Danger actors affiliated with the hacking crew recognised as Patchwork have been noticed concentrating on universities and investigate organizations in China as element of a recently noticed campaign.
The exercise, in accordance to KnownSec 404 Crew, entailed the use of a backdoor codenamed EyeShell.
Patchwork, also recognised by the names Operation Hangover and Zinc Emerson, is suspected to be a danger team that operates on behalf of India. Lively since at least December 2015, attack chains mounted by the group have a narrow concentrate and are likely to solitary out Pakistan and China with custom implants these kinds of as BADNEWS through spear-phishing and watering hole attacks.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The adversarial collective has been found to share tactical overlaps with other cyber-espionage groups with an Indian link, including SideWinder and the DoNot Crew.
Before this May possibly, Meta disclosed that it took down 50 accounts on Fb and Instagram operated by Patchwork, which took gain of rogue messaging applications uploaded to the Google Enjoy Store to gather details from victims in Pakistan, India, Bangladesh, Sri Lanka, Tibet, and China.
“Patchwork relied on a range of elaborate fictitious personas to socially engineer people today into clicking on destructive back links and downloading malicious applications,” the social media large mentioned.
“These apps contained fairly primary destructive operation with the entry to person info exclusively reliant on legitimate app permissions granted by the conclusion person. Notably, Patchwork produced a faux overview web site for chat applications where they listed the top five communication applications, placing their own, attacker-controlled application at the prime of the listing.”
Some of its pursuits have also been claimed less than the title ModifiedElephant, in accordance to Secureworks, referring to a established of attacks towards human rights activists, lecturers, and legal professionals throughout India to perform extensive-time period surveillance and plant “incriminating digital evidence” in relationship with the 2018 Bhima Koregaon violence in the Indian state of Maharashtra.
Upcoming WEBINARShield From Insider Threats: Learn SaaS Security Posture Administration
Fearful about insider threats? We have obtained you protected! Be part of this webinar to examine useful procedures and the secrets of proactive security with SaaS Security Posture Management.
Join Now
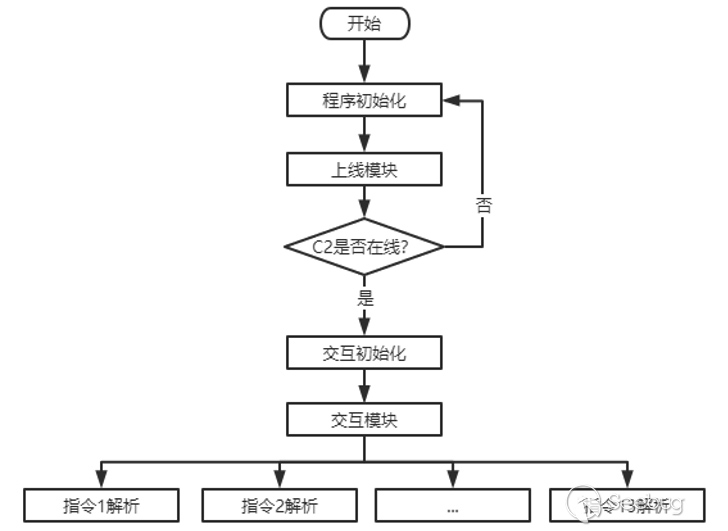
EyeShell, detected along with BADNEWS, is a a .NET-centered modular backdoor that comes with capabilities to establish call with a distant command-and-regulate (C2) server and execute instructions to enumerate data files and directories, downloading and uploading information to and from the host, execute a specified file, delete data files, and capture screenshots.
The findings occur as the cybersecurity organization also in-depth a further wave of phishing attacks orchestrated by a group named Bitter aimed at aerospace, navy, substantial enterprises, countrywide government affairs, and universities in the country with a new backdoor recognized as ORPCBackdoor.
The South Asian danger actor was formerly detected targeting the nuclear power sector in China with malware downloaders delivered by means of CHM and Microsoft Excel Data files that are developed to create persistence and retrieve additional payloads.
Uncovered this write-up attention-grabbing? Abide by us on Twitter and LinkedIn to examine a lot more unique content material we publish.
Some parts of this posting are sourced from:
thehackernews.com


 Webinar: Riding the vCISO Wave: How to Provide vCISO Services
Webinar: Riding the vCISO Wave: How to Provide vCISO Services