A new variant of an Apple macOS malware referred to as XLoader has surfaced in the wild, masquerading its destructive functions less than the guise of an business office productivity application known as “OfficeNote.”
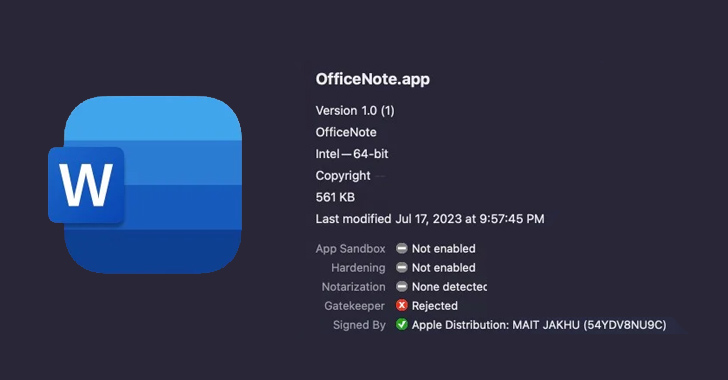
“The new version of XLoader is bundled inside of a common Apple disk impression with the identify OfficeNote.dmg,” SentinelOne security scientists Dinesh Devadoss and Phil Stokes said in a Monday examination. “The application contained within just is signed with the developer signature MAIT JAKHU (54YDV8NU9C).”
XLoader, very first detected in 2020, is deemed a successor to Formbook and is an information stealer and keylogger presented below the malware-as-a-service (MaaS) product. A macOS variant of the malware emerged in July 2021, distributed as a Java program in the sort of a compiled .JAR file.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

“This sort of files demand the Java Runtime Atmosphere, and for that cause the malicious .jar file will not execute on a macOS install out of the box, because Apple stopped shipping and delivery JRE with Macs over a decade in the past,” the cybersecurity firm noted at the time.
The most recent iteration of XLoader receives close to this limitation by switching to programming languages this kind of as C and Objective C, with the disk graphic file signed on July 17, 2023. Apple has considering that revoked the signature.
SentinelOne mentioned it detected many submissions of the artifact on VirusTotal all by way of the month of July 2023, indicating a popular campaign.
“Ads on crimeware message boards supply the Mac edition for rental at $199/thirty day period or $299/3 months,” the researchers mentioned. “Curiously, this is somewhat high priced when compared to Windows variants of XLoader, which go for $59/month and $129/3 months.”
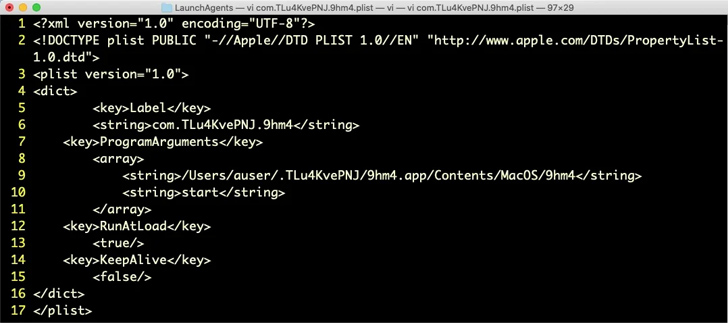
As soon as executed, OfficeNote throws an error concept expressing it “won’t be able to be opened due to the fact the original product can’t be located,” but, in truth, it installs a Start Agent in the qualifications for persistence.

XLoader is intended to harvest clipboard information as effectively as facts stored in the directories affiliated with web browsers this kind of as Google Chrome and Mozilla Firefox. Safari, nevertheless, is not focused.
Aside from getting steps to evade examination equally manually and by automatic solutions, the malware is configured to run slumber instructions to hold off its execution and avoid boosting any red flags.
“XLoader carries on to current a menace to macOS people and corporations,” the scientists concluded.
“This latest iteration masquerading as an business efficiency application reveals that the targets of curiosity are obviously end users in a doing the job natural environment. The malware tries to steal browser and clipboard secrets that could be utilised or sold to other danger actors for further compromise.”
Located this report fascinating? Abide by us on Twitter and LinkedIn to browse much more exclusive content we put up.
Some components of this article are sourced from:
thehackernews.com

 Ivanti Warns of Critical Zero-Day Flaw Being Actively Exploited in Sentry Software
Ivanti Warns of Critical Zero-Day Flaw Being Actively Exploited in Sentry Software