Getty Photographs
Rackspace has exposed the Participate in ransomware gang was at the rear of a December attack which took down the company’s hosted Microsoft Exchange email assistance.
In a status update published on Thursday evening, the cloud computing business verified the ransomware team obtained accessibility to Particular Storage Tables (PST) belonging to 27 hosted exchange shoppers.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Rackspace insisted that, at current, there is no evidence to recommend that danger actors “viewed, acquired, misused, or disseminated” email messages or information belonging to the hosted trade prospects.
“No other Rackspace solutions, platforms, answers, or corporations were being affected or professional downtime due to this incident,” the organization said.
At the time of Rackspace’s update, the business disclosed that “more than half” of impacted clients have experienced “some or all of their info out there to them to download”.
“This signifies to us that a lot of of our prospects have facts backed up domestically, archived, or if not do not need the historic info,” the enterprise reported.
“We will continue operating to get better all data attainable as prepared, having said that, in parallel, we are acquiring an on-desire option for those people buyers who do nonetheless would like to down load their info. We hope that the on-demand resolution will be available inside of two weeks.”
Rackspace extra that the hosted Exchange company will not return following the incident.
Rackspace cyber attack
Rackspace initially informed consumers that it had endured a breach on 2 December. The attack brought about an outage on the firm’s hosted Microsoft Exchange email support, disrupting affected buyers who ended up left unable to access email products and services and get better contacts or former correspondence.
A adhere to-up disclosure by the organization confirmed that a ransomware attack was to blame for the incident, and subsequently commenced migrating customers to cloud-primarily based Microsoft 365 providers.
First speculation recommended that the incident was the result of the ProxyNotShell exploit, Rackspace reported. Nevertheless, the company mentioned it can now “definitively state” that this is not exact.
An investigation by CrowdStrike located that Engage in harnessed a zero-day exploit associated with CVE-2022-41080, recognized as ‘OWASSRF’, as part of the attack.
The OWASSRF zero-day exploits two vulnerabilities, tracked as CVE-2022-41080 and CVE-2022-41082, and allows menace actors to attain distant code execution (RCE) through Outlook Web Access.
According to CrowdStrike, this strategy “bypasses URL rewrite mitigations for the Autodiscover endpoint offered by Microsoft in reaction to ProxyNotShell”.
“Microsoft disclosed CVE-2022-41080 as a privilege escalation vulnerability and did not contain notes for getting aspect of a distant code execution chain that was exploitable,” Rackspace added in its update.
CrowdStrike mentioned it uncovered this new exploit on the back of an intensive investigation into current Enjoy ransomware attacks that focused Microsoft Trade.
What is Participate in ransomware?
The Engage in ransomware group is a relative newcomer to the worldwide cyber criminal offense room. Also identified as PlayCrypt, the group is thought to have introduced in June 2022 and has already induced sizeable disruption to a host of important organisations.
The team earlier claimed accountability for an attack on German resort chain, H-Lodges, and before this week the group stated it was accountable for an attack on the Point out of New York (SUNY) Polytechnic.
The attack is believed to be the first key ransomware attack on the schooling sector so much in 2023, and led to the publicity of sensitive knowledge this kind of as passport information, confidential contracts, and pupil IDs.
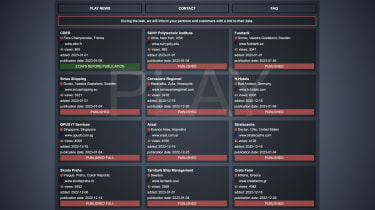
IT Pro
According to research from Avertium, Enjoy has largely focused organisations throughout Latin America, but has also been observed deploying attacks on India, Hungary, Spain, and the Netherlands.
“Play is recognized for their big video game hunting tactics, this kind of as working with Cobalt Strike for put up-compromise and SystemBC RAT for persistence,” Avertium explained in a blog publish. “They have just lately began exploiting the ProxyNotShell vulnerabilities in Microsoft Exchange.
“The group also has identical techniques and methods to the ransomware groups Hive and Nokoyawa, major researchers to feel Enjoy is operated by the identical people today.”
Some pieces of this short article are sourced from:
www.itpro.co.uk


 Personal Storage Table Files Accessed in Rackspace Attack
Personal Storage Table Files Accessed in Rackspace Attack