Consumers of Advanced Customized Fields plugin for WordPress are currently being urged to update model 6.1.6 next the discovery of a security flaw.
The issue, assigned the identifier CVE-2023-30777, relates to a scenario of mirrored cross-web page scripting (XSS) that could be abused to inject arbitrary executable scripts into normally benign websites.
The plugin, which is available the two as a absolutely free and pro edition, has over two million energetic installations. The issue was identified and described to the maintainers on Could 2, 2023.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“This vulnerability makes it possible for any unauthenticated person from thieving delicate facts to, in this situation, privilege escalation on the WordPress website by tricking a privileged person to take a look at the crafted URL path,” Patchstack researcher Rafie Muhammad mentioned.

Mirrored XSS attacks generally happen when victims are tricked into clicking on a bogus website link sent via email or a further route, triggering the destructive code to be despatched to the vulnerable website, which demonstrates the attack again to the user’s browser.
This aspect of social engineering indicates that mirrored XSS does not have the identical attain and scale as stored XSS attacks, prompting danger actors to distribute the destructive hyperlink to as several victims as feasible.
“[A reflected XSS attack] is normally a final result of incoming requests not staying adequately sanitized, which will allow for the manipulation of a web application’s capabilities and the activation of malicious scripts,” Imperva notes.
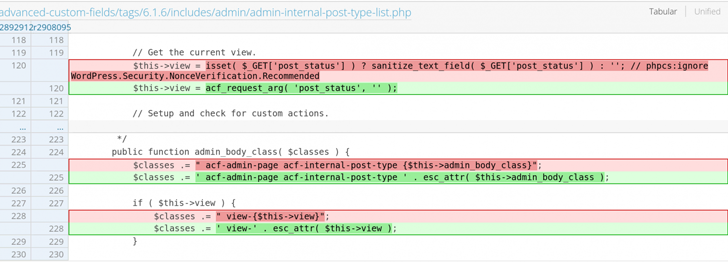
It truly is worthy of noting that CVE-2023-30777 can be activated on a default installation or configuration of Highly developed Customized Fields, even though it’s only achievable to do so from logged-in customers who have obtain to the plugin.
The improvement comes as Craft CMS patched two medium-severity XSS flaws (CVE-2023-30177 and CVE-2023-31144) that could be exploited by a risk actor to serve destructive payloads.
Forthcoming WEBINARLearn to Stop Ransomware with Serious-Time Safety
Join our webinar and learn how to stop ransomware attacks in their tracks with genuine-time MFA and support account defense.
Save My Seat!
It also follows the disclosure of a further XSS flaw in the cPanel solution (CVE-2023-29489, CVSS score: 6.1) that could be exploited with out any authentication to run arbitrary JavaScript.
“An attacker can not only attack the administration ports of cPanel but also the programs that are managing on port 80 and 443,” Assetnote’s Shubham Shah stated, incorporating it could allow an adversary to hijack a legitimate user’s cPanel session.
“After performing on behalf of an authenticated consumer of cPanel, it is normally trivial to upload a web shell and attain command execution.”
Observed this short article interesting? Observe us on Twitter and LinkedIn to read through more unique written content we write-up.
Some pieces of this write-up are sourced from:
thehackernews.com


 Dallas Police Department Compromised in Ransomware Attack
Dallas Police Department Compromised in Ransomware Attack