A new malware pressure termed ZenRAT has emerged in the wild which is distributed by means of bogus installation deals of the Bitwarden password manager.
“The malware is particularly focusing on Windows consumers and will redirect individuals utilizing other hosts to a benign web website page,” organization security firm Proofpoint explained in a technical report. “The malware is a modular distant obtain trojan (RAT) with info thieving abilities.”
ZenRAT is hosted on bogus websites pretending to be related with Bitwarden, though it is uncertain as to how targeted visitors is remaining directed to the domains. This sort of malware has been propagated via phishing, malvertising, or Web optimization poisoning attacks in the past.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The payload (Bitwarden-Installer-version-2023-7-1.exe), downloaded from crazygameis[.]com, is a trojanized variation of the standard Bitwarden installation bundle that includes a malicious .NET executable (ApplicationRuntimeMonitor.exe).
A noteworthy aspect of the marketing campaign is that people who conclude up viewing the misleading site from non-Windows units are redirected to a cloned opensource.com posting revealed in March 2018 about “How to regulate your passwords with Bitwarden, a LastPass substitute.”
Further, Windows customers clicking on downloading inbound links marked for Linux or macOS on the Downloads site are redirected to the authentic Bitwarden internet site, vault.bitwarden.com.
An assessment of the installer’s metadata reveals makes an attempt on the aspect of the menace actor to masquerade the malware as Piriform’s Speccy, a freeware Windows utility to exhibit hardware and application information and facts.
The digital signature employed to indication the executable is not only invalid, but also claims to be signed by Tim Kosse, a well-regarded German pc scientist acknowledged for establishing the free cross-platform FTP program FileZilla.
ZenRAT, once launched, gathers specifics about the host, like CPU title, GPU title, working system edition, browser credentials, and set up applications and security computer software, to a command-and-regulate (C2) server (185.186.72[.]14) operated by the menace actors.
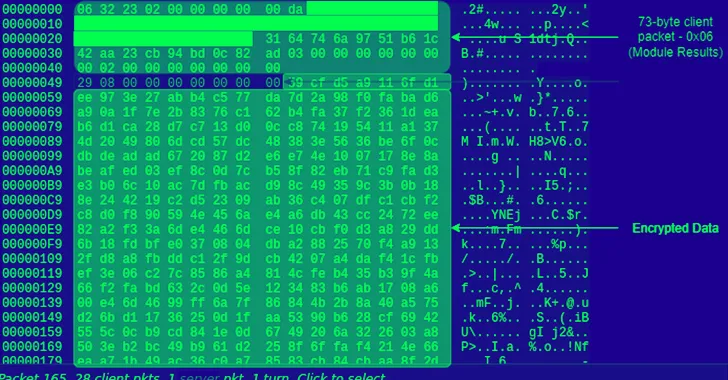
“The client initiates conversation to the C2,” Proofpoint mentioned. “Irrespective of the command, and additional data transmitted, the very first packet is often 73 bytes.”
ZenRAT is also configured to transmit its logs to the server in plaintext, which captures a sequence of process checks carried out by the malware and the status of the execution of each individual module, indicating its use as a “modular, extendable implant.”
To mitigate this kind of threats, it truly is suggested that end users download program only from dependable sources and assure the authenticity of the internet websites.
The disclosure comes as the info stealer known as Lumma Stealer has been observed compromising manufacturing, retail, and enterprise industries considering that the commencing of August 2023.
“The infostealer was sent by using push-by downloads disguised as pretend installers this sort of as Chrome and Edge browser installers, and some of them were being dispersed by way of PrivateLoader,” eSentire explained earlier this thirty day period.
In a linked campaign, rogue web-sites impersonating Google Enterprise Profile and Google Sheets had been found to trick users into putting in a stealer malware dubbed Stealc under the pretext of a security update.
“Drive-by downloads go on to be a widespread system to distribute malware, these types of as facts stealers and loaders,” the Canadian cybersecurity firm pointed out.
Located this article appealing? Adhere to us on Twitter and LinkedIn to go through a lot more special articles we submit.
Some elements of this posting are sourced from:
thehackernews.com

 New libwebp Vulnerability Under Active Exploitation – Gets Maximum CVSS Score
New libwebp Vulnerability Under Active Exploitation – Gets Maximum CVSS Score