U.S. cybersecurity and intelligence agencies have warned of Phobos ransomware attacks concentrating on federal government and critical infrastructure entities, outlining the different ways and tactics the threat actors have adopted to deploy the file-encrypting malware.
“Structured as a ransomware as a service (RaaS) design, Phobos ransomware actors have focused entities like municipal and county governments, unexpected emergency expert services, schooling, public healthcare, and critical infrastructure to properly ransom a number of million in U.S. pounds,” the governing administration claimed.
The advisory will come from the U.S. Cybersecurity and Infrastructure Security Agency (CISA), the Federal Bureau of Investigation (FBI), and the Multi-Point out Information and facts Sharing and Examination Center (MS-ISAC).

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Active considering that May perhaps 2019, many variants of Phobos ransomware have been determined to day, specifically Eking, 8, Elbie, Devos, Faust, and Backmydata. Late previous year, Cisco Talos discovered that the risk actors at the rear of the 8Base ransomware are leveraging a Phobos ransomware variant to carry out their economically motivated attacks.
There is proof to recommend that Phobos is possible closely managed by a central authority, which controls the ransomware’s private decryption critical.
Attack chains involving the ransomware pressure have usually leveraged phishing as an preliminary entry vector to drop stealthy payloads like SmokeLoader. Alternatively, vulnerable networks are breached by looking for exposed RDP services and exploiting them by suggests of a brute-drive attack.

A profitable digital break-in is followed by the menace actors dropping more distant access instruments, having benefit of method injection approaches to execute malicious code and evade detection, and earning Windows Registry modifications to maintain persistence in compromised environments.
“Furthermore, Phobos actors have been noticed employing designed-in Windows API functions to steal tokens, bypass entry controls, and generate new processes to escalate privileges by leveraging the SeDebugPrivilege approach,” the agencies stated. “Phobos actors endeavor to authenticate utilizing cached password hashes on sufferer devices until eventually they arrive at area administrator access.”
The e-crime group is also identified to use open-supply instruments these kinds of as Bloodhound and Sharphound to enumerate the energetic directory. File exfiltration is attained by using WinSCP and Mega.io, right after which volume shadow copies are deleted in an attempt to make recovery tougher.
The disclosure will come as Bitdefender comprehensive a meticulously coordinated ransomware attack impacting two independent firms at the exact same time. The attack, described as synchronized and multifaceted, has been attributed to a ransomware actor named CACTUS.
“CACTUS continued infiltrating the network of just one business, implanting several kinds of distant entry resources and tunnels across different servers,” Martin Zugec, technical methods director at Bitdefender, mentioned in a report printed previous 7 days.
“When they discovered an opportunity to transfer to another company, they momentarily paused their operation to infiltrate the other network. Each businesses are component of the identical team, but run independently, protecting independent networks and domains with out any set up have faith in relationship.”
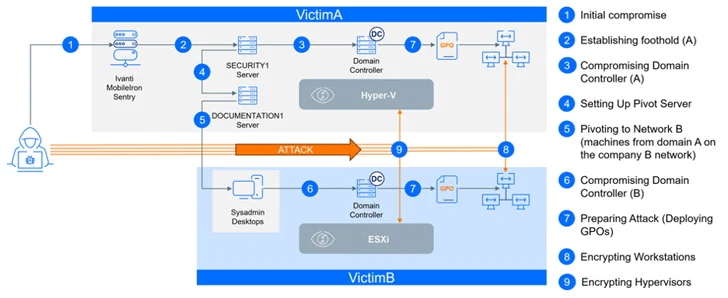
The attack is also notable for the focusing on of the unnamed firm’s virtualization infrastructure, indicating that CACTUS actors have broadened their focus further than Windows hosts to strike Hyper-V and VMware ESXi hosts.
It also leveraged a critical security flaw (CVE-2023-38035, CVSS score: 9.8) in an internet-uncovered Ivanti Sentry server fewer than 24 several hours after its initial disclosure in August 2023, when once more highlighting opportunistic and swift weaponization of freshly revealed vulnerabilities.

Ransomware proceeds to be a key income spinner for fiscally enthusiastic risk actors, with first ransomware calls for reaching a median of $600,000 in 2023, a 20% leap from the earlier 12 months, in accordance to Arctic Wolf. As of Q4 2023, the common ransom payment stands at $568,705 for each sufferer.
What is actually more, shelling out a ransom demand does not quantity to future safety. There is no assure that a victim’s info and techniques will be securely recovered and that the attackers won’t promote the stolen data on underground message boards or attack them once again.
Facts shared by cybersecurity company Cybereason exhibits that “a staggering 78% [of organizations] were being attacked all over again just after paying out the ransom – 82% of them in a calendar year,” in some circumstances by the similar threat actor. Of these victims, 63% ended up “asked to fork out additional the next time.”
Observed this article exciting? Abide by us on Twitter and LinkedIn to read through more distinctive content we article.
Some elements of this short article are sourced from:
thehackernews.com


 U.S. Court Orders NSO Group to Hand Over Pegasus Spyware Code to WhatsApp
U.S. Court Orders NSO Group to Hand Over Pegasus Spyware Code to WhatsApp