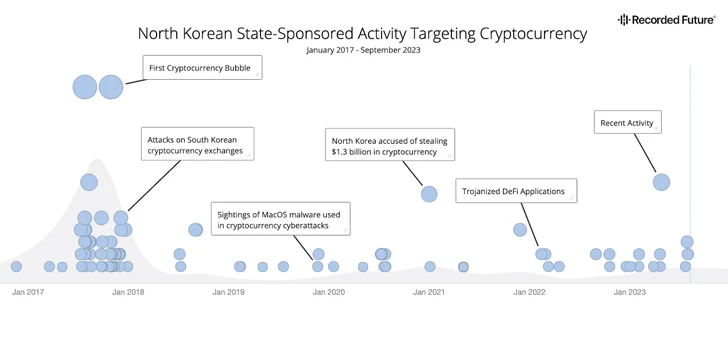
Risk actors from the Democratic People’s Republic of Korea (DPRK) are increasingly concentrating on the cryptocurrency sector as a significant profits era system since at minimum 2017 to get about sanctions imposed versus the state.
“Even although movement in and out of and within just the place is heavily restricted, and its common population is isolated from the relaxation of the earth, the regime’s ruling elite and its extremely trained cadre of computer science experts have privileged access to new technologies and facts,” cybersecurity firm Recorded Long term reported in a report shared with The Hacker Information.
“The privileged obtain to means, technologies, information, and from time to time international journey for a compact set of picked people with guarantee in mathematics and laptop science equips them with the necessary expertise for conducting cyber attacks against the cryptocurrency business.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The disclosure comes as the U.S. Treasury Office imposed sanctions towards Sinbad, a digital currency mixer that has been set to use by the North Korea-linked Lazarus Team to launder unwell-gotten proceeds.

The risk actors from the place are estimated to have stolen $3 billion value of crypto property about the previous six several years, with about $1.7 billion plundered in 2022 alone. A majority of these stolen belongings are utilized to instantly fund the hermit kingdom’s weapons of mass destruction (WMD) and ballistic missile plans.
“$1.1 billion of that whole was stolen in hacks of DeFi protocols, generating North Korea one of the driving forces guiding the DeFi hacking craze that intensified in 2022,” Chainalysis mentioned before this February.
A report printed by the U.S. Office of Homeland Security (DHS) as component of its Analytic Trade Application (AEP) previously this September also highlighted the Lazarus Group’s exploitation of DeFi protocols.
“DeFi trade platforms make it possible for users to changeover between cryptocurrencies without the need of the platform at any time getting custody of the customer’s money in purchase to facilitate the transition,” the report mentioned. “This will allow DPRK cyber actors to decide just when to changeover stolen cryptocurrency from 1 type of cryptocurrency to a different, enabling attribution to be more challenging to decide or even trace.”
The cryptocurrency sector is amongst the top targets for point out-sponsored North Korean cyber menace actors, as frequently evidenced by the myriad strategies carried out in modern months.

DPRK hackers are known for adeptly pulling off social engineering tips to concentrate on workers of on line cryptocurrency exchanges and then lure their victims with the promise of lucrative careers to distribute malware that grants distant obtain to the company’s network, eventually allowing them to drain all accessible property and go them to different DPRK managed wallets.
Other strategies have used equivalent phishing techniques to entice users into downloading trojanized cryptocurrency applications to steal their assets as properly as watering hole attacks (aka strategic web compromises) as an first accessibility vector, together with engaging in airdrop scams and rug pulls.
A further noteworthy tactic adopted by the team is use of mixing services to conceal the economical path and cloud attribution attempts. This sort of expert services are generally offered on cryptocurrency exchange platforms that do not utilize know your consumer (KYC) policies or anti-money laundering (AML) laws.
“Absent more powerful laws, cybersecurity specifications, and investments in cybersecurity for cryptocurrency firms, we evaluate that in the close to time period, North Korea will nearly undoubtedly continue to concentrate on the cryptocurrency business due to its earlier good results in mining it as a resource of added profits to help the routine,” Recorded Foreseeable future concluded.
Located this article intriguing? Stick to us on Twitter and LinkedIn to read through far more exclusive information we post.
Some elements of this article are sourced from:
thehackernews.com

 7 Uses for Generative AI to Enhance Security Operations
7 Uses for Generative AI to Enhance Security Operations