Cybersecurity researchers today disclosed quite a few security issues in popular on the internet relationship platform OkCupid that could likely allow attackers remotely spy on users’ private information and facts or perform malicious actions on behalf of the targeted accounts.
According to a report shared with The Hacker News, researchers from Examine Stage observed that the flaws in OkCupid’s Android and web apps could permit the theft of users’ authentication tokens, buyers IDs, and other sensitive facts this sort of as email addresses, choices, sexual orientation, and other non-public data.
After Test Position scientists responsibly shared their results with OkCupid, the Match Team-owned firm set the issues, stating, “not a solitary user was impacted by the possible vulnerability.”
The Chain of Flaws
The flaws have been recognized as aspect of reverse engineering of OkCupid’s Android application version 40.3.1, which was produced on April 29 previously this yr. Considering that then, there have been 15 updates to the application with the most the latest edition (43.3.2) hitting Google Participate in Store yesterday.
Examine Place stated OkCupid’s use of deep back links could help a terrible actor to ship a personalized connection outlined in the app’s manifest file to open a browser window with JavaScript enabled. Any such request was discovered to return the users’ cookies.
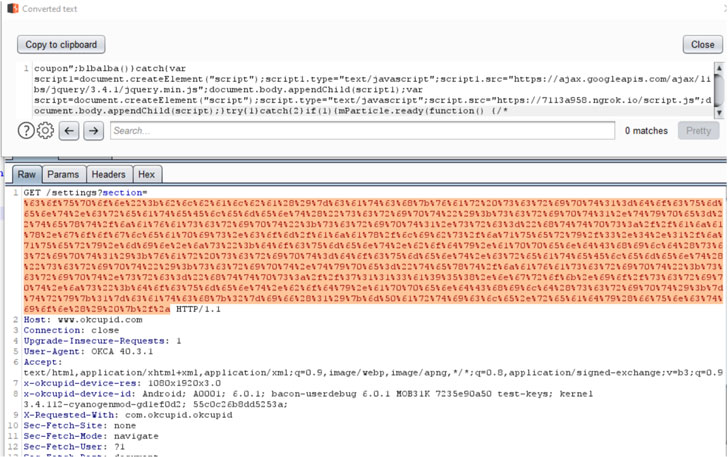
The scientists also uncovered a independent flaw in OkCupid’s settings performance that will make it susceptible to an XSS assault by injecting destructive JavaScript code working with the “section” parameter as follows: “https://www.okcupid.com/configurations?area=price”
The aforementioned XSS attack can be augmented even further by loading a JavaScript payload from an attacker-managed server to steal authentication tokens, profile information and facts, and user tastes, and transmit the amassed information back again to the server.
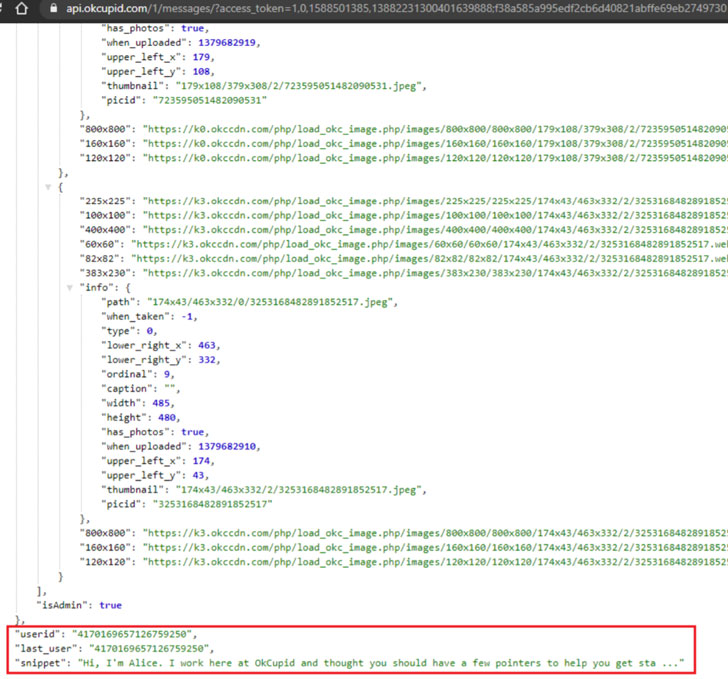
“Users’ cookies are sent to the [OkCupid] server considering that the XSS payload is executed in the context of the application’s WebView,” the researchers claimed, outlining their process to capture the token information and facts. “The server responds with a vast JSON containing the users’ id and the authentication token.”
Once in possession of the person ID and the token, an adversary can ship a request to the “https://www.OkCupid.com:443/graphql” endpoint to fetch all the information and facts involved with the victim’s profile (email address, sexual orientation, peak, relatives standing, and other private tastes) as perfectly as have out actions on behalf of the compromised specific, these as send out messages and alter profile information.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Having said that, a entire account hijack is not achievable as the cookies are shielded with HTTPOnly, mitigating the chance of a customer-side script accessing the secured cookie.
Last of all, an oversight in the Cross-Origin Resource Sharing (CORS) coverage of the API server could have permitted an attacker to craft requests from any origin (e.g. “https://okcupidmeethehacker.com”) in get to get keep of the person ID and authentication token, and subsequently, use that details to extract profile facts and messages utilizing the API’s “profile” and “messages” endpoints.
Keep in mind Ashley Madison Breach and Blackmail Threats?
Though the vulnerabilities ended up not exploited in the wild, the episode is nevertheless a further reminder of how terrible actors could have taken gain of the flaws to threaten victims with black and extortion.
Following Ashley Madison, an grownup dating assistance catering to married people today seeking partners for affairs was hacked in 2015 and details about its 32 million consumers was posted to the dark web, it led to a increase in phishing and sextortion strategies, with blackmailers reportedly sending personalised e-mail to the consumers, threatening to reveal their membership to close friends and household unless they shell out money.
“The dire want for privateness and data security results in being much far more vital when so considerably non-public and personal facts is remaining saved, managed and analyzed in an application,” the researchers concluded. “The app and system was made to deliver individuals collectively, but of program exactly where people go, criminals will comply with, hunting for effortless pickings.”
Uncovered this post interesting? Abide by THN on Fb, Twitter and LinkedIn to browse far more special content we post.


 Worldwide Corporations Delayed Essential Security Assignments as Pandemic Struck
Worldwide Corporations Delayed Essential Security Assignments as Pandemic Struck