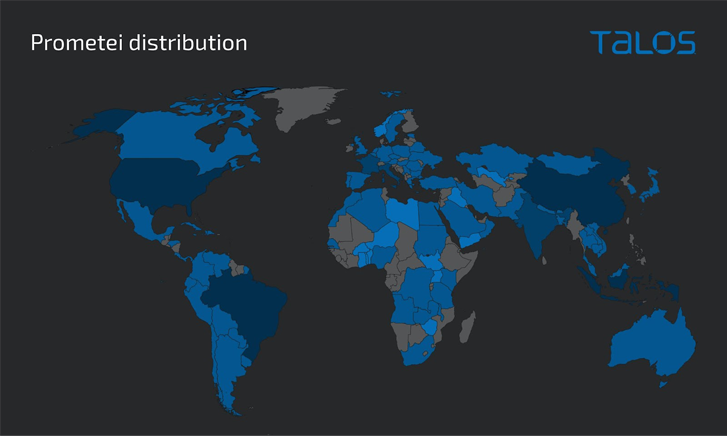
An updated variation of a botnet malware referred to as Prometei has contaminated extra than 10,000 systems throughout the world because November 2022.
The infections are each geographically indiscriminate and opportunistic, with a the greater part of the victims described in Brazil, Indonesia, and Turkey.
Prometei, initially noticed in 2016, is a modular botnet that attributes a massive repertoire of components and many proliferation procedures, some of which also consist of the exploitation of ProxyLogon Microsoft Trade Server flaws.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
It is really also notable for steering clear of hanging Russia, suggesting that the danger actors behind the operation are possible based in the nation.
The cross-system botnet’s motivations are economic, mostly leveraging its pool of infected hosts to mine cryptocurrency and harvest credentials.
The newest variant of Prometei (referred to as v3) enhances upon its present capabilities to challenge forensic analysis and even more burrow its accessibility on sufferer equipment, Cisco Talos said in a report shared with The Hacker Information.
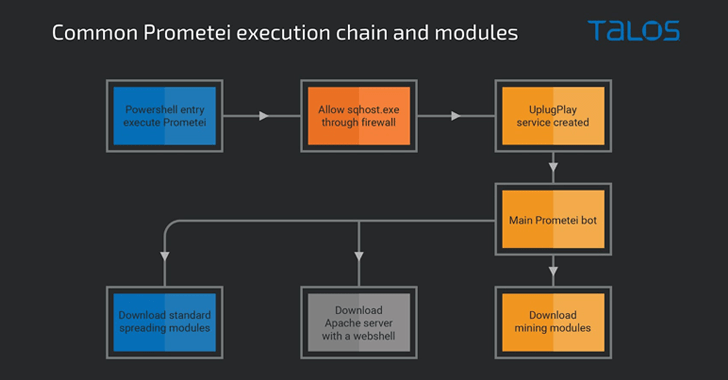
The attack sequence proceeds thus: On attaining a productive foothold, a PowerShell command is executed to download the botnet payload from a remote server. Prometei’s major module is then utilized to retrieve the genuine crypto-mining payload and other auxiliary factors on the method.
Some of these guidance modules purpose as spreader courses developed to propagate the malware through Remote Desktop Protocol (RDP), Safe Shell (SSH), and Server Information Block (SMB).
WEBINARDiscover the Hidden Potential risks of 3rd-Party SaaS Apps
Are you informed of the risks involved with 3rd-party app entry to your company’s SaaS apps? Be part of our webinar to study about the forms of permissions remaining granted and how to decrease risk.
RESERVE YOUR SEAT
Prometei v3 is also noteworthy for applying a domain technology algorithm (DGA) to make out its command-and-management (C2) infrastructure. It even more packs in a self-update system and an expanded set of instructions to harvest delicate details and commandeer the host.
Previous but not minimum, the malware deploys an Apache web server that’s bundled with a PHP-based web shell, which is able of executing Base64-encoded commands and carrying out file uploads.
“This modern addition of new abilities [indicates] that the Prometei operators are repeatedly updating the botnet and including performance,” Talos researchers Andrew Windsor and Vanja Svajcer said.
Identified this posting exciting? Observe us on Twitter and LinkedIn to browse a lot more special written content we submit.
Some pieces of this article are sourced from:
thehackernews.com

 China-linked Hackers Targeting Unpatched SonicWall SMA Devices with Malware
China-linked Hackers Targeting Unpatched SonicWall SMA Devices with Malware