In a new joint cybersecurity advisory, U.S. cybersecurity and intelligence agencies have warned about the use of Maui ransomware by North Korean governing administration-backed hackers to concentrate on the health care sector since at least Might 2021.
“North Korean point out-sponsored cyber actors applied Maui ransomware in these incidents to encrypt servers dependable for healthcare services—including electronic wellness documents providers, diagnostics expert services, imaging providers, and intranet companies,” the authorities mentioned.
The inform arrives courtesy of the U.S. Cybersecurity and Infrastructure Security Agency (CISA), the Federal Bureau of Investigation (FBI), and the Division of the Treasury.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Cybersecurity business Stairwell, whose results shaped the foundation of the advisory, said the lesser-recognized ransomware family stands out simply because of a deficiency of a number of crucial attributes usually connected with ransomware-as-a-services (RaaS) teams.
This contains the absence of “embedded ransom take note to provide recovery instructions or automatic suggests of transmitting encryption keys to attackers,” security researcher Silas Cutler stated in a technical overview of the ransomware.
In its place, investigation of Maui samples suggests that the malware is built for guide execution by a remote actor by means of a command-line interface, using it to goal unique information on the contaminated machine for encryption.
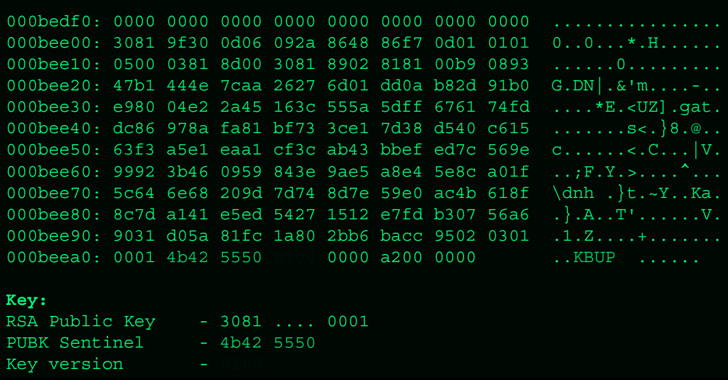
Apart from encrypting target information with AES 128-bit encryption with a exclusive important, every single of these keys is, in transform, encrypted with RSA employing a important pair produced the initially time when Maui is executed. As a third layer of security, the RSA keys are encrypted utilizing a difficult-coded RSA public essential that’s unique to each marketing campaign.
What sets Maui aside from other regular ransomware choices is also the simple fact that it is not supplied as a services to other affiliates for use in return for a share of monetary income.
In some occasions, the ransomware incidents are stated to have disrupted health and fitness expert services for extended periods of time. The first infection vector made use of to carry out the intrusions is unidentified as nevertheless.
It can be value noting that the marketing campaign is predicated on the willingness of healthcare entities to pay ransoms to immediately recover from an attack and assure uninterrupted entry to critical companies. It is really the most recent indicator of how North Korean adversaries are adapting their methods to illegally crank out a frequent stream of earnings for the cash-strapped country.

According to the Sophos’ State of Ransomware in Healthcare 2022 report, 61% of health care businesses surveyed opted to settle as opposed with the global typical of 46%, with only 2% of those that paid out the ransom in 2021 having their full knowledge again.
That said, the use of a manually operated ransomware family members by an APT group also raises the probability that the operation could be a diversionary tactic created to act as a protect for other malicious motives, as lately observed in the case of Bronze Starlight.
“Nation point out-sponsored ransomware attacks have turn into usual intercontinental functions of aggression,” Peter Martini, co-founder of iboss, explained in a assertion. “Regrettably, North Korea exclusively has revealed it is quite prepared to indiscriminately target several industries, which includes health care, to protected untraceable cryptocurrency that is funding its nuclear weapons application.”
Found this post fascinating? Stick to THN on Facebook, Twitter and LinkedIn to examine additional special content we put up.
Some pieces of this posting are sourced from:
thehackernews.com

 Why are ransomware gangs pivoting to Rust?
Why are ransomware gangs pivoting to Rust?