A new Mirai-dependent botnet referred to as NoaBot is getting applied by danger actors as section of a crypto mining campaign because the starting of 2023.
“The abilities of the new botnet, NoaBot, involve a wormable self-spreader and an SSH vital backdoor to obtain and execute additional binaries or distribute by itself to new victims,” Akamai security researcher Stiv Kupchik stated in a report shared with The Hacker News.
Mirai, which experienced its source code leaked in 2016, has been the progenitor of a number of botnets, the most latest getting InfectedSlurs, which is able of mounting dispersed denial-of-company (DDoS) attacks.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
There are indications that NoaBot could be joined to an additional botnet campaign involving a Rust-centered malware relatives recognized as P2PInfect, which lately acquired an update to concentrate on routers and IoT products.

This is primarily based on the simple fact that danger actors have also experimented with dropping P2PInfect in location of NoaBot in modern attacks focusing on SSH servers, indicating very likely makes an attempt to pivot to tailor made malware.
Despite NaoBot’s Mirai foundations, its spreader module leverages an SSH scanner to research for servers inclined to dictionary attack in order to brute-force them and add an SSH general public key in the .ssh/authorized_keys file for remote accessibility. Optionally, it can also obtain and execute further binaries post prosperous exploitation or propagate itself to new victims.
“NoaBot is compiled with uClibc, which looks to alter how antivirus engines detect the malware,” Kupchik famous. “Even though other Mirai variants are commonly detected with a Mirai signature, NoaBot’s antivirus signatures are of an SSH scanner or a generic trojan.”
Apart from incorporating obfuscation ways to render analysis tough, the attack chain ultimately effects in the deployment of a modified model of the XMRig coin miner.
What tends to make the new variant a slice above other similar Mirai botnet-based strategies is that it does not consist of any information and facts about the mining pool or the wallet tackle, therefore making it difficult to evaluate the profitability of the illicit cryptocurrency mining scheme.

“The miner obfuscates its configuration and also employs a custom made mining pool to prevent exposing the wallet handle employed by the miner,” Kupchik explained, highlighting some degree of preparedness of the danger actors.
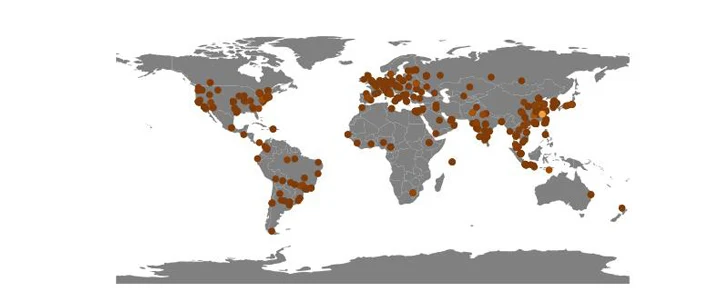
Akamai mentioned it discovered 849 victim IP addresses to day that are distribute geographically throughout the planet, with substantial concentrations claimed in China, so significantly so that it amounts to virtually 10% of all attacks versus its honeypots in 2023.
“The malware’s technique of lateral motion is by using plain outdated SSH credentials dictionary attacks,” Kupchik mentioned. “Restricting arbitrary internet SSH entry to your network drastically diminishes the challenges of an infection. In addition, employing solid (not default or randomly generated) passwords also will make your network extra secure, as the malware utilizes a standard listing of guessable passwords.”
Located this posting attention-grabbing? Comply with us on Twitter and LinkedIn to read through a lot more distinctive information we put up.
Some areas of this post are sourced from:
thehackernews.com


 Getting off the Attack Surface Hamster Wheel: Identity Can Help
Getting off the Attack Surface Hamster Wheel: Identity Can Help