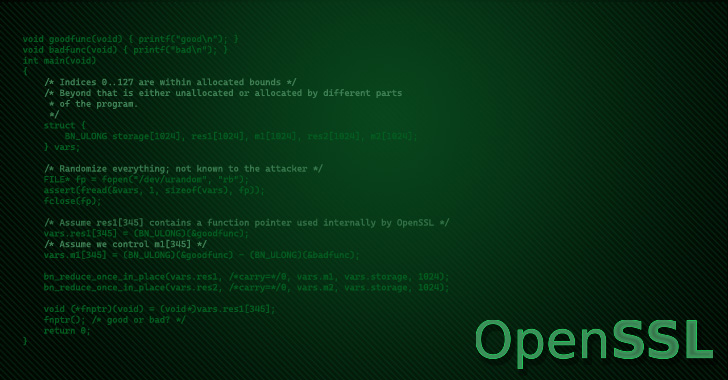
The hottest edition of the OpenSSL library has been discovered as prone to a distant memory-corruption vulnerability on pick methods.
The issue has been identified in OpenSSL variation 3..4, which was introduced on June 21, 2022, and impacts x64 techniques with the AVX-512 instruction set. OpenSSL 1.1.1 as very well as OpenSSL forks BoringSSL and LibreSSL are not influenced.
Security researcher Guido Vranken, who documented the bug at the close of May perhaps, mentioned it “can be activated trivially by an attacker.” Despite the fact that the shortcoming has been mounted, no patches have been manufactured offered as still.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
OpenSSL is a common cryptography library that offers an open supply implementation of the Transportation Layer Security (TLS) protocol. Advanced Vector Extensions (AVX) are extensions to the x86 instruction established architecture for microprocessors from Intel and AMD.
“I do not imagine this is a security vulnerability,” Tomáš Mráz of the OpenSSL Basis mentioned in a GitHub issue thread. “It is just a really serious bug earning the 3..4 launch unusable on AVX-512 capable devices.”

On the other hand, Alex Gaynor pointed out, “I am not certain I understand how it really is not a security vulnerability. It truly is a heap buffer overflow that is triggerable by matters like RSA signatures, which can effortlessly materialize in remote contexts (e.g. a TLS handshake).”
Xi Ruoyao, a postgraduate university student at Xidian College, chimed in, stating that while “I feel we should not mark a bug as ‘security vulnerability’ except if we have some evidence showing it can (or at minimum, may well) be exploited,” it really is needed to launch variation 3..5 as before long as achievable given the severity of the issue.
Located this short article attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to go through extra distinctive written content we submit.
Some components of this short article are sourced from:
thehackernews.com

 New Android Banking Trojan ‘Revive’ Targeting Users of Spanish Financial Services
New Android Banking Trojan ‘Revive’ Targeting Users of Spanish Financial Services