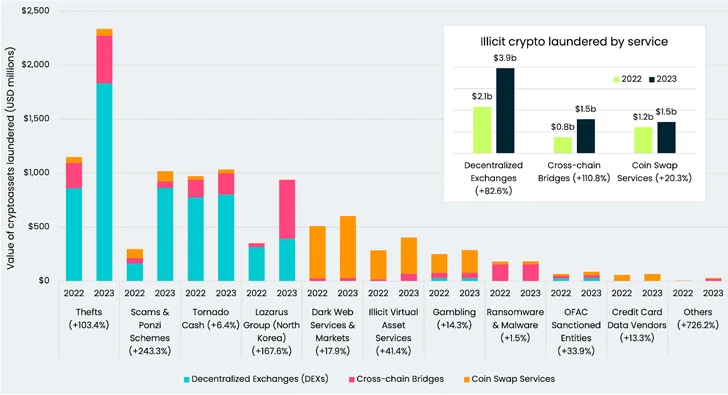
As substantially as $7 billion in cryptocurrency has been illicitly laundered by cross-chain crime, with the North Korea-connected Lazarus Team joined to the theft of approximately $900 million of all those proceeds between July 2022 and July of this 12 months.
“As traditional entities such as mixers carry on to be subject matter to seizures and sanctions scrutiny, the crypto crime displacement to chain- or asset-hopping typologies is also on the increase,” blockchain analytics firm Elliptic stated in a new report released this week.
Cross-chain crime refers to the conversion of crypto assets from just one token or blockchain to a different, usually in speedy succession, in an attempt to obfuscate their origin, creating it a profitable system for money laundering for crypto thefts and an option to Acc techniques like mixers.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
According to details collected by Elliptic, the Lazarus Group’s use of cross-chain bridges contributed to a the vast majority of the 111% maximize in the proportion of resources despatched through these solutions.

The North Korean hacking crew is estimated to have stolen virtually $240 million in cryptocurrency considering that June 2023, next a series of attacks concentrating on Atomic Wallet ($100 million), CoinsPaid ($37.3 million), Alphapo ($60 million), Stake.com ($41 million), and CoinEx ($31 million).
“The range, number, and eccentricity in implementation of Lazarus strategies define this group, as well as that it performs all three pillars of cybercriminal activities: cyber espionage, cyber sabotage, and pursuit of money obtain,” ESET explained of the danger actor late final thirty day period.
The danger actor has also been joined to the use of Avalanche Bridge to deposit extra than 9,500 bitcoin, whilst simultaneously employing cross-chain methods to go some of the plundered assets.

“As is evidenced by the assets ending up on the same blockchain on numerous situations, these transactions have no genuine business reason other than to obfuscate their origin,” Elliptic reported. “Bridging again-and-forth for the sake of obfuscation – i.e. ‘chain-hopping’ – is now a identified cash laundering typology.”
The disclosure arrives as South Korea’s National Intelligence Company (NIS) has warned of North Korea attacking its shipbuilding sector due to the fact the start off of the 12 months.
“The hacking methods predominantly applied by North Korean hacking organizations were to occupy and bypass the PCs of IT servicing providers, and to set up malicious code after distributing phishing emails to internal personnel,” the agency reported.
Identified this article exciting? Comply with us on Twitter and LinkedIn to read extra special material we write-up.
Some parts of this posting are sourced from:
thehackernews.com


