated into banking platforms in the LATAM region.
The mother nature of the responses from the command-and-regulate (C2) server is presently not identified owing to the reality that the server is no more time out there.
“By misleading phishing e-mails, intricate redirect mechanisms, and domain diversification, the risk actors correctly provide their destructive payload,” the scientists stated. “The multi-staged infection chain observed in this campaign consists of the use of custom made-produced modules that employ many evasion tactics and encryption solutions.”
Found this post intriguing? Stick to us on Twitter and LinkedIn to browse far more exclusive content material we article.
Some parts of this article are sourced from:
thehackernews.com

 Global Retailers Must Keep an Eye on Their SaaS Stack
Global Retailers Must Keep an Eye on Their SaaS Stack